Enhancing information security
Vulnerability Countermeasure Information Database JVN iPedia Registration Status [2021 2nd Quarter (Apr. - Jun.)]
Release Date:Aug 25, 2021
IT Security Center
1. 2021 2nd Quarter: Vulnerability Countermeasure Information Database JVN iPedia Registration Status
The vulnerability countermeasure information database JVN iPedia (https://jvndb.jvn.jp/en/) is endeavoring to become a comprehensive vulnerability database where vulnerability information is aggregated for easy access for IT users. JVN iPedia collects and/or translates the vulnerability information published by 1) domestic software developers, 2) JVN (*1), a vulnerability information portal run by JPCERT/CC and IPA, and 3) NVD (*2), a vulnerability database run by NIST (*3). JVN iPedia has been making vulnerability information available to the public since April 25, 2007.
1-1. Vulnerabilities Registered in 2021/2Q
~ JVN iPedia now stores 129,824 vulnerabilities ~
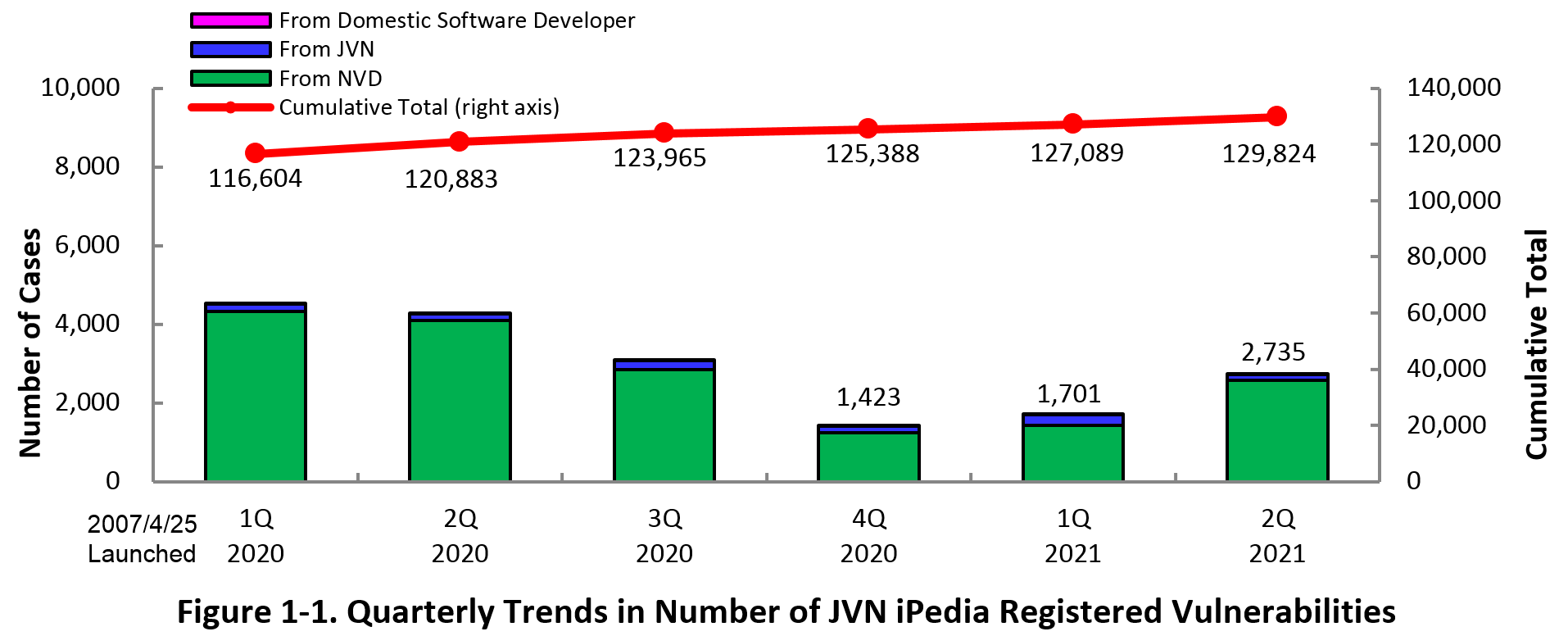
The summary of the vulnerability information registered to the Japanese version of JVN iPedia during the 2nd quarter of 2021 (April 1 to June 30, 2021) is shown in the table below. As of the end of June 2021, the total number of vulnerabilities stored in JVN iPedia is 129,824 (Table 1-1, Figure 1-1).
