Enhancing information security
Vulnerability Countermeasure Information Database JVN iPedia Registration Status [2023 4th Quarter (Oct. - Dec.)]
Release Date:Feb 21, 2024
IT Security Center
1. 2023 4th Quarter: Vulnerability Countermeasure Information Database JVN iPedia Registration Status
The vulnerability countermeasure information database JVN iPedia is endeavoring to become a comprehensive vulnerability database where vulnerability information is aggregated for easy access for IT users. JVN iPedia collects and/or translates the vulnerability information published by 1) domestic software developers, 2) JVN (footnote 1), a vulnerability information portal run by JPCERT/CC and IPA, and 3) NVD (footnote 2), a vulnerability database run by NIST (footnote 3). JVN iPedia has been making vulnerability information available to the public since April 25, 2007.
1-1. Vulnerabilities Registered in 2023/4Q
JVN iPedia now stores 193,872 vulnerabilities
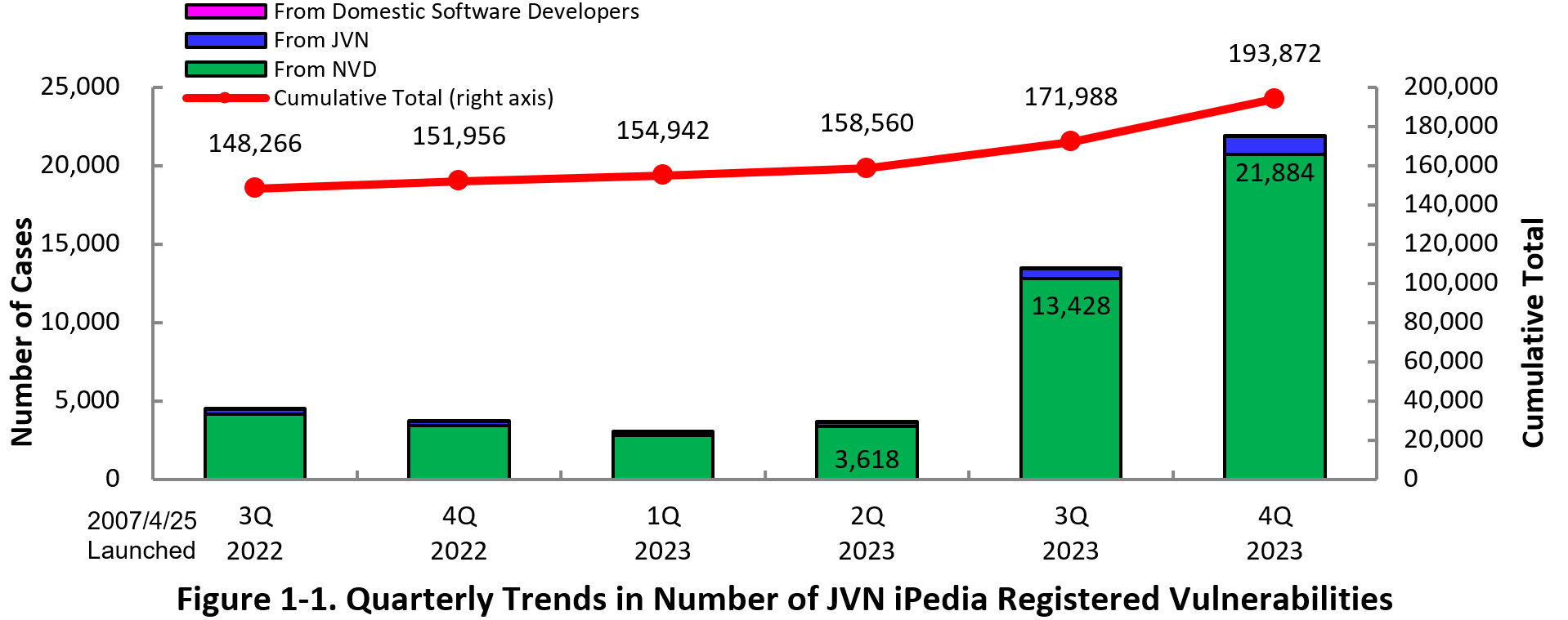
The summary of the vulnerability information registered to the Japanese version of JVN iPedia during the 4th quarter (October 1 to December 31) of 2023 is shown in the table below. As of the end of December 2023, the total number of vulnerabilities stored in JVN iPedia is 193,872 (Table 1-1, Figure 1-1).
The number of vulnerabilities registered in JVN iPedia significantly increased this quarter, but that doesn't mean more vulnerabilities were discovered in the world. That's because many vulnerabilities, mainly from last year, which were delayed in being disclosed, were disclosed due to changes in the way JVN iPedia operates.
As for the JVN iPedia English version, the total number of vulnerabilities stored is 2,724 as shown in the Table 1-2.
Table 1-1. Vulnerabilities Registered in JVN iPedia during 4th Quarter of 2023 (Japanese Version)
| Information Source | Registered Cases | Cumulative Cases |
|---|---|---|
| Domestic Software Developers | 5 cases | 275 cases |
| JVN | 1,151 cases | 14,236 cases |
| NVD | 20,728 cases | 179,361 cases |
| Total | 21,884 cases | 193,872 cases |
Table 1-2. Vulnerabilities Registered in JVN iPedia during 4th Quarter of 2023 (English Version)
| Information Source | Registered Cases | Cumulative Cases |
|---|---|---|
| Domestic Software Developers | 5 cases | 279 cases |
| JVN | 44 cases | 2,445 cases |
| Total | 49 cases | 2,724 cases |
1-2. 【Observation 1】Zero-Day Vulnerabilities in MOVEit Transfer
Large-scale attacks exploiting the vulnerabilities by a cyber attack group was observed
In May 2023, a vulnerability (CVE-2023-34362) in MOVEit Transfer, a data transfer solution provided by Progress Software was disclosed (footnote 4). This vulnerability is an SQL injection vulnerability that could be exploited by an unauthenticated, remote attacker to gain unauthorized access to the MOVEit Transfer database to steal or falsify data or perform privilege escalation. The CVSSv3.1 base score which indicates the severity of the vulnerability is 9.8 and rated as "Critical" (CVSSv3 base score = 9.0-10.0), the highest severity rating (footnote 5).
