Enhancing information security
Vulnerability Countermeasure Information Database JVN iPedia Registration Status [2021 1st Quarter (Jan. - Mar.)]
Release Date:May 26, 2021
IT Security Center
1. 2021 1st Quarter: Vulnerability Countermeasure Information Database JVN iPedia Registration Status
The vulnerability countermeasure information database JVN iPedia (https://jvndb.jvn.jp/en/) is endeavoring to become a comprehensive vulnerability database where vulnerability information is aggregated for easy access for IT users. JVN iPedia collects and/or translates the vulnerability information published by 1) domestic software developers, 2) JVN (*1), a vulnerability information portal run by JPCERT/CC and IPA, and 3) NVD (*2), a vulnerability database run by NIST (*3). JVN iPedia has been making vulnerability information available to the public since April 25, 2007.
1-1. Vulnerabilities Registered in 2021/1Q
~ JVN iPedia now stores 127,089 vulnerabilities ~
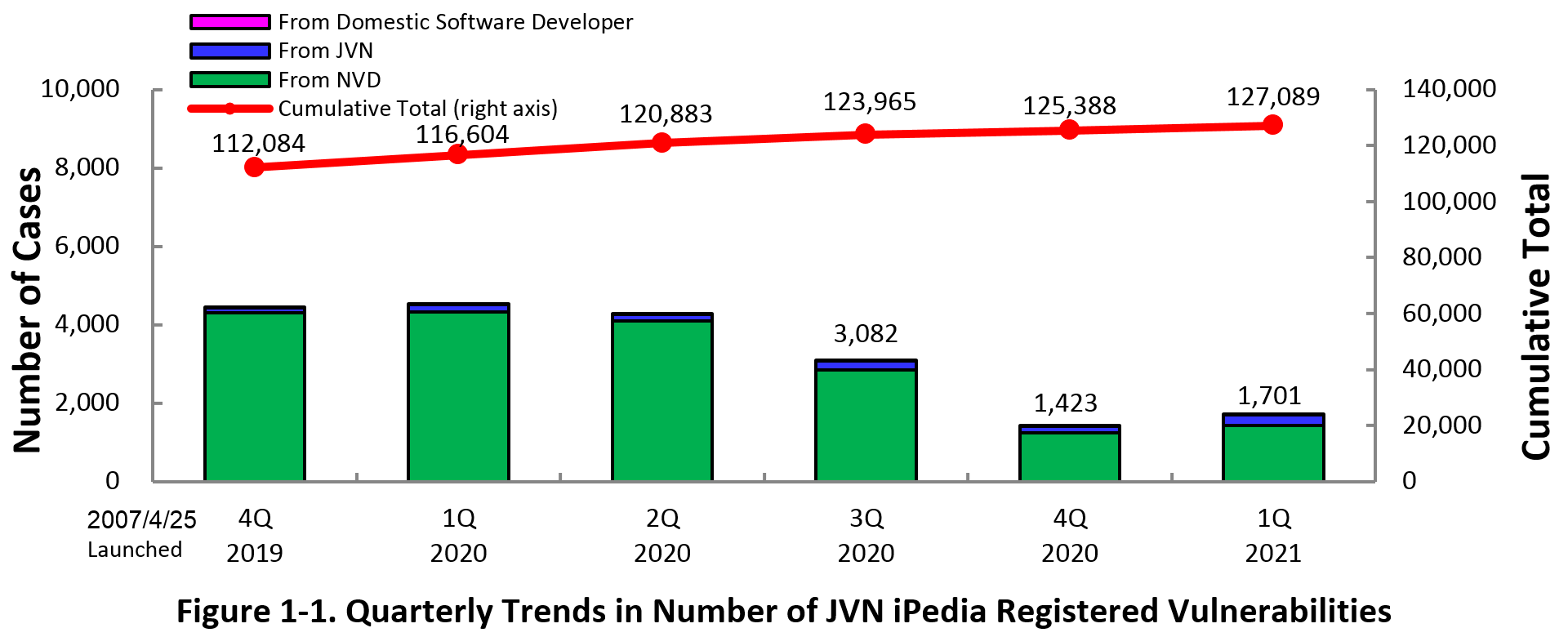
The summary of the vulnerability information registered to the Japanese version of JVN iPedia during the 1st quarter of 2021 (January 1 to March 31, 2021) is shown in the table below. As of the end of March 2021, the total number of vulnerabilities stored in JVN iPedia is 127,089 (Table 1-1, Figure 1-1).