As for the JVN iPedia English version, the total number of vulnerabilities stored is 2,301 as shown in the lower half of the Table 1-1.
Table 1-1. Vulnerabilities Registered to JVN iPedia during 2nd Quarter of 2021
|
|
Information Source
|
Registered Cases
|
Cumulative Cases
|
|---|---|---|---|
|
Japanese Version
|
Domestic Product Developers
|
3 cases
|
256 cases
|
|
JVN
|
150 cases
|
10,151 cases
|
|
|
NVD
|
2,582 cases
|
119,417 cases
|
|
|
Total
|
2,735 cases
|
129,824 cases
|
|
|
English Version
|
Domestic Product Developers
|
3 cases
|
251 cases
|
|
JVN
|
38 cases
|
2,050 cases
|
|
|
Total
|
41 cases
|
2,301 cases
|
2. Details on JVN iPedia Registered Data
2-1. Types of Vulnerabilities Reported
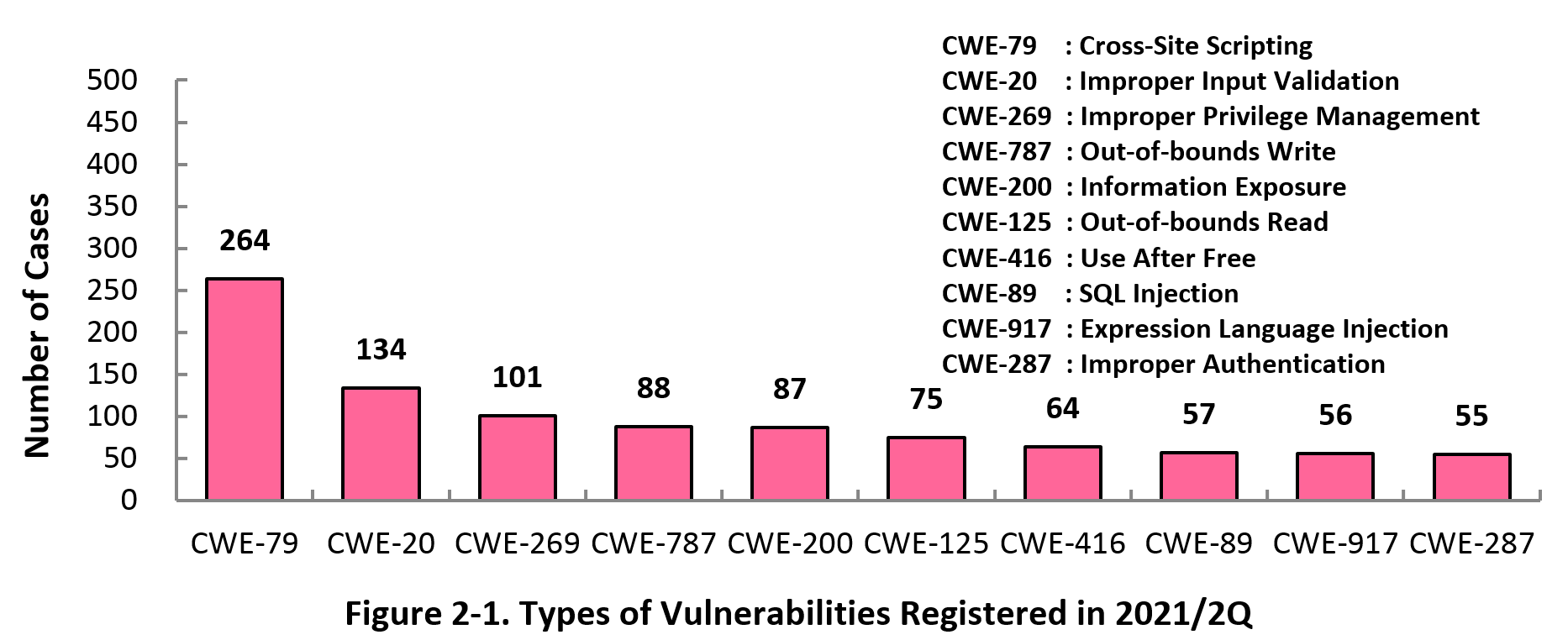
Figure 2-1 shows the number of vulnerabilities newly added to JVN iPedia during the 2nd quarter of 2021, sorted by the CWE vulnerability types.