This vulnerability was confirmed to have been exploited in attacks even before the vulnerability countermeasure information was released. Such vulnerabilities are known as zero-day vulnerabilities. After the vulnerability countermeasure information was disclosed mainly in Europe and the U.S., where the products in question are widely used, several government agencies in the U.S. were also attacked. Especially, a cyberattack group "Clop" known for its ransomware attack methods of encrypting data and stealing information, was responsible for many of the attacks. Japanese companies with overseas offices were also attacked, with employee information leaked and other damage confirmed. As of January 2024, 2,730 organizations and approximately 93.34 million individuals worldwide have been affected (footnote 6)(footnote 7)(footnote 8)(footnote 9).
Several other MOVEit Transfer vulnerabilities were also disclosed in 2023. Among them, CVE-2023-35036 and CVE-2023-35708 which disclosed in a row in June, were attracted widespread attention being reported by web media because those vulnerabilities are "SQL Injection" same as CVE-2023-34362 which observed exploitation and severity ratings were both "critical" (CVSSv3.1 base score were 9.1 and 9.8 respectively)(footnote 10)(footnote 11)(footnote 12).
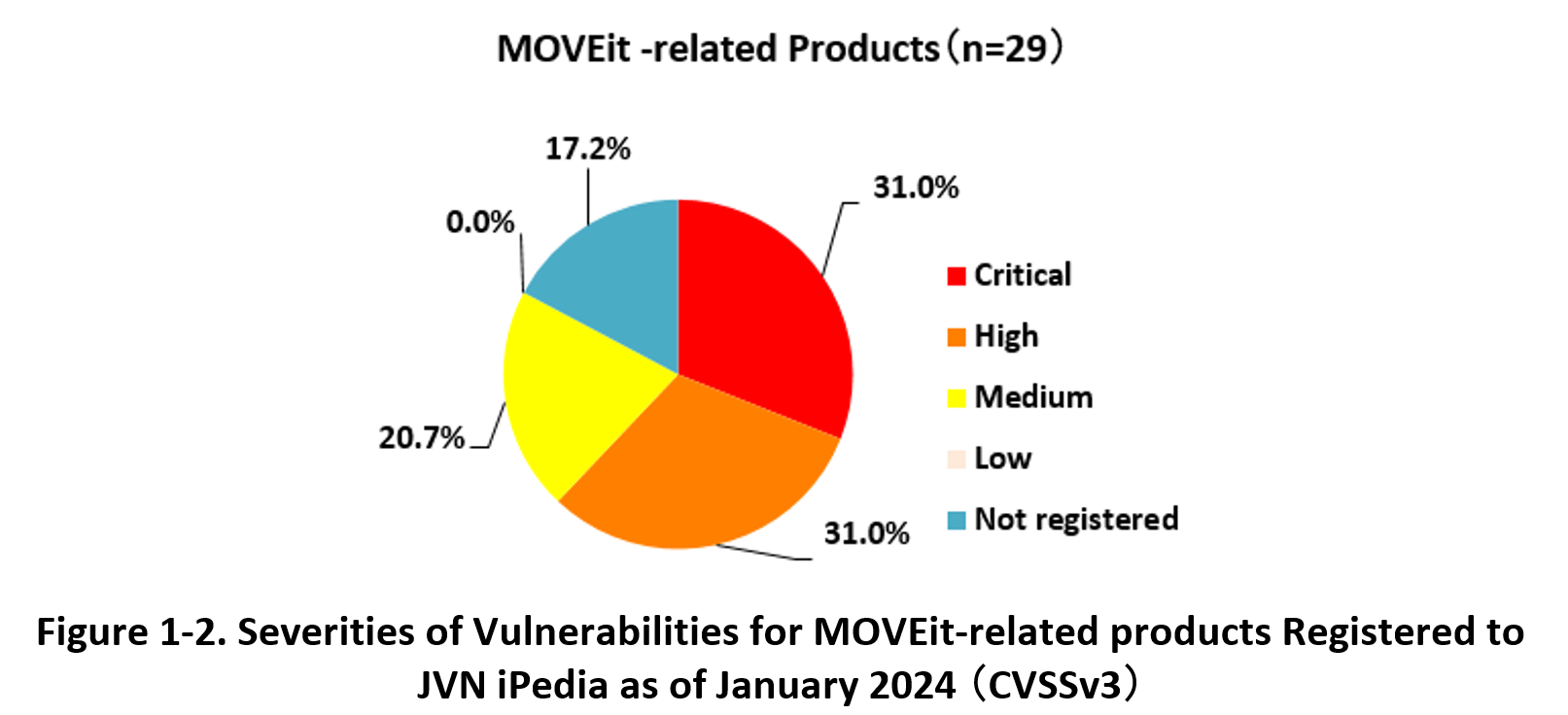
As of January 2024, cumulative total of 29 vulnerabilities in MOVEit-related products have registered to JVN iPedia . Figure 1-2 shows the percentage of these vulnerabilities by severity. In descending order of severity, 31.0% of the vulnerabilities were classified as "Critical" (CVSSv3 base score = 9.0-10.0), 31.0% as "High" (CVSSv3 base score = 7.0-8.9), 20.7% as "Medium" (CVSSv3 base score = 4.0-6.9) and 0.0% as "Low" (CVSSv3 base score = 0.1-3.9). The majority of the vulnerabilities were classified as "Critical" and "High," which have a large impact if exploited.
