Enhancing information security
Vulnerability Countermeasure Information Database JVN iPedia Registration Status [2025 3rd Quarter (Jul. - Sep.)]
Release Date:Nov 19, 2025
IT Security Center
1. 2025 3rd Quarter: Vulnerability Countermeasure Information Database JVN iPedia Registration Status
The vulnerability countermeasure information database JVN iPedia is endeavoring to become a comprehensive vulnerability database where vulnerability information is aggregated for easy access for IT users. JVN iPedia collects and/or translates the vulnerability information published by 1) domestic software developers, 2) JVN (footnote 1), a vulnerability information portal run by JPCERT/CC and IPA, and 3) NVD (footnote 2), a vulnerability database run by NIST (footnote 3). JVN iPedia has been making vulnerability information available to the public since April 25, 2007.
1-1. Vulnerabilities Registered in the 3rd Quarter of 2025
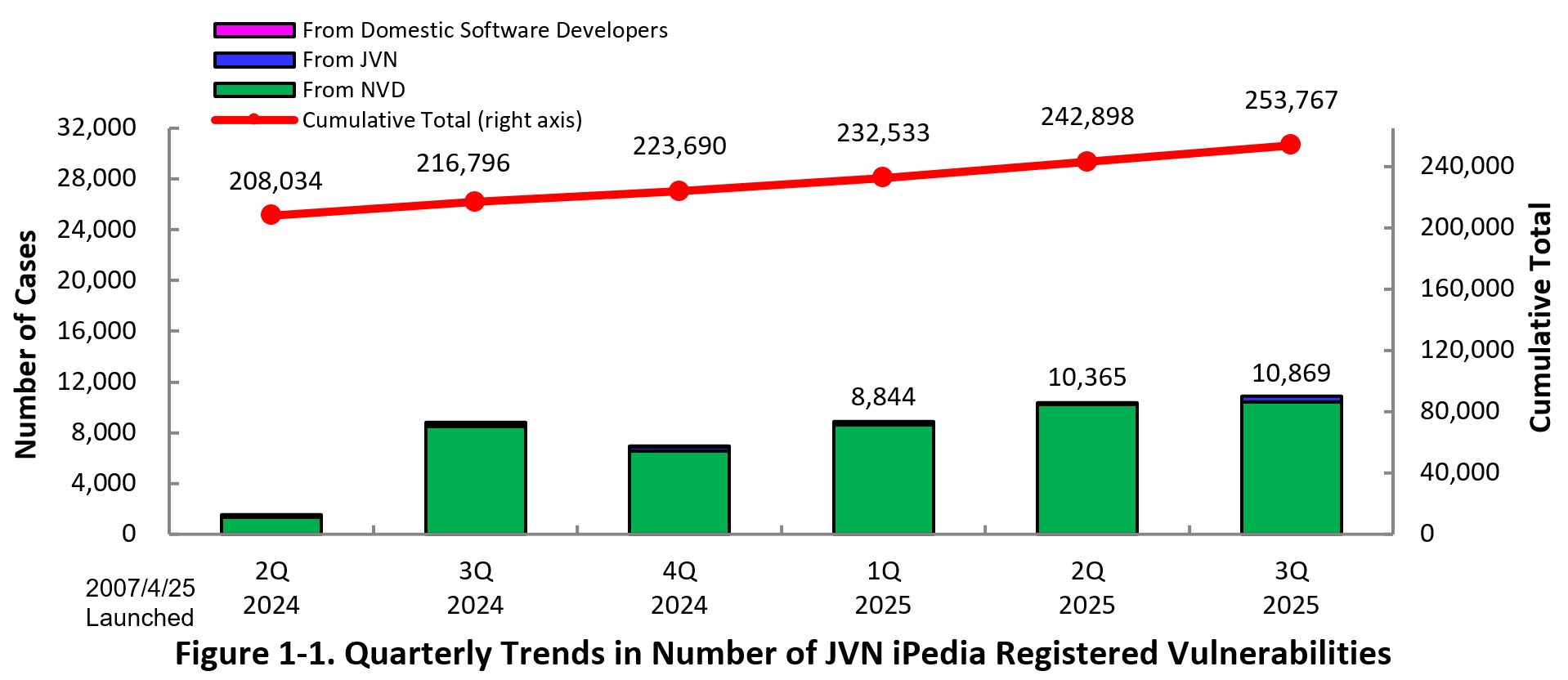
JVN iPedia now stores 253,767 vulnerabilities
The summary of the vulnerability information registered to the Japanese version of JVN iPedia during the third quarter (July 1 to September 30) of 2025 is shown in the table below. As of the end of September 2025, the total number of vulnerabilities stored in JVN iPedia is 253,767 (Table 1-1, Figure 1-1).