The type of the vulnerabilities reported most in the 2nd quarter is CWE-79 (Cross-Site Scripting) with 264 cases, followed by CWE-20 (Improper Input Validation) with 134, CWE-269 (Improper Privilege Management) with 101 cases, CWE-787 (Out-of-bounds Write) with 88, CWE-200 (Information Exposure) with 87. CWE-79 (Cross-Site Scripting), the most reported vulnerability type in this quarter, could allow attackers to display false webpages and/or steal information.
Software developers need to make sure to mitigate vulnerability from the planning and design phase of software development. IPA provides tools and guidelines, such as "Vulnerability Countermeasure Guide for Software Developers"" (*4), "How to Secure Your Website" (*5), "Secure Programming Guide" (*6) and "AppGoat" (*7), a hands-on venerability learning tool, for website developers and operators to build secure websites.
2-2. Severity of Vulnerabilities Reported
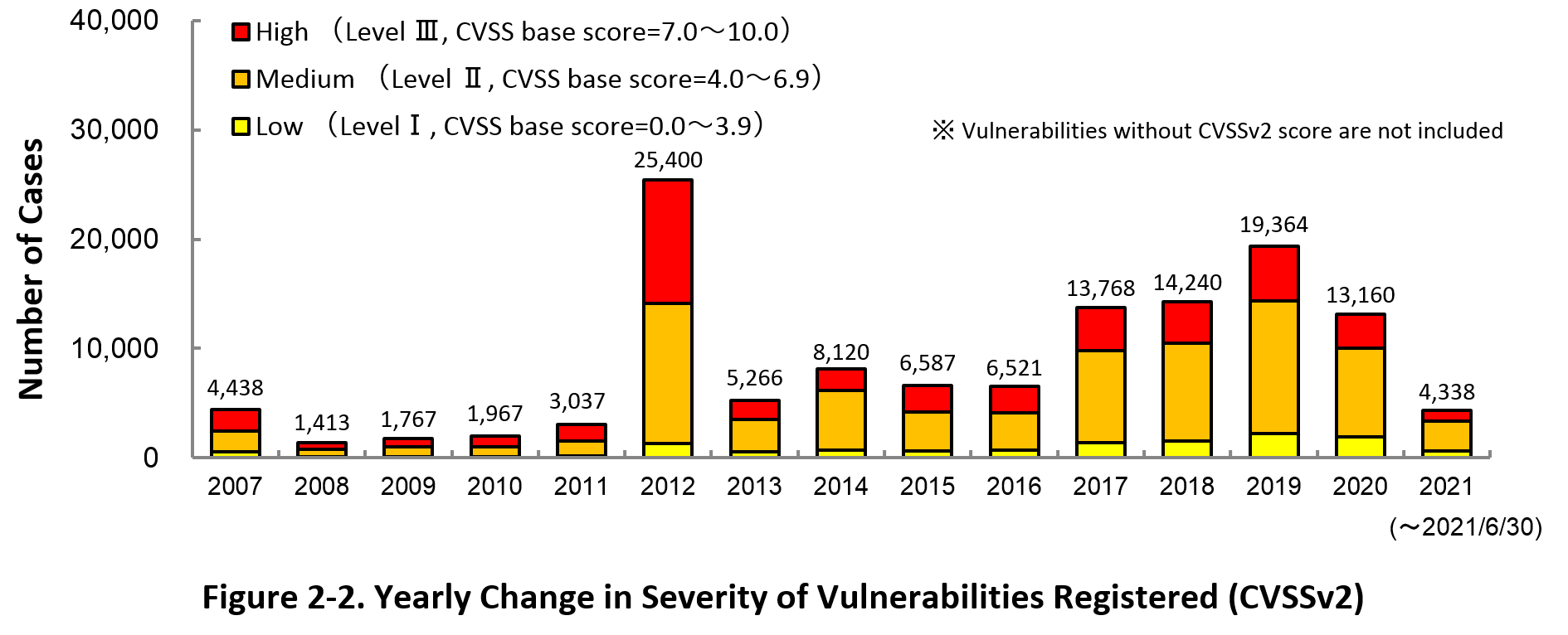
Figure 2-2 shows the yearly change in the CVSSv2 rating scale based severity of vulnerabilities registered to JVN iPedia.
As for the vulnerabilities added to JVN iPedia in 2021, 22.0 percent are “Level III” (7.0 - 10.0), 62.9 percent are “Level ll” (4.0 – 6.9) and 15.1 percent are “Level I” (0.0 – 3.9). This means 84.9 percent of all vulnerabilities registered are Level II or higher, which are potentially critical enough to cause damage like information exposure or data falsification.