For products like MOVEit Transfer, which are widely used by many users, the disclosure of vulnerability information attracts attackers' attention and may be exploited in an attack. Perhaps because MOVEit Transfer is mainly used by overseas organizations, the damage in Japan was limited. If a vulnerability equivalent to MOVEit Transfer were discovered in a product widely used in Japan, the damage in Japan would be much greater. Users are required to continuously collect vulnerability information and promptly respond to security patches when they are released. If an attack that exploits the vulnerability has already been confirmed, as in this case, it is recommended to collect information on the attack and confirm whether or not any damage has occurred.
1-3. 【Observation 2】Attacks Using a New Vulnerability Related to Citrix Bleed
The vulnerability can be exploited in a ransomware attack to cause widespread damage
Among the many vulnerabilities discovered in 2023, CVE-2023-4966 (footnote 13), disclosed in October and dubbed "Citrix Bleed," made headlines. Citrix Bleed is a vulnerability in NetScaler ADC and NetScaler Gateway that could lead to a buffer overflow and information leakage if the devices are operated under certain conditions. In addition, this vulnerability could be exploited to use stolen session information or information required for multi-factor authentication to bypass authentication and compromise the system. This vulnerability has been known to be exploited since August 2023, when it was a zero-day vulnerability prior to the release of the vulnerability countermeasure information. Since then, its exploitation by ransomware such as LockBit3.0 (footnote 14) has been confirmed, and the damage has increased.