As for the JVN iPedia English version, the total number of vulnerabilities stored is 3,071 as shown in the Table 1-2.
Table 1-1. Vulnerabilities Registered in JVN iPedia in the 3rd Quarter of 2025 (Japanese Version)
| Information Source | Registered Cases | Cumulative Cases |
|---|---|---|
| Domestic Software Developers | 0 cases | 291 cases |
| JVN | 459 cases | 16,906 cases |
| NVD | 10,410 cases | 236,570 cases |
| Total | 10,869 cases | 253,767 cases |
Table 1-2. Vulnerabilities Registered in JVN iPedia in the 3rd Quarter of 2025 (English Version)
| Information Source | Registered Cases | Cumulative Cases |
|---|---|---|
| Domestic Software Developers | 0 cases | 294 cases |
| JVN | 55 cases | 2,777 cases |
| Total | 55 cases | 3,071 cases |
2. Details on JVN iPedia Registered Data
2-1. Types of Vulnerabilities Reported
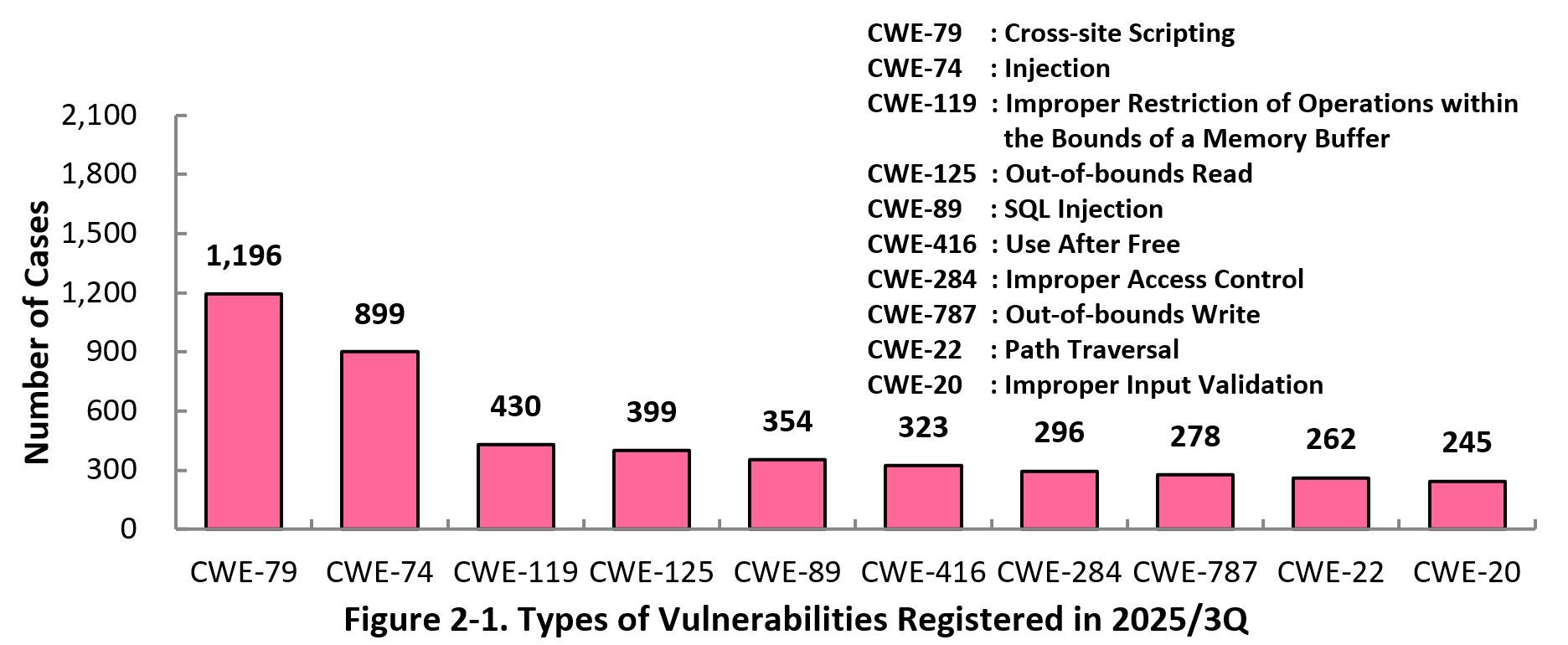
Figure 2-1 shows the number of vulnerabilities newly added to JVN iPedia during the third quarter (July 1 to September 30) of 2025, sorted by the CWE vulnerability types.