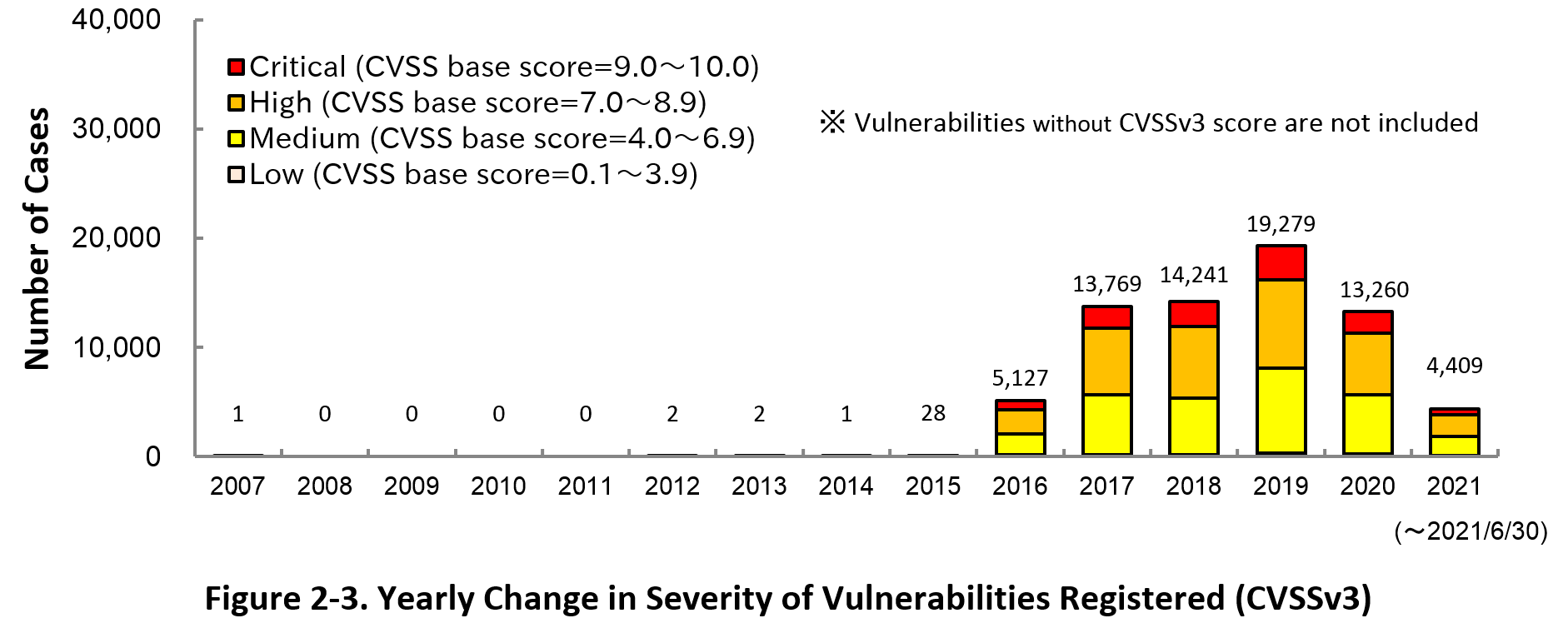
Figure 2-3 shows the yearly change in the CVSSv3 rating scale based severity of vulnerabilities registered to JVN iPedia.
As for the vulnerabilities added to JVN iPedia in 2021, 12.8 percent are “Critical” (9.0 – 10.0), 45.2 percent are “High” (7.0 – 8.9), 39.4 percent are “Medium” (4.0 – 6.9) and 2.6 percent are “Low” (0.1 – 3.9).
To avoid threats posed by the known vulnerabilities, both product developers and IT users should pay close attention to vulnerability disclosure and update software they use to a fixed version or apply a security patch as soon as possible when they become available. IT users can check vulnerabilities newly published on JVN iPedia in RSS and XML format (*8) as well.