In response to this vulnerability, the developer, Citrix Systems, recommended not only updating the software to address the vulnerability, but also executing additional commands to remove active and persistent sessions. The company also rated the vulnerability as "Critical" (CVSSv3 base score = 9.0-10.0), which is the most severe, with a CVSSv3.1 base score value of 9.4.
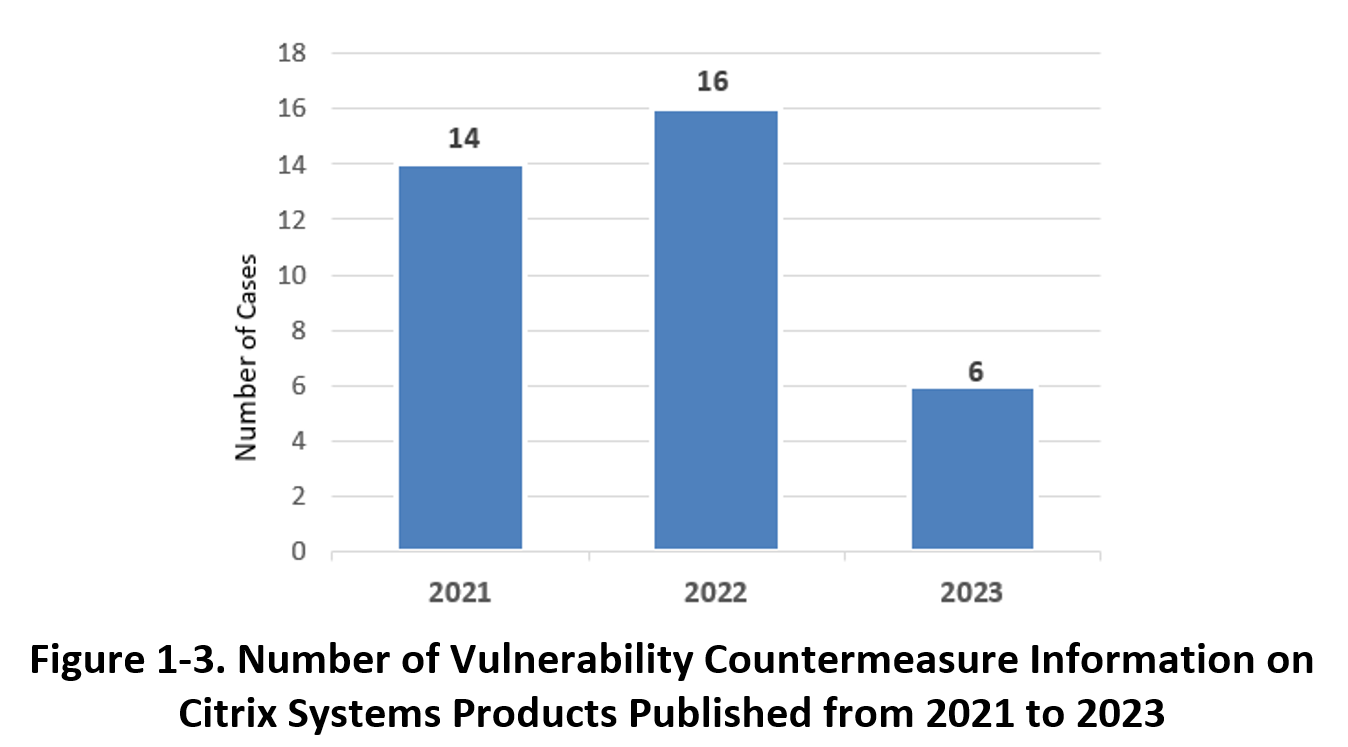
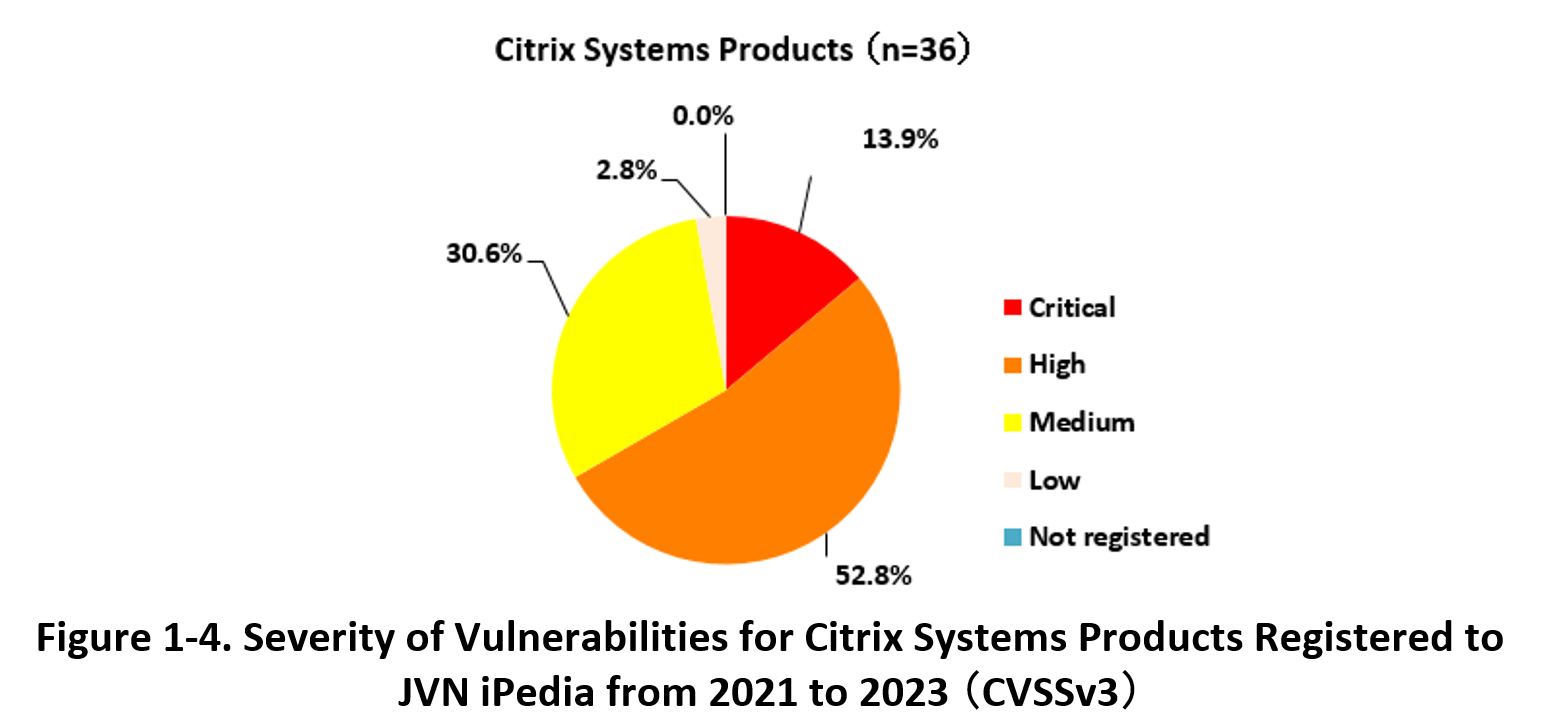
The following graphs show the number of vulnerability countermeasure information on Citrix Systems products published from 2021 to 2023 and registered in JVN iPedia, as well as the percentage of such information by severity.
The vulnerabilities are disclosed each fiscal year, and in order of severity, 13.9% of the vulnerabilities are classified as "Critical" (CVSSv3 base score = 9.0-10.0), 52.8% as "High" (CVSSv3 base score = 7.0-8.9), 30.6% as "Medium" (CVSSv3 base score = 4.0-6.9), and 2.8% as "Low" (CVSSv3 base score = 0.1-3.9). 66.7% of all vulnerabilities were classified as "Critical" and "High" with high impact if exploited.
Even if software and hardware are initially deployed with the latest versions that address existing vulnerabilities, new vulnerabilities may be discovered over time. In addition to updating to the latest version that addresses the vulnerability, additional measures may be required, such as removing active and persistent sessions, as in the case of Citrix Bleed. You should gather vulnerability information for the products you use and promptly implement any additional measures required by the developer, etc. in addition to updating to the latest version.
2. Details on JVN iPedia Registered Data
2-1. Types of Vulnerabilities Reported
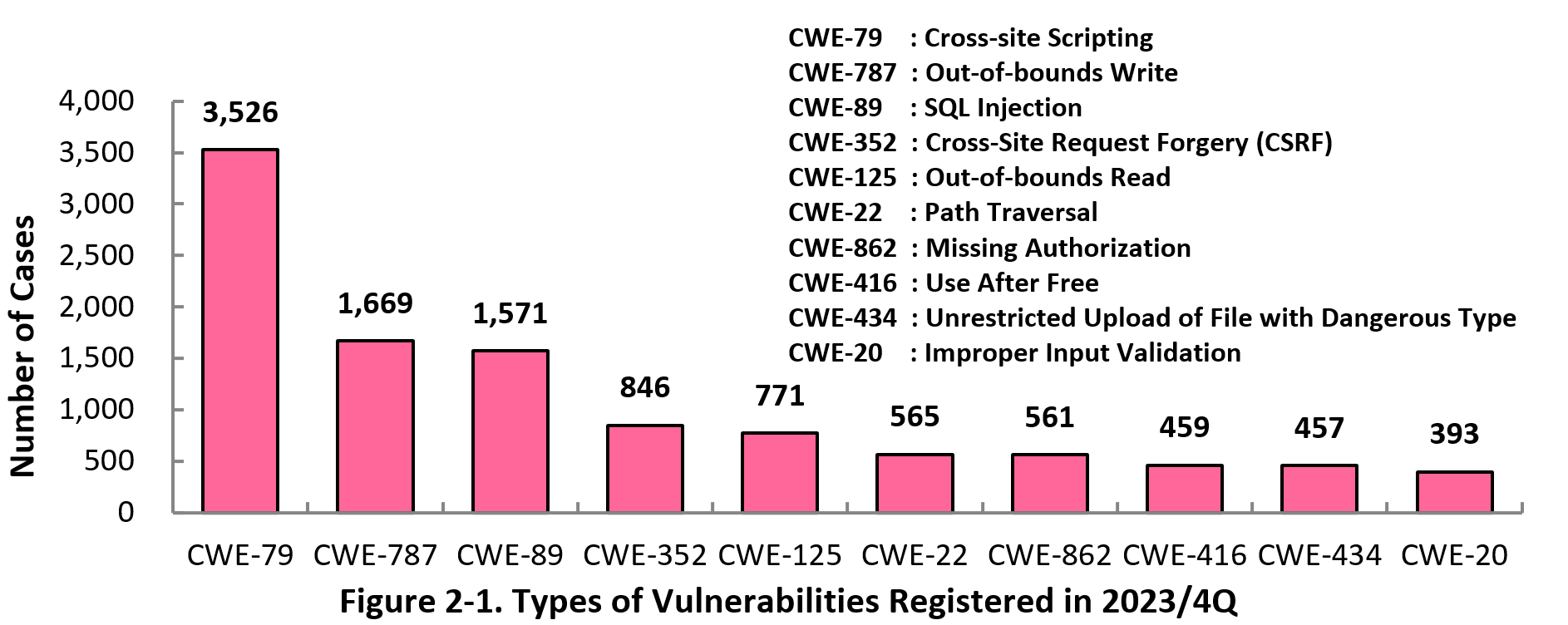
Figure 2-1 shows the number of vulnerabilities newly added to JVN iPedia during the 4th quarter (October 1 to December 31)of 2023, sorted by the CWE vulnerability types.