The type of the vulnerabilities reported most in the third quarter is CWE-79 (Cross-Site Scripting) with 1,196 cases, followed by CWE-74 (Injection) with 899, CWE-119 (Improper Restriction of Operations within the Bounds of a Memory Buffer) with 430, CWE-125 (Out-of-bounds Read) with 399, CWE-89 (SQL Injection) with 354. CWE-79 (Cross-site Scripting), the most reported vulnerability type in this quarter, could allow attackers to display false webpages and/or steal information.
Software developers need to make sure to mitigate vulnerability from the planning and design phase of software development. IPA provides tools and guidelines, such as “Vulnerability Countermeasure Guide for Software Developers” (footnote 4), “How to Secure Your Web-site” (footnote 5), and “AppGoat” (footnote 6), a hands-on venerability learning tool, for website developers and operators to build secure websites.
2-2. Severity of Vulnerabilities Reported
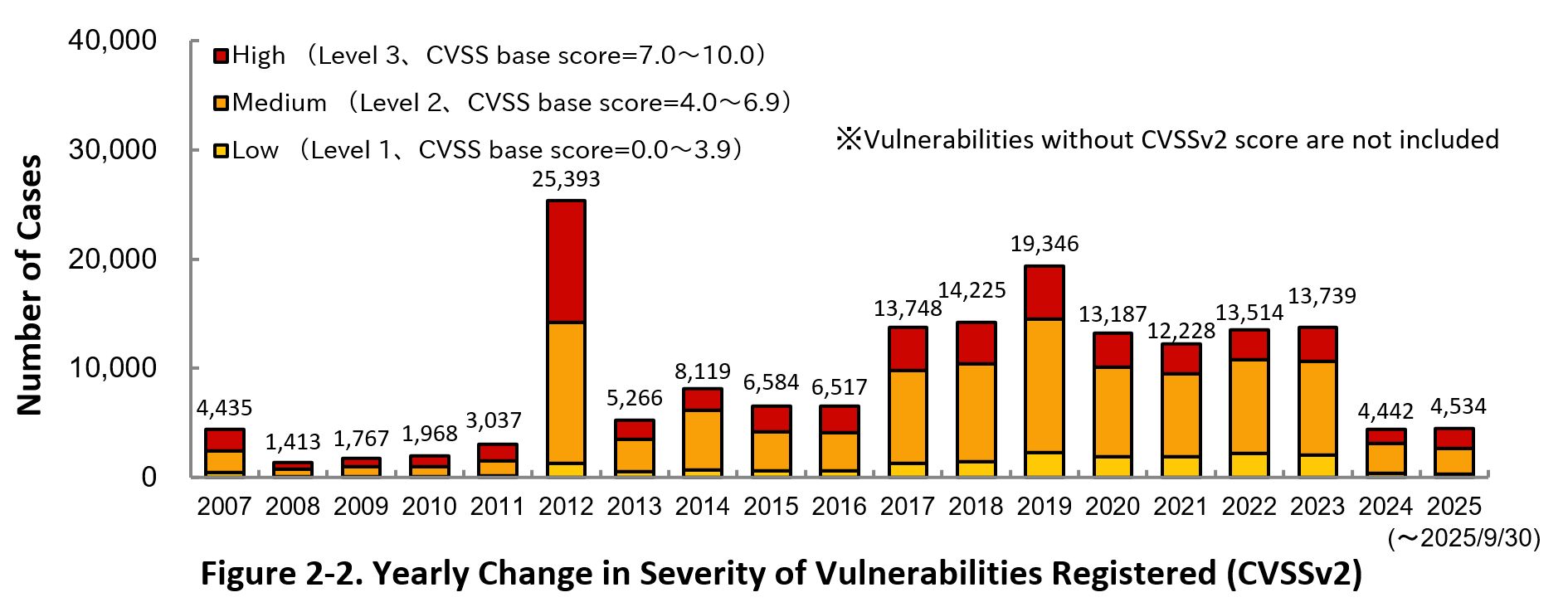
Figure 2-2 shows the yearly change in the CVSSv2 rating scale based severity of vulnerabilities registered to JVN iPedia.