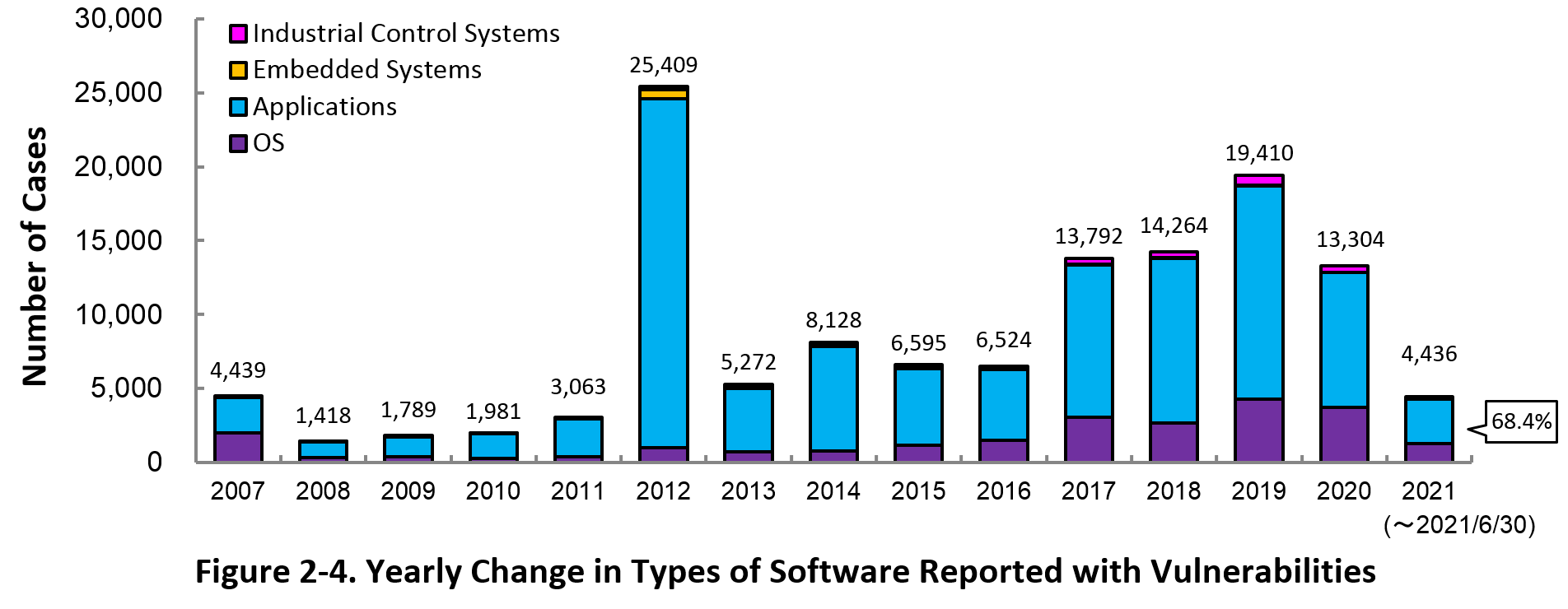
2-3. Types of Software Reported with Vulnerability
Figure 2-4 shows the yearly change in the type of software reported with vulnerability. Application vulnerabilities have been published most, accounting for 68.4 percent (3,034 out of 4,436) of the 2021 total.
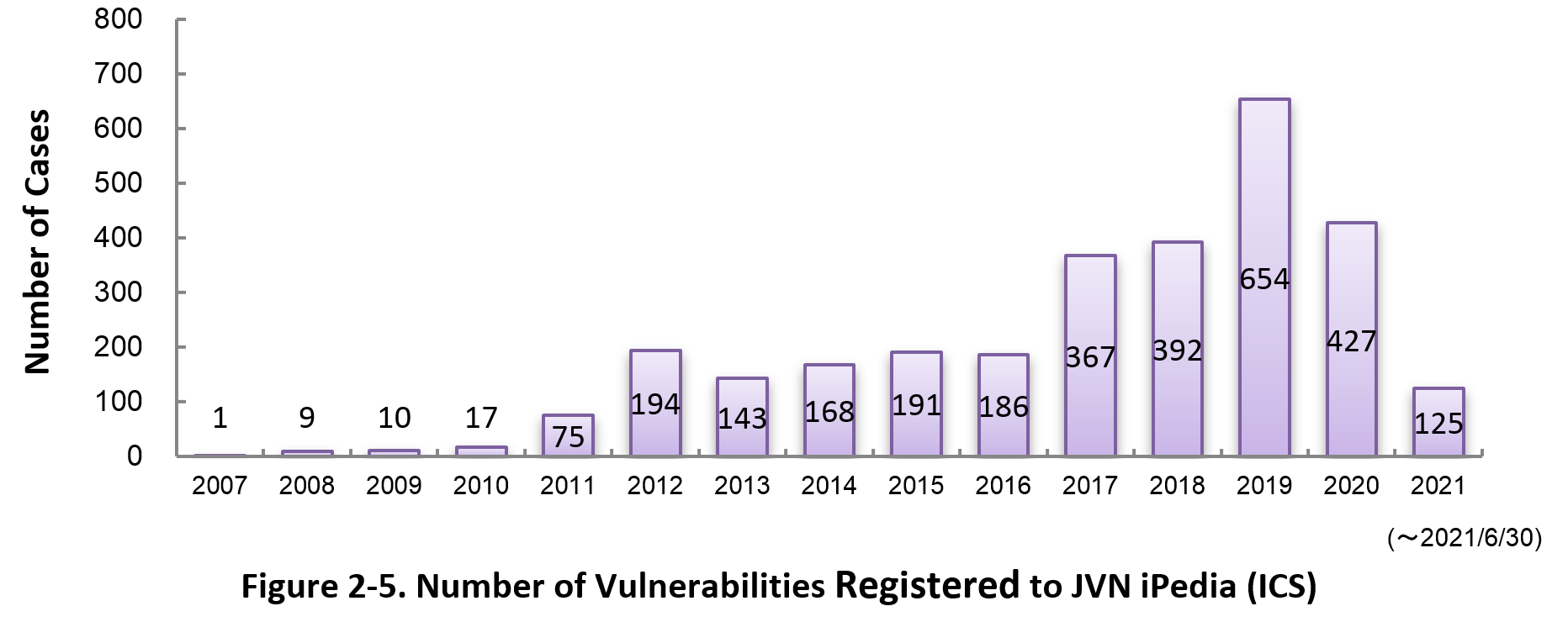
Figure 2-5 shows the yearly change in the number of JVN iPedia-stored vulnerabilities in industrial control systems (ICS) used in critical infrastructure sectors. As of June 2021, the total of 2,959 ICS vulnerabilities have been registered.
2-4. Products Reported with Vulnerability
Table 2-1 lists the top 20 software whose vulnerabilities were most registered to JVN iPedia during the 2nd quarter (April to June) of 2021.
In this quarter, the most registered products were Qualcomm products which continued from previous quarter, with 460 cases. This is due to the registration of vulnerability information for multiple Qualcomm products which published in 2020. In addition, OS products, such as Microsoft Windows Products, account for 14 of the top 20.
Besides those in the top 20 list, JVN iPedia stores and offers vulnerability information about a variety of software. IPA hopes software developers and users will make good use of JVN iPedia to efficiently check vulnerability information and take necessary action in a timely manner (*9).
Table 2-1. Top 20 most registered software products vulnerability countermeasure information in JVN iPedia [Apr. – Jun. 2021]