As for the JVN iPedia English version, the total number of vulnerabilities stored is 2,260 as shown in the lower half of the Table 1-1.
Table 1-1. Vulnerabilities Registered to JVN iPedia during 1st Quarter of 2021
|
|
Information Source
|
Registered Cases
|
Cumulative Cases
|
|---|---|---|---|
|
Japanese Version
|
Domestic Product Developers
|
4 cases
|
253 cases
|
|
JVN
|
260 cases
|
9,976 cases
|
|
|
NVD
|
1,437 cases
|
116,860 cases
|
|
|
Total
|
1,701 cases
|
127,089 cases
|
|
|
English Version
|
Domestic Product Developers
|
4 cases
|
248 cases
|
|
JVN
|
39 cases
|
2,012 cases
|
|
|
Total
|
43 cases
|
2,260 cases
|
2. Details on JVN iPedia Registered Data
2-1. Types of Vulnerabilities Reported
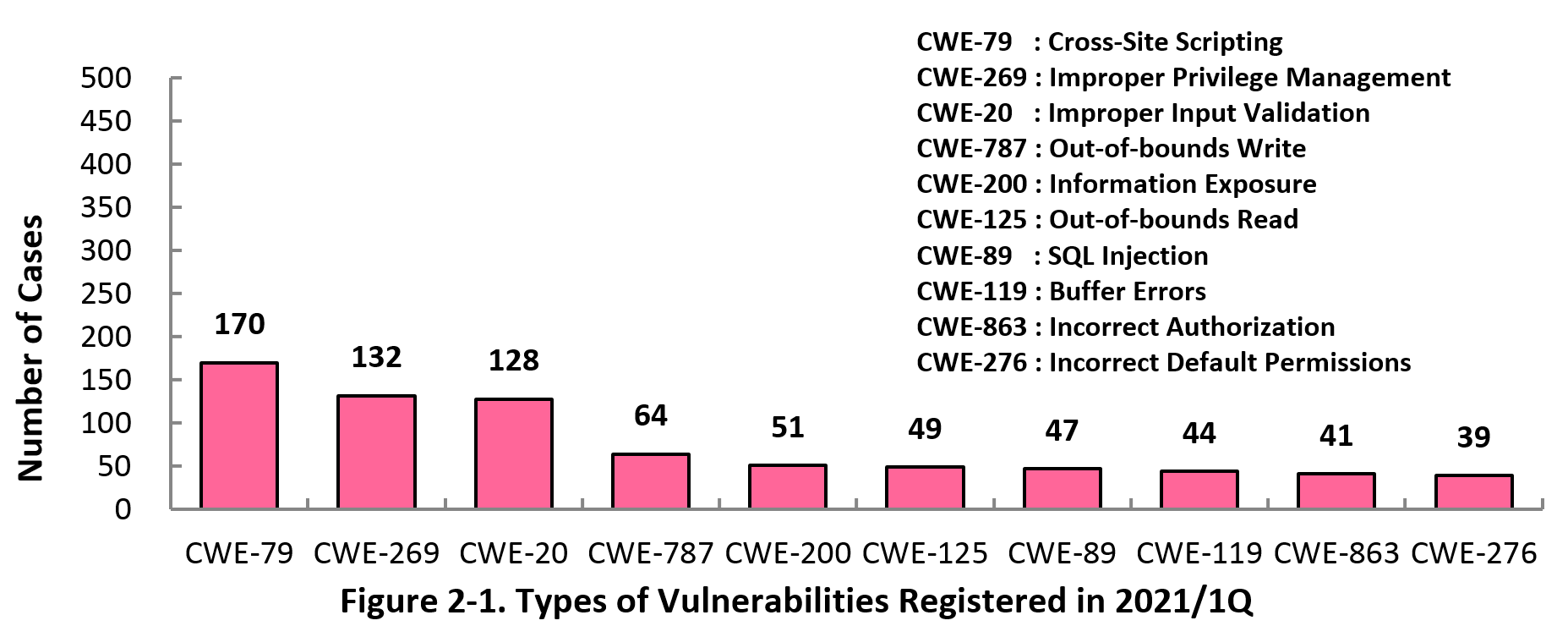
Figure 2-1 shows the number of vulnerabilities newly added to JVN iPedia during the 1st quarter of 2021, sorted by the CWE vulnerability types.