As for the vulnerabilities added to JVN iPedia in 2025, 41.1 percent are “Level 3” (7.0 - 10.0), 51.3 percent are “Level 2” (4.0 – 6.9) and 7.6 percent are “Level 1” (0.0 – 3.9). This means 92.4 percent of all vulnerabilities registered are Level 2 or higher, which are potentially critical enough to cause damage like information exposure or data falsification.
The reason for the significant decrease in the number of CVSSv2 registrations in JVN iPedia in 2024 is that CVSSv2 is not actively evaluated by NVD, the information collection source for JVN iPedia (footnote 7).
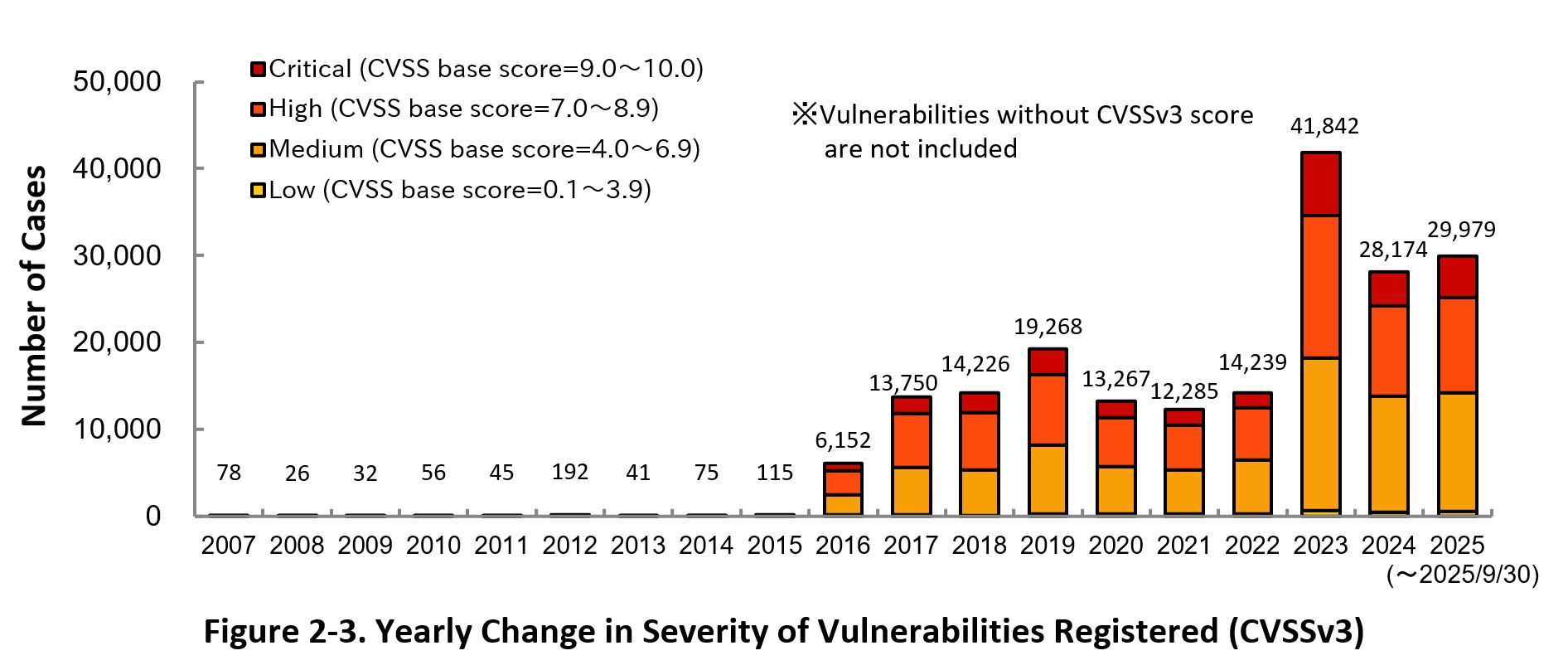
Figure 2-3 shows the yearly change in the CVSSv3 rating scale based severity of vulnerabilities registered to JVN iPedia.