The type of the vulnerabilities reported most in the 4th quarter is CWE-79 (Cross-Site Scripting) with 3,526 cases, followed by CWE-787 (Out-of-bounds Write) with 1,669, CWE-89 (SQL Injection) with 1,571, CWE-352 (Cross-Site Request Forgery) with 846, CWE-125 (Out-of-bounds Read) with 771. CWE-79 (Cross-site Scripting), the most reported vulnerability type in this quarter, could allow attackers to display false webpages and/or steal information.
Software developers need to make sure to mitigate vulnerability from the planning and design phase of software development. IPA provides tools and guidelines, such as “Vulnerability Countermeasure Guide for Software Developers” (footnote 15), “How to Secure Your Web-site” (footnote 16), and “AppGoat” (footnote 17), a hands-on venerability learning tool, for website developers and operators to build secure websites.
2-2. Severity of Vulnerabilities Reported
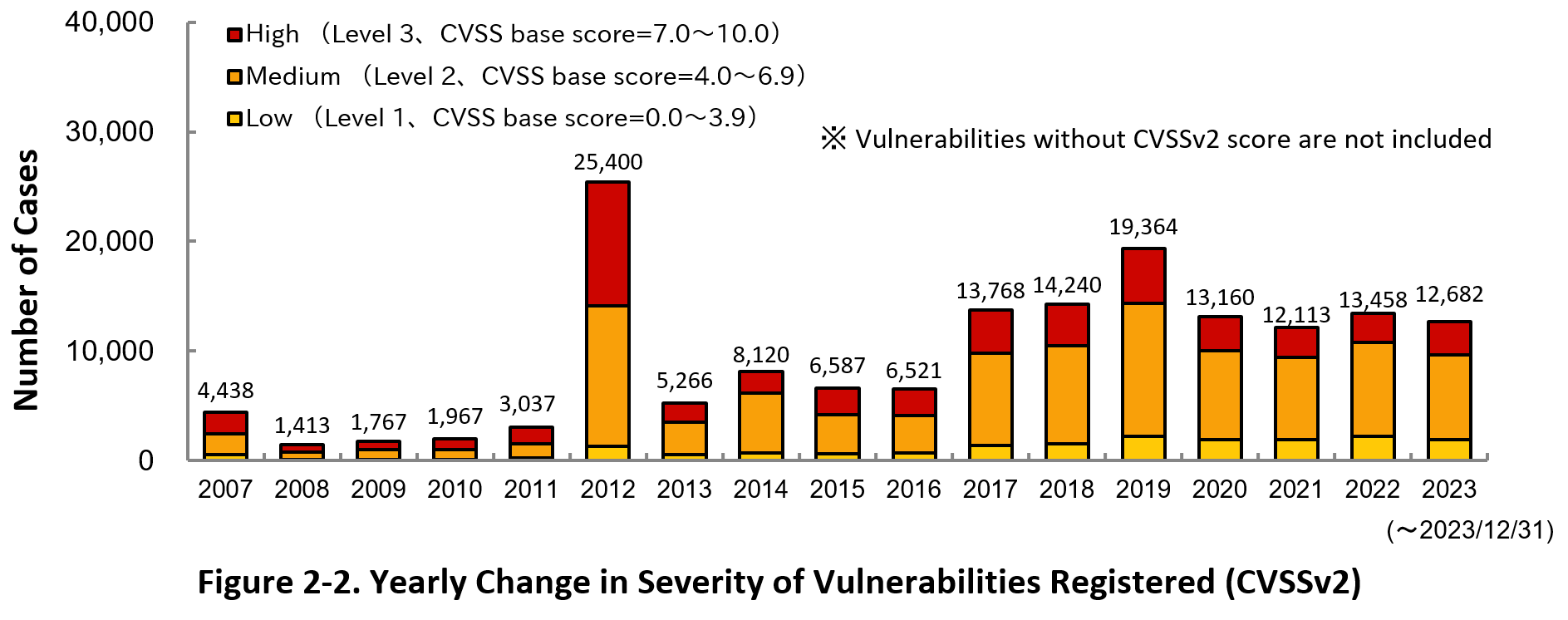
Figure 2-2 shows the yearly change in the CVSSv2 rating scale based severity of vulnerabilities registered to JVN iPedia.
As for the vulnerabilities added to JVN iPedia in 2023, 24.1 percent are “Level 3” (7.0-10.0), 60.6 percent are “Level 2” (4.0–6.9) and 15.3 percent are “Level 1” (0.0–3.9). This means 84.7 percent of all vulnerabilities registered are Level 2 or higher, which are potentially critical enough to cause damage like information exposure or data falsification.