The type of the vulnerabilities reported most in the 1st quarter is CWE-79 (Cross-Site Scripting) with 170 cases, followed by CWE-269 (Improper Privilege Management) with 132 cases, CWE-20 (Improper Input Validation) with 128, CWE-787 (Out-of-bounds Write) with 64, CWE-200 (Information Exposure) with 51. CWE-79 (Cross-Site Scripting), the most reported vulnerability type in this quarter, could allow attackers to display false webpages and/or steal information.
Software developers need to make sure to mitigate vulnerability from the planning and design phase of software development. IPA provides tools and guidelines, such as "Vulnerability Countermeasure Guide for Software Developers"" (*4), "How to Secure Your Website" (*5), "Secure Programming Guide" (*6) and "AppGoat" (*7), a hands-on venerability learning tool, for website developers and operators to build secure websites.
2-2. Severity of Vulnerabilities Reported
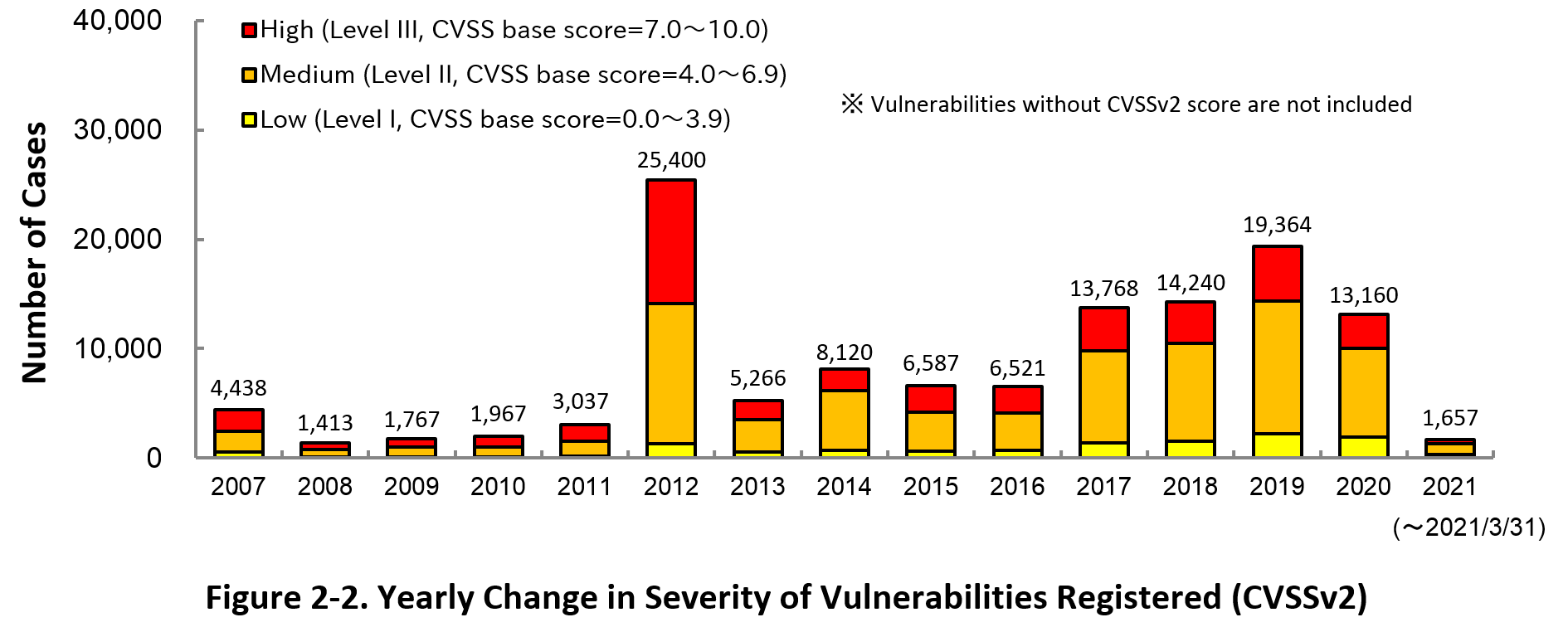
Figure 2-2 shows the yearly change in the CVSSv2 rating scale based severity of vulnerabilities registered to JVN iPedia.