As for the vulnerabilities added to JVN iPedia in 2025, 16.0 percent are “Critical” (9.0 – 10.0), 36.6 percent are “High” (7.0 – 8.9), 45.5 percent are “Medium” (4.0 – 6.9) and 2.0 percent are “Low” (0.1 – 3.9).
To avoid the threats posed by the known vulnerabilities, both product developers and IT users should pay close attention to vulnerability disclosures and update the software they use to a fixed version or apply a security patch as soon as it becomes available. They can also check JVN iPedia for new vulnerabilities that are in RSS and XML formats (footnote 8).
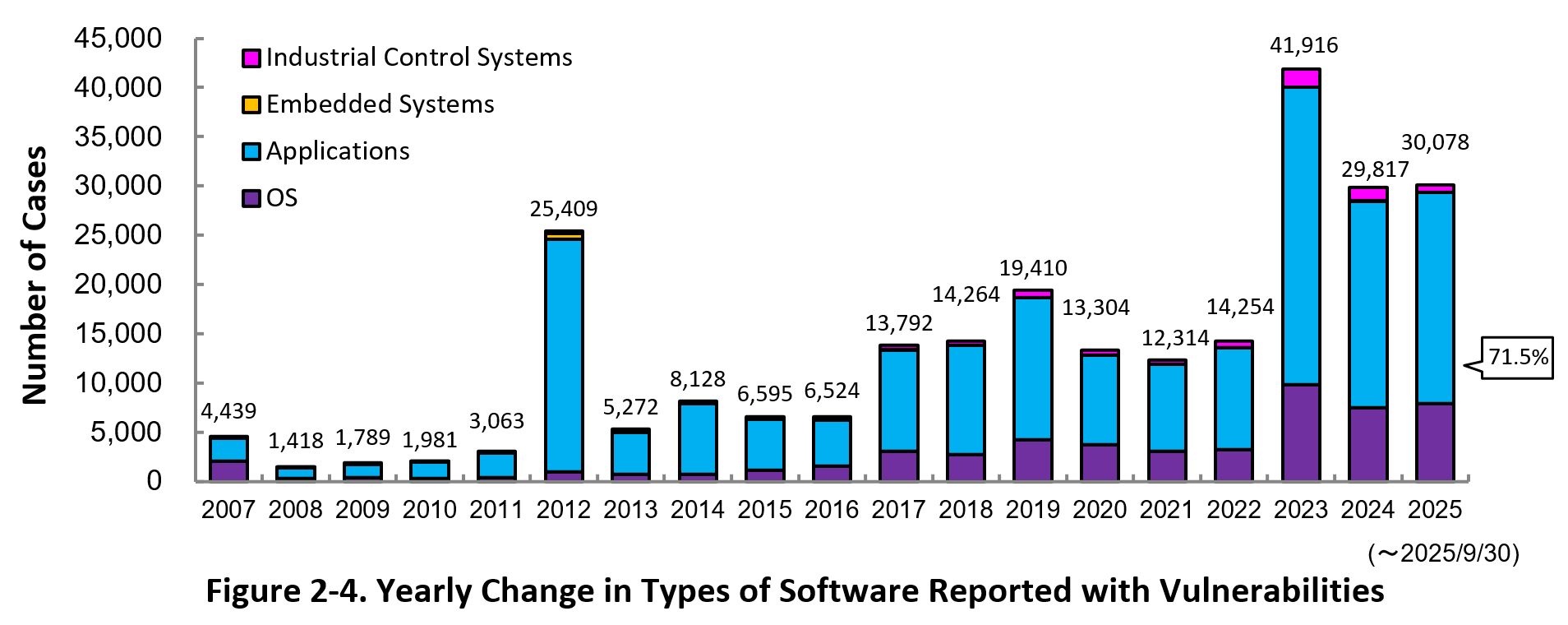
2-3. Types of Software Reported with Vulnerability
Figure 2-4 shows the yearly change in the type of software reported with vulnerability. Application vulnerabilities have been published most, accounting for 71.5 percent (21,507 out of 30,078) of the 2025 total.