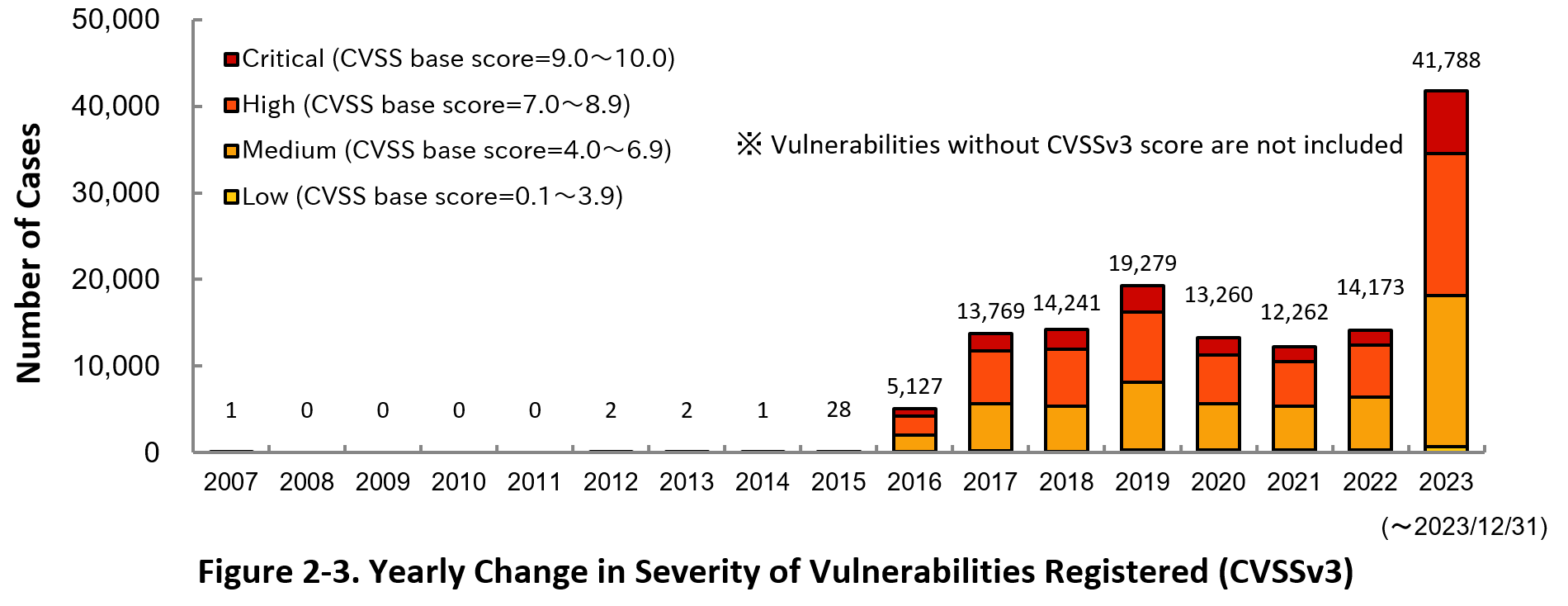
Figure 2-3 shows the yearly change in the CVSSv3 rating scale based severity of vulnerabilities registered to JVN iPedia.
As for the vulnerabilities added to JVN iPedia in 2023, 17.5 percent are “Critical” (9.0–10.0), 39.1 percent are “High” (7.0–8.9), 41.7 percent are “Medium” (4.0–6.9) and 1.7 percent are “Low” (0.1–3.9).
To avoid threats posed by the known vulnerabilities, both product developers and IT users should pay close attention to vulnerability disclosure and update software they use to a fixed version or apply a security patch as soon as possible when they become available. IT users can check vulnerabilities newly published on JVN iPedia in RSS and XML format (footnote 18) as well.
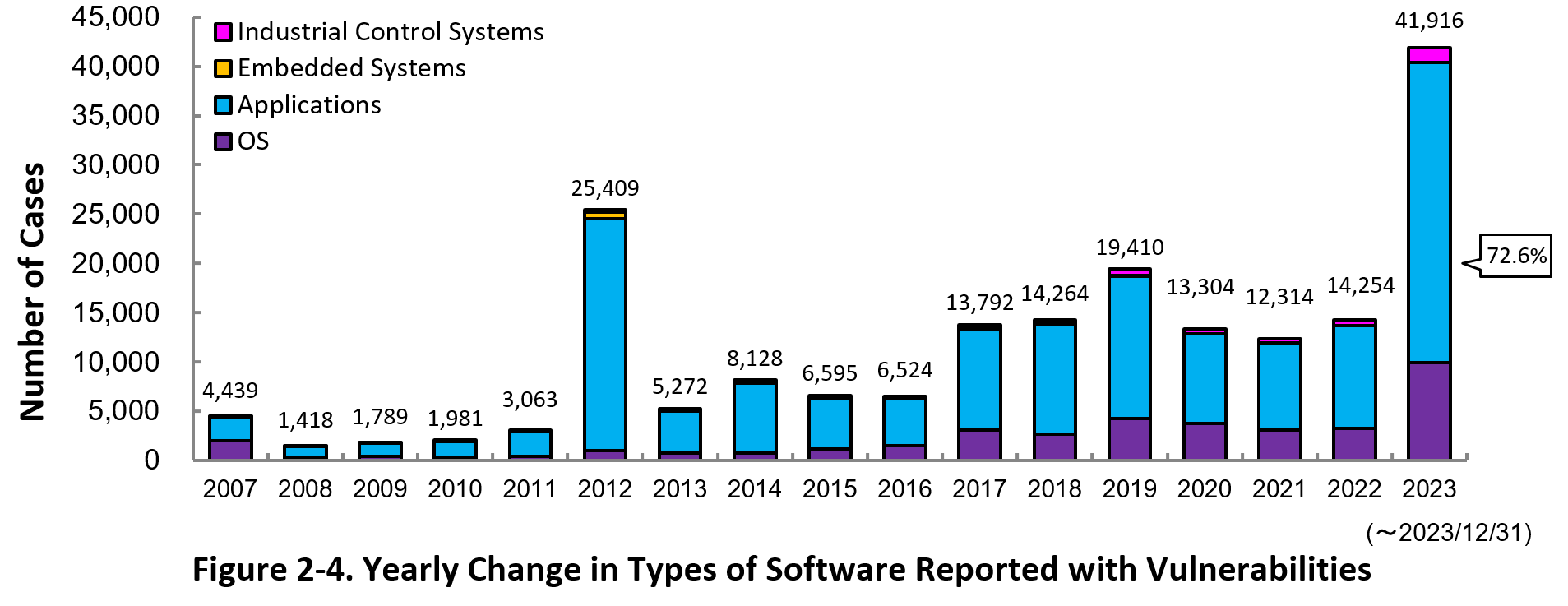
2-3. Types of Software Reported with Vulnerability
Figure 2-4 shows the yearly change in the type of software reported with vulnerability. Application vulnerabilities have been published most, accounting for 72.6 percent (30,415 out of 41,916) of the 2023 total.