|
Rank
|
Category
|
Product Name (Vendor)
|
Number of
Vulnerabilities Registered |
|---|---|---|---|
|
1
|
Firmware
|
Qualcomm component (Qualcomm)
|
460
|
|
2
|
OS
|
Fedora (Fedora Project)
|
115
|
|
3
|
OS
|
Debian GNU/Linux (Debian)
|
102
|
|
4
|
Integrated set of business applications
|
Oracle E-Business Suite (Oracle)
|
99
|
|
4
|
OS
|
Microsoft Windows 10 (Microsoft)
|
99
|
|
6
|
OS
|
Microsoft Windows Server (Microsoft)
|
96
|
|
7
|
OS
|
Microsoft Windows Server 2019 (Microsoft)
|
88
|
|
8
|
Middleware
|
MySQL (Oracle)
|
77
|
|
9
|
Browser
|
Google Chrome (Google)
|
74
|
|
10
|
OS
|
Microsoft Windows Server 2016 (Microsoft)
|
70
|
|
11
|
OS
|
Android (Google)
|
67
|
|
12
|
Network management software
|
HPE Intelligent Management Center (Hewlett Packard Enterprise)
|
64
|
|
13
|
OS
|
Microsoft Windows Server 2012 (Microsoft)
|
63
|
|
13
|
Others
|
Backports SLE (openSUSE project)
|
63
|
|
15
|
OS
|
Microsoft Windows 8.1 (Microsoft)
|
62
|
|
16
|
OS
|
Microsoft Windows RT 8.1 (Microsoft)
|
61
|
|
17
|
OS
|
openSUSE Leap (openSUSE project)
|
60
|
|
18
|
OS
|
Microsoft Windows 7 (Microsoft)
|
57
|
|
19
|
OS
|
Microsoft Windows Server 2008 (Microsoft)
|
56
|
|
20
|
OS
|
Cisco IOS XE (Cisco Systems)
|
46
|
3. Most Accessed Vulnerability Countermeasure Information
Table 3-1 lists the top 20 most accessed vulnerability countermeasure information in JVN iPedia during the 2nd quarter of 2021 (April to June).