As for the vulnerabilities added to JVN iPedia in 2021, 23.5 percent are “Level III” (7.0 - 10.0), 59.5 percent are “Level ll” (4.0 – 6.9) and 17.0 percent are “Level I” (0.0 – 3.9). This means 83.0 percent of all vulnerabilities registered are Level II or higher, which are potentially critical enough to cause damage like information exposure or data falsification.
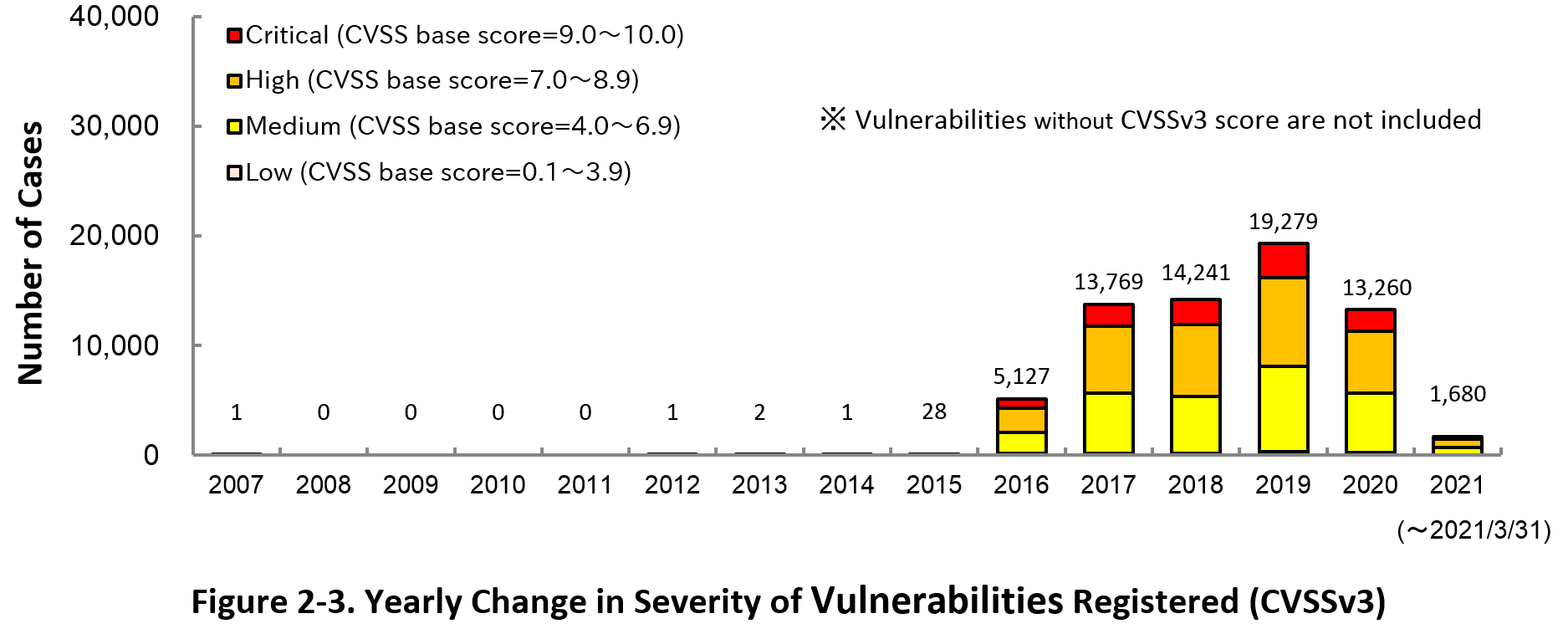
Figure 2-3 shows the yearly change in the CVSSv3 rating scale based severity of vulnerabilities registered to JVN iPedia.