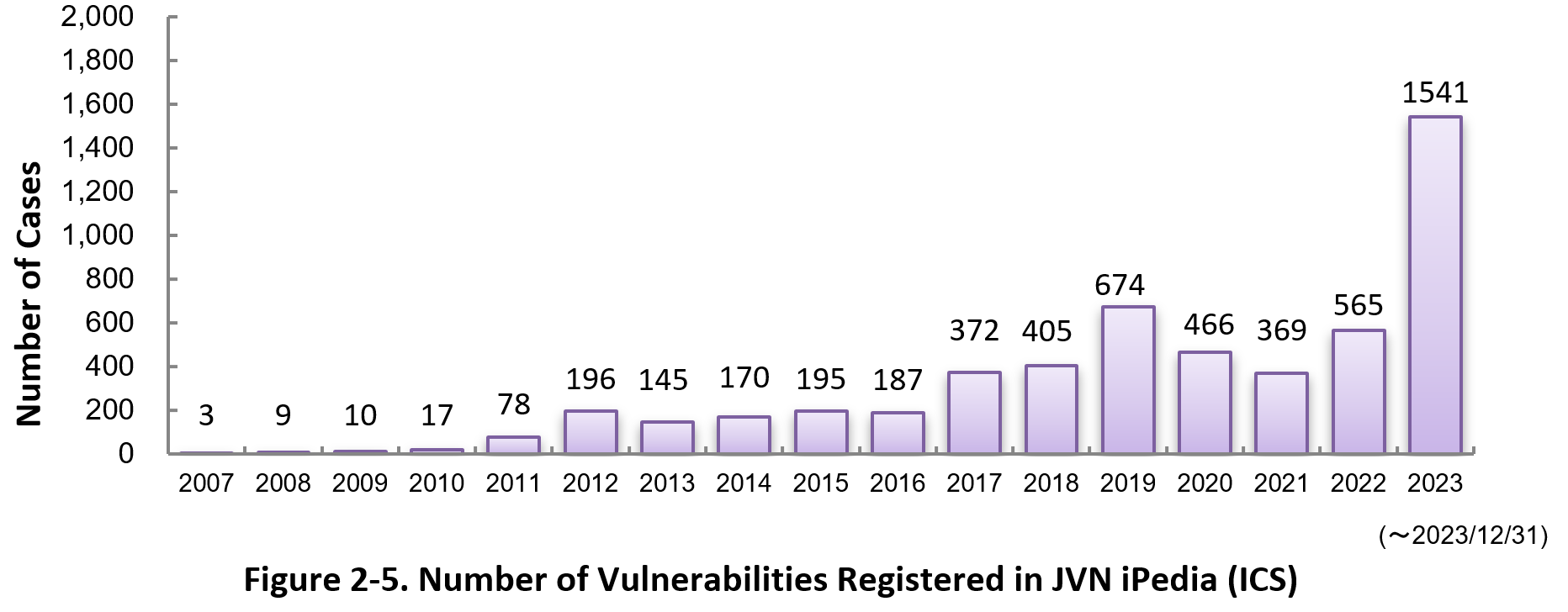
Figure 2-5 shows the yearly change in the number of JVN iPedia-stored vulnerabilities in industrial control systems (ICS) used in critical infrastructure sectors. As of December 2023, the total of 5,402 ICS vulnerabilities have been registered.
2-4. Products Reported with Vulnerability
Table 2-1 lists the top 20 software whose vulnerabilities were most registered to JVN iPedia during the 4th quarter (October 1 to December 31)of 2023.
In this quarter, the most registered product was the Qualcomm component. After the second place, a wide range of venders' OS products were on the list, such as Google, Apple, and Microsoft.
Besides those in the top 20 list, JVN iPedia stores and offers vulnerability information about a variety of software. IPA hopes software developers and users will make good use of JVN iPedia to efficiently check vulnerability information and take necessary action in a timely manner (footnote 19).
Table 2-1. Top 20 most registered software products vulnerability countermeasure information in JVN iPedia [Oct. – Dec. 2023]
|
Rank
|
Category
|
Product Name (Vendor)
|
Number of
Vulnerabilities Registered |
|---|---|---|---|
|
1
|
Firmware
|
Qualcomm component (Qualcomm) |
4,965
|
|
2
|
OS
|
Android (Google) |
1,406
|
|
3
|
OS
|
Fedora (Fedora Project) |
524
|
|
4
|
OS
|
Debian GNU/Linux (Debian) |
476
|
|
5
|
OS
|
macOS (Apple) |
406
|
|
6
|
OS
|
Linux Kernel (Linux) |
335
|
|
7
|
OS
|
iOS (Apple) |
311
|
|
8
|
OS
|
iPadOS (Apple) |
285
|
|
9
|
Browser
|
Google Chrome (Google) |
269
|
|
10
|
OS
|
EMUI (Huawei) |
206
|
|
11
|
OS
|
watchOS (Apple) |
180
|
|
11
|
OS
|
HarmonyOS (Huawei) |
180
|
|
13
|
OS
|
tvOS (Apple) |
164
|
|
14
|
Others
|
GitLab (GitLab.org) |
144
|
|
15
|
OS
|
Red Hat Enterprise Linux (Red Hat) |
138
|
|
16
|
OS
|
Microsoft Windows Server 2022 (Microsoft) |
134
|
|
17
|
OS
|
Microsoft Windows Server 2019 (Microsoft) |
129
|
|
18
|
OS
|
Microsoft Windows 11 (Microsoft) |
128
|
|
19
|
OS
|
Microsoft Windows 10 (Microsoft) |
122
|
|
20
|
OS
|
Microsoft Windows Server 2016 (Microsoft) |
116
|
3. Most Accessed Vulnerability Countermeasure Information
Table 3-1 lists the top 20 most accessed vulnerability countermeasure information in JVN iPedia during the 4th quarter (October 1 to December 31)of 2023.