In this quarter, the most accessed vulnerability countermeasure information was "phpMyAdmin vulnerable to cross-site scripting" published in 2014. This is because there was a lot of access which was considered mechanical from specific organizations. In addition, vulnerability countermeasure information published on the vulnerability countermeasure information portal site JVN accounted for 17 of the top 20.
Rating Scale
Note 1) CVSSv2 Severity Rating Scale
- Level I (Low)
- CVSS Base Score = 0.0~3.9
- Level II (Medium)
- CVSS Base Score = 4.0~6.9
- Level III (High)
- CVSS Base Score = 7.0~10.0
Note 2) CVSSv3 Severity Rating Scale
- Low
- CVSS Base Score =0.1~3.9
- Medium
- CVSS Base Score =4.0~6.9
- High
- CVSS Base Score =7.0~8.9
- Critical
- CVSS Base Score =9.0~10.0
Table 3-1. Top 20 Most Accessed Vulnerability Countermeasure Information in JVN iPedia [Apr. – Jun. 2021]
No.1 phpMyAdmin vulnerable to cross-site scripting JVNDB-2014-003893
- CVSSv2 Severity Rating Scale
-
- Level I (Low)
- CVSSv2 Base Score
-
3.5
- CVSSv3 Base Score
-
-
- Date Public
-
2014/8/25
- Access Count
-
7,948
No.2 Multiple vulnerabilities in Buffalo broadband routers JVNDB-2021-001381
- CVSSv2 Base Score
-
-
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
4.3
- Date Public
-
2021/4/28
- Access Count
-
7,278
No.3 Gurunavi Apps fail to restrict access permissions JVNDB-2021-000031
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
4.3
- CVSSv3 Severity Rating Scale
-
Low
- CVSSv3 Base Score
-
3.3
- Date Public
-
2021/4/14
- Access Count
-
7,257
No.4 Multiple Buffalo network devices contain hidden functionality JVNDB-2021-001380
- CVSSv2 Base Score
-
-
- CVSSv3 Severity Rating Scale
-
High
- CVSSv3 Base Score
-
8.8
- Date Public
-
2021/4/28
- Access Count
-
7,155
No5. WordPress plugin "WP Fastest Cache" vulnerable to directory traversal JVNDB-2021-000034
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
5.5
- CVSSv3 Severity Rating Scale
-
Low
- CVSSv3 Base Score
-
3.8
- Date Public
-
2021/4/27
- Access Count
-
6,593
No.6 Multiple vulnerabilities in Aterm WF1200CR, Aterm WG1200CR, Aterm WG2600HS, and Aterm WX3000HP JVNDB-2021-000030
- CVSSv2 Severity Rating Scale
-
- Level III (High)
- CVSSv2 Base Score
-
8.3
- CVSSv3 Severity Rating Scale
-
- High
- CVSSv3 Base Score
-
8.8
- Date Public
-
2021/4/9
- Access Count
-
6,580
No.7 Archive collectively operation utility vulnerable to directory traversal JVNDB-2021-000029
- CVSSv2 Severity Rating Scale
-
- Level II (Medium)
- CVSSv2 Base Score
-
4.3
- CVSSv3 Severity Rating Scale
-
Low
- CVSSv3 Base Score
-
3.3
- Date Public
-
2021/4/1
- Access Count
-
6,427
No.8 Multiple vulnerabilities in multiple Aterm products JVNDB-2021-000028
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
5.8
- CVSSv3 Severity Rating Scale
-
High
- CVSSv3 Base Score
-
8.8
- Date Public
-
2021/4/9
- Access Count
-
6,323
No.9 Hot Pepper Gourmet App fails to restrict access permissions JVNDB-2021-000033
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
4.3
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
4.3
- Date Public
-
2021/4/27
- Access Count
-
6,264
No.10 mod_auth_openidc vulnerable to denial-of-service (DoS) JVNDB-2021-000037
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
5.0
- CVSSv3 Severity Rating Scale
-
High
- CVSSv3 Base Score
-
7.5
- Date Public
-
2021/5/14
- Access Count
-
5,908
No.11 EC-CUBE vulnerable to cross-site scripting JVNDB-2021-000035
- CVSSv2 Severity Rating Scale
-
- Level II (Medium)
- CVSSv2 Base Score
-
6.8
- CVSSv3 Severity Rating Scale
-
- High
- CVSSv3 Base Score
-
7.1
- Date Public
-
2021/5/10