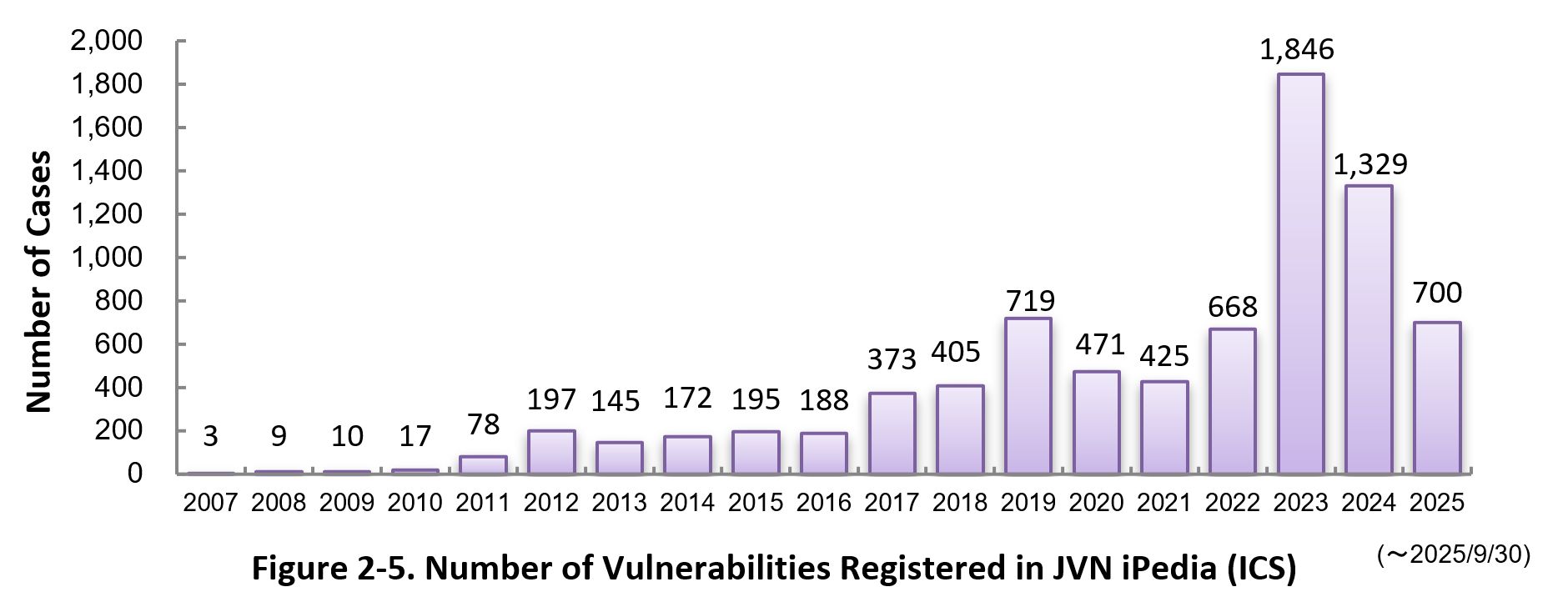
Figure 2-5 shows the yearly change in the number of JVN iPedia-stored vulnerabilities in industrial control systems (ICS) used in critical infrastructure sectors. As of September 2025, the total of 7,950 ICS vulnerabilities have been registered.
2-4. Products Reported with Vulnerability
Table 2-1 lists the top 20 software whose vulnerabilities were most registered to JVN iPedia during the third quarter (July 1 to September 30) of 2025.
This quarter, the most registered products were Qualcomm components, followed by a wide range of operating systems from various vendors, including the Linux kernel, Microsoft and Android.
Besides those in the top 20 list, JVN iPedia stores and offers vulnerability information about a variety of software. IPA hopes software developers and users will make good use of JVN iPedia to efficiently check vulnerability information and take necessary action in a timely manner (footnote 9).