As for the vulnerabilities added to JVN iPedia in 2021, 12.0 percent are “Critical” (9.0 – 10.0), 45.2 percent are “High” (7.0 – 8.9), 40.8 percent are “Medium” (4.0 – 6.9) and 2.1 percent are “Low” (0.1 – 3.9).
To avoid threats posed by the known vulnerabilities, both product developers and IT users should pay close attention to vulnerability disclosure and update software they use to a fixed version or apply a security patch as soon as possible when they become available. IT users can check vulnerabilities newly published on JVN iPedia in RSS and XML format (*8) as well.
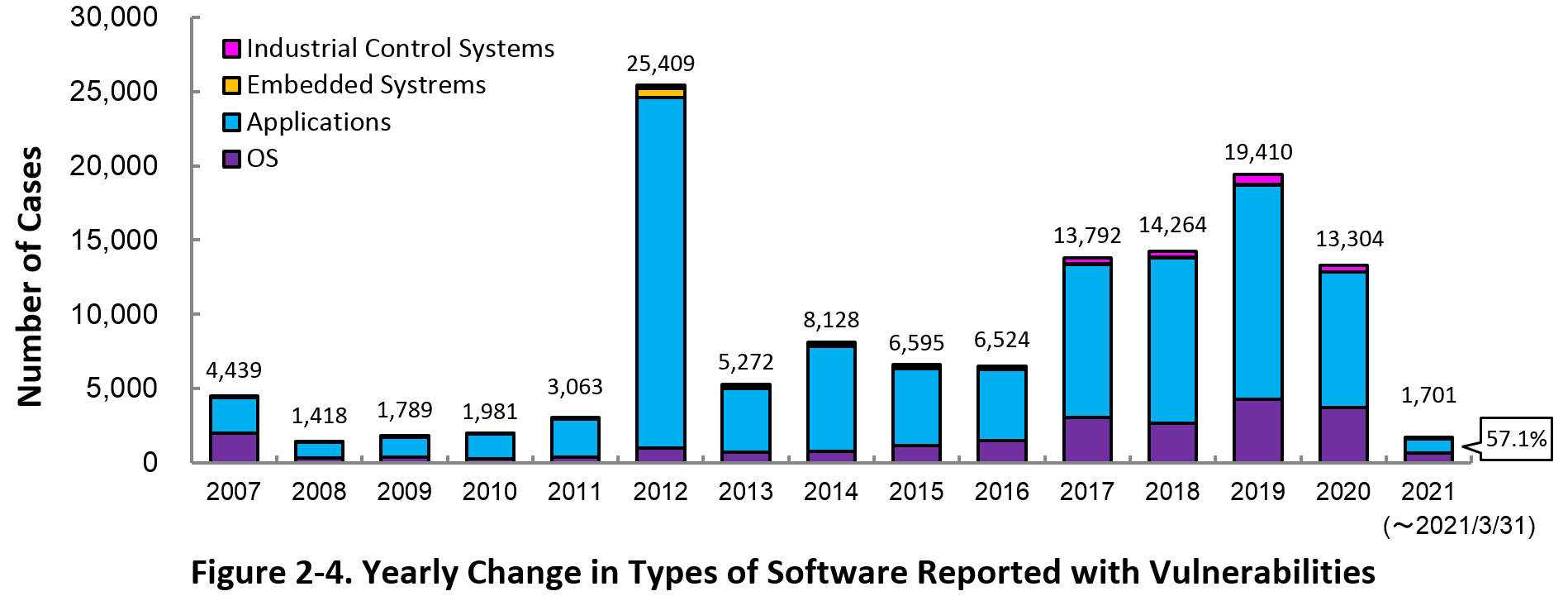
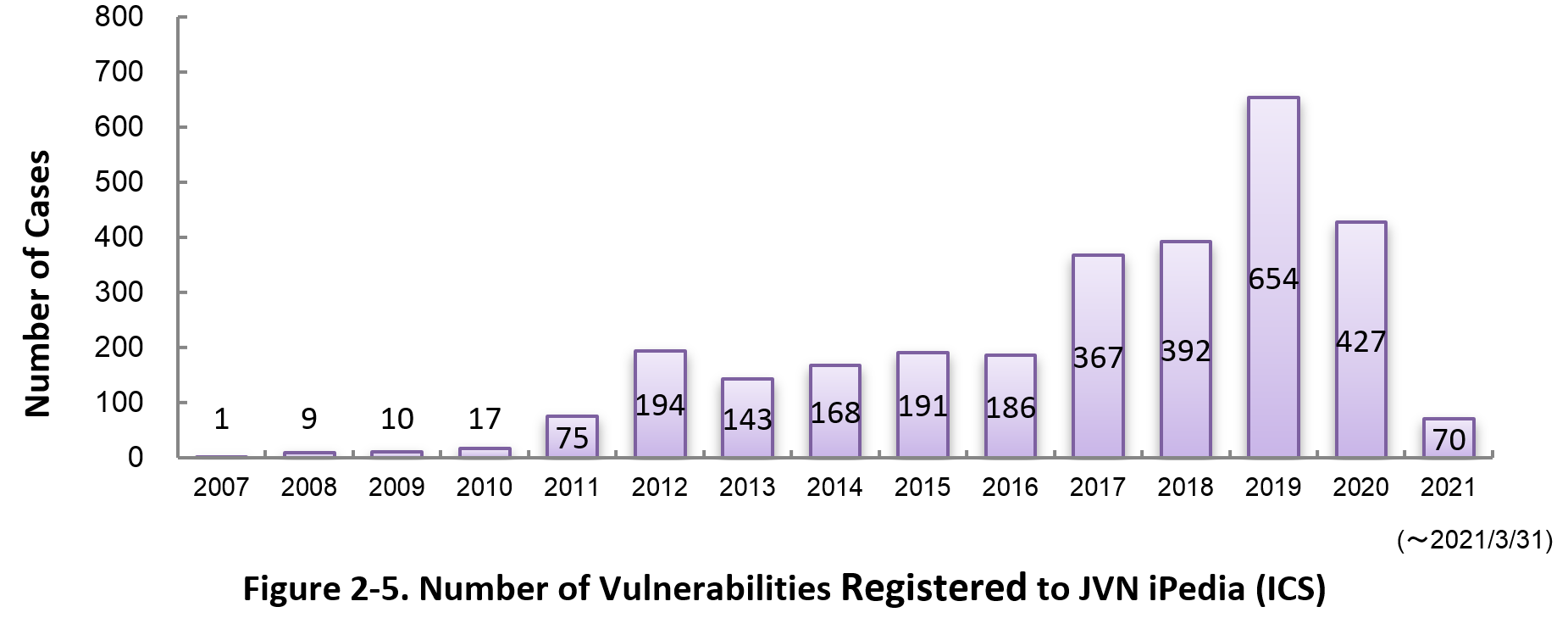
2-3. Types of Software Reported with Vulnerability
Figure 2-4 shows the yearly change in the type of software reported with vulnerability. Application vulnerabilities have been published most, accounting for 57.1 percent (972 out of 1,701) of the 2021 total.
Figure 2-5 shows the yearly change in the number of JVN iPedia-stored vulnerabilities in industrial control systems (ICS) used in critical infrastructure sectors. As of March 2021, the total of 2,904 ICS vulnerabilities have been registered.
2-4. Products Reported with Vulnerability
Table 2-1 lists the top 20 software whose vulnerabilities were most registered to JVN iPedia during the 1st quarter (January to March) of 2021.
In this quarter, the most registered products are Qualcomm products with 551 cases. This is due to the registration of vulnerability information for multiple Qualcomm products published from 2019 to 2020. OS products are lined up from 2nd to 16th rank, especially Microsoft's Windows products accounting for the most of them.
Besides those in the top 20 list, JVN iPedia stores and offers vulnerability information about a variety of software. IPA hopes software developers and users will make good use of JVN iPedia to efficiently check vulnerability information and take necessary action in a timely manner (*9).