- Access Count
-
5,792
No.12 Trend Micro Password Manager may insecurely load Dynamic Link Libraries JVNDB-2021-001374
- CVSSv2 Severity Rating Scale
-
- Level II (Medium)
- CVSSv2 Base Score
-
4.4
- CVSSv3 Severity Rating Scale
-
High
- CVSSv3 Base Score
-
7.8
- Date Public
-
2021/4/20
- Access Count
-
5,559
No.13 Information Disclosure Vulnerability in Cosminexus JVNDB-2021-001345
- CVSSv2 Base Score
-
-
- CVSSv3 Base Score
-
-
- Date Public
-
2021/4/13
- Access Count
-
5,475
No.14 Vulnerability in JP1/VERITAS JVNDB-2021-001344
- CVSSv2 Base Score
-
-
- CVSSv3 Base Score
-
-
- Date Public
-
2021/4/13
- Access Count
-
5,471
No.15 yappa-ng vulnerable to cross-site scripting JVNDB-2021-000909
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
4.3
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
6.1
- Date Public
-
2021/4/22
- Access Count
-
5,261
No.16 The installers of ScanSnap Manager may insecurely load Dynamic Link Libraries JVNDB-2021-000041
- CVSSv2 Severity Rating Scale
-
- Level II (Medium)
- CVSSv2 Base Score
-
6.8
- CVSSv3 Severity Rating Scale
-
- High
- CVSSv3 Base Score
-
7.8
- Date Public
-
2021/5/21
- Access Count
-
5,159
No.17 D-Link DAP-1880AC contains multiple vulnerabilities JVNDB-2021-001343
- CVSSv2 Base Score
-
-
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
5.0
- Date Public
-
2021/4/12
- Access Count
-
5,060
No.18 rNote vulnerable to cross-site scripting JVNDB-2021-000908
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
4.3
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
6.1
- Date Public
-
2021/3/25
- Access Count
-
5,007
No.19 Fuji Xerox multifunction devices and printers vulnerable to denial-of-service (DoS) JVNDB-2021-000026
- CVSSv2 Severity Rating Scale
-
Level I (Low)
- CVSSv2 Base Score
-
3.3
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
4.3
- Date Public
-
2021/3/19
- Access Count
-
4,985
No.20 Multiple vulnerabilities in KonaWiki2 JVNDB-2021-000036
- CVSSv2 Severity Rating Scale
-
Level III (High)
- CVSSv2 Base Score
-
7.5
- CVSSv3 Severity Rating Scale
-
High
- CVSSv3 Base Score
-
7.3
- Date Public
-
2021/5/13
- Access Count
-
4,971
Table 3-2 lists the top 5 most accessed vulnerability information among those reported by domestic product developers.
Table 3-2. Top 5 Most Accessed Vulnerabilities Reported by Domestic Product Developers [Apr. - Jun. 2021]
No.1 Information Disclosure Vulnerability in Cosminexus JVNDB-2021-001345
- CVSSv2 Base Score
-
- -
- CVSSv3 Base Score
-
- -
- Date Public
-
2021/4/13
- Access Count
-
5,475
No.2 Vulnerability in JP1/VERITAS JVNDB-2021-001344
- CVSSv2 Base Score
-
- -
- CVSSv3 Base Score
-
-
- Date Public
-
2021/4/13
- Access Count
-
5,471
No.3 Multiple Vulnerabilities in JP1/Automatic Operation JVNDB-2021-001026
- CVSSv2 Base Score
-
-
- CVSSv3 Base Score
-
-
- Date Public
-
2021/2/16
- Access Count
-
4,121
No.4 Improper access control vulnerability in JP1/IT Desktop Management 2 - Manager and JP1/NETM/Asset Information Manager JVNDB-2021-001021
- CVSSv2 Base Score
-
-
- CVSSv3 Base Score
-
-
- Date Public
-
2021/2/8
- Access Count
-
4,087
No.5 DoS Vulnerability in JP1/Automatic Job Management System 3 and JP1/Automatic Job Management System 2 JVNDB-2020-004476
- DoS Vulnerability in JP1/Automatic Job Management System 3 and JP1/Automatic Job Management System 2
- CVSSv2 Base Score
-
-
- CVSSv3 Base Score
-
-
- Date Public
-
2020/5/18
- Access Count
-
4,062
Footnotes
-
(*1)
-
(*2)
-
(*3)
-
(*4)
-
(*5)
-
(*6)
-
(*7)
-
(*8)
-
(*9)
Past Quarterly Reports
Contact information
IT Security Center,
Information-technology Promotion Agency, Japan (ISEC/IPA)