Table 2-1. Top 20 most registered software products vulnerability countermeasure information in JVN iPedia [Jul. – Sep. 2025]
|
Rank
|
Category
|
Product Name (Vendor)
|
Number of
Vulnerabilities Registered |
|---|---|---|---|
|
1
|
Firmware
|
Qualcomm component (Qualcomm) |
1,299
|
|
2
|
OS
|
Linux Kernel (Linux) |
331
|
|
3
|
OS
|
Microsoft Windows Server 2025 (Microsoft) |
322
|
|
4
|
OS
|
Microsoft Windows Server 2022 (Microsoft) |
316
|
|
5
|
OS
|
Android (Google) |
311
|
|
6
|
OS
|
Microsoft Windows Server 2019 (Microsoft) |
292
|
|
7
|
OS
|
Microsoft Windows 11 (Microsoft) |
273
|
|
8
|
OS
|
Microsoft Windows Server 2016 (Microsoft) |
260
|
| 9 | OS | Microsoft Windows 10 (Microsoft) | 246 |
| 10 | OS | Microsoft Windows Server 2012 (Microsoft) | 207 |
|
11
|
OS
|
Microsoft Windows Server 2008 (Microsoft) |
167
|
| 12 | OS | macOS (Apple) | 160 |
|
13
|
PDF Viewer | pdf reader (Foxit) |
132
|
|
14
|
PDF Viewer/Editor
|
pdf editor (Foxit) |
131
|
|
15
|
Others
|
GitLab (GitLab.org) |
121
|
|
16
|
Business software
|
CAD Image DLL Plugin (Soft Gold Ltd) |
91
|
|
17
|
Business software
|
Microsoft Office (Microsoft) |
79
|
|
17
|
PDF Viewer/Editor
|
power pdf (tungstenautomation) |
79
|
| 19 | OS | HarmonyOS (Huawei) | 78 |
|
20
|
Business software
|
Microsoft 365 Apps (Microsoft) |
77
|
3. Most Accessed Vulnerability Countermeasure Information
Table 3-1 lists the top 20 most accessed vulnerability countermeasure information in JVN iPedia during the third quarter (July 1 to September 30) of 2025.
This quarter, all of the top 20 were vulnerability countermeasure information published in Japan Vulnerability Notes (JVN), the vulnerability countermeasure information portal.
Table 3-1. Top 20 Most Accessed Vulnerability Countermeasure Information in JVN iPedia [Jul. – Sep. 2025]
Table 3-2 lists the top 5 most accessed vulnerability information among those reported by domestic software developers.
Table 3-2. Top 5 Most Accessed Vulnerabilities Reported by Domestic Product Developers [Jul. – Sep. 2025]
|
Rank
|
ID/Title
|
CVSSv2
Base Score
|
CVSSv3
Base Score
|
Publication Date
|
Access Count |
|---|---|---|---|---|---|
|
1
|
JVNDB-2025-001244
|
-
|
-
|
January 30, 2025
|
888
|
|
2
|
JVNDB-2024-009498
Vulnerability in Cosminexus |
-
|
-
|
October 1, 2024
|
730
|
|
3
|
-
|
9.4
|
December 17, 2024
|
619
|
|
|
4
|
JVNDB-2024-006367
Unquoted Service Path in Hitachi Device Manager
|
-
|
6.7
|
August 23, 2024
|
587
|
|
5
|
-
|
7.8
|
August 27, 2024
|
584
|
Footnotes
(1) Japan Vulnerability Notes: A portal for vulnerability countermeasure information including information on vendor response to the reported vulnerabilities and security support. Operated in the collaboration of IPA and JPCERT/CC.
(2) National Vulnerability Database: A vulnerability database operated by NIST.
(3) National Institute of Standards and Technology: A U.S federal agency that develops and promotes measurement, standards and technology.
(4) Vulnerability Countermeasure Guide for Software Developers (in Japanese only)
(5) How to Secure Your Websites (latest version in Japanese only)
(6) AppGoat (in Japanese only)
(7) NIST - "Retirement of CVSS v2"
(8) IPA Data Feeds (in Japanese only)
(9) IPA Technical Watch - Daily Practice Guide (in Japanese only): Tips on Vulnerability Management The guide gives tips on how to efficiently collect and leverage vulnerability information.
Past Quarterly Reports
Contact information
IT Security Center,
Information-technology Promotion Agency, Japan (ISEC/IPA)