This quarter, as in the previous quarter, many vulnerabilities in plugins for WordPress were ranked. This is due to the mechanical access from specific organizations.
Table 3-1. Top 20 Most Accessed Vulnerability Countermeasure Information in JVN iPedia [Oct. – Dec. 2023]
|
Rank
|
ID/Title
|
CVSSv2
Base Score
|
CVSSv3
Base Score
|
Publication Date
|
Access Count |
|---|---|---|---|---|---|
|
1
|
2.6
|
6.1
|
2023/4/24
|
10,153
|
|
|
2
|
7.5
|
8.3
|
2023/5/15
|
9,878
|
|
|
3
|
JVNDB-2022-000087
|
5.0
|
5.3
|
2022/11/8
|
9,586
|
|
4
|
JVNDB-2023-000007
|
5.0
|
7.5
|
2023/1/17
|
9,509
|
|
5
|
JVNDB-2023-000042
|
2.6
|
6.1
|
2023/5/9
|
9,480
|
|
6
|
4.0
|
5.4
|
2023/5/9
|
9,472
|
|
|
7
|
4.0
|
5.4
|
2022/6/1
|
9,447
|
|
|
8
|
2.6
|
4.3
|
2023/4/19
|
9,446
|
|
|
9
|
5.0
|
5.3
|
2022/11/18
|
9,435
|
|
|
10
|
JVNDB-2022-000038
|
2.6
|
6.1
|
2022/5/24
|
9,415
|
|
11
|
2.6
|
6.1
|
2022/11/8
|
9,402
|
|
|
12
|
JVNDB-2023-000094
|
5.5
|
5.4
|
2023/9/22
|
7,480
|
|
13
|
JVNDB-2022-000057
|
2.6
|
6.1
|
2022/7/25
|
7,262
|
|
14
|
3.5
|
5.4
|
2023/8/21
|
7,220
|
|
|
15
|
JVNDB-2022-012258
Jforum by the JForum Team vulnerable to cross-site request forgery (in Japanese only)
|
6.8
|
8.8
|
2023/8/28
|
6,808
|
|
16
|
JVNDB-2023-000070
|
2.6
|
6.1
|
2023/7/20
|
6,781
|
|
17
|
JVNDB-2023-000067
|
5.0
|
5.8
|
2023/6/27
|
6,778
|
|
18
|
JVNDB-2023-000100
|
-
|
-
|
2023/10/16
|
6,628
|
|
19
|
2.6
|
3.7
|
2023/6/9
|
6,326
|
|
|
20
|
2.6
|
4.3
|
2022/4/15
|
6,037
|
Table 3-2 lists the top 5 most accessed vulnerability information among those reported by domestic software developers.
Table 3-2. Top 5 Most Accessed Vulnerabilities Reported by Domestic Product Developers [Oct. - Dec. 2023]
|
Rank
|
ID/Title
|
CVSSv2
Base Score
|
CVSSv3
Base Score
|
Publication Date
|
Access Count |
|---|---|---|---|---|---|
|
1
|
JVNDB-2023-001926
|
-
|
7.6
|
2023/5/23
|
5,269
|
|
2
|
-
|
-
|
2022/9/14
|
5,231
|
|
|
3
|
JVNDB-2023-001008
|
-
|
6.6
|
2023/1/18
|
5,217
|
|
4
|
-
|
6.6
|
2023/3/1
|
5,207
|
|
|
5
|
-
|
5.4
|
2022/10/5
|
5,127
|
Footnotes
(1) Japan Vulnerability Notes: A portal for vulnerability countermeasure information including information on vendor response to the reported vulnerabilities and security support. Operated in the collaboration of IPA and JPCERT/CC.
(2) National Vulnerability Database: A vulnerability database operated by NIST.
(3) National Institute of Standards and Technology: A U.S federal agency that develops and promotes measurement, standards and technology.
(4) MOVEit Transfer Critical Vulnerability (May 2023) (CVE-2023-34362)
(5) CVE-2023-34362
(6)「MOVEit Transfer」にゼロデイ脆弱性 - 侵害状況も確認を
(7) US energy department, other agencies hit in global hacking spree
(8) Sony confirms data breach impacting thousands in the U.S.
(9) Unpacking the MOVEit Breach: Statistics and Analysis
(10) CVE-2023-35036
(11) CVE-2023-35708
(12) 「MOVEit Transfer」にあらたな脆弱性 - 5月末以降、3度目の更新
(13) CVE-2023-4966
(14) 「Citrix Bleed」に対する攻撃増加 - 著名ランサムグループも悪用
(15) Vulnerability Countermeasure Guide for Software Developers (in Japanese only)
(16) How to Secure Your Websites (latest version in Japanese only)
(17) AppGoat (in Japanese only)
(18) IPA Data Feeds (in Japanese only)
(19) IPA Technical Watch - Daily Practice Guide (in Japanese only): Tips on Vulnerability Management The guide gives tips on how to efficiently collect and leverage vulnerability information.
Past Quarterly Reports
Contact information
IT Security Center,
Information-technology Promotion Agency, Japan (ISEC/IPA)