Table 2-1. Top 20 most registered software products vulnerability countermeasure information in JVN iPedia [Jan. – Mar. 2021]
|
Rank
|
Category
|
Product Name (Vendor)
|
Number of
Vulnerabilities Registered |
|---|---|---|---|
|
1
|
Firmware
|
Qualcomm component (Qualcomm)
|
551
|
|
2
|
OS
|
Android (Google)
|
159
|
|
3
|
OS
|
Microsoft Windows Server (Microsoft)
|
153
|
|
4
|
OS
|
Microsoft Windows 10 (Microsoft)
|
152
|
|
5
|
OS
|
Microsoft Windows Server 2019 (Microsoft)
|
138
|
|
6
|
OS
|
Microsoft Windows Server 2016 (Microsoft)
|
123
|
|
7
|
OS
|
Apple Mac OS X (Apple)
|
120
|
|
8
|
OS
|
Microsoft Windows Server 2012 (Microsoft)
|
101
|
|
8
|
OS
|
iOS (Apple)
|
101
|
|
10
|
OS
|
Microsoft Windows 8.1 (Microsoft)
|
93
|
|
11
|
OS
|
Microsoft Windows RT 8.1 (Microsoft)
|
88
|
|
12
|
OS
|
Microsoft Windows Server 2008 (Microsoft)
|
78
|
|
13
|
OS
|
watchOS (Apple)
|
75
|
|
14
|
OS
|
Microsoft Windows 7 (Microsoft)
|
70
|
|
14
|
OS
|
tvOS (Apple)
|
70
|
|
16
|
OS
|
iPadOS (Apple)
|
59
|
|
17
|
Others
|
SAP 3D Visual Enterprise Viewer (SAP)
|
38
|
|
18
|
OS
|
Debian GNU/Linux (Debian)
|
36
|
|
19
|
Media Player
|
iTunes (Apple)
|
34
|
|
20
|
Cloud Service
|
iCloud (Apple)
|
32
|
3. Most Accessed Vulnerability Countermeasure Information
Table 3-1 lists the top 20 most accessed vulnerability countermeasure information in JVN iPedia during the 1st quarter of 2021 (January to March).
In this quarter, vulnerability countermeasure information published on the vulnerability counter-measure information portal site JVN accounted for 15 of the top 20.
Rating Scale
Note 1) CVSSv2 Severity Rating Scale
- Level I (Low)
- CVSS Base Score = 0.0~3.9
- Level II (Medium)
- CVSS Base Score = 4.0~6.9
- Level III (High)
- CVSS Base Score = 7.0~10.0
Note 2) CVSSv3 Severity Rating Scale
- Low
- CVSS Base Score =0.1~3.9
- Medium
- CVSS Base Score =4.0~6.9
- High
- CVSS Base Score =7.0~8.9
- Critical
- CVSS Base Score =9.0~10.0
Table 3-1. Top 20 Most Accessed Vulnerability Countermeasure Information in JVN iPedia [Jan. – Mar. 2021]
No.1 Multiple NEC Products vulnerable to authentication bypass JVNDB-2021-000002
- CVSSv2 Severity Rating Scale
-
- Level II (Medium)
- CVSSv2 Base Score
-
5.0
- CVSSv3 Severity Rating Scale
-
- Medium
- CVSSv3 Base Score
-
5.3
- Date Public
-
2021/1/4
- Access Count
-
8,557
No.2 The installer of SKYSEA Client View may insecurely load Dynamic Link Libraries JVNDB-2021-000003
- CVSSv2 Severity Rating Scale
-
- Level II (Medium)
- CVSSv2 Base Score
-
6.8
- CVSSv3 Severity Rating Scale
-
High
- CVSSv3 Base Score
-
7.8
- Date Public
-
2021/1/12
- Access Count
-
8,516
No.3 Multiple vulnerabilities in UNIVERGE SV9500/SV8500 series JVNDB-2021-000001
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
5.8
- CVSSv3 Severity Rating Scale
-
Critical
- CVSSv3 Base Score
-
9.6
- Date Public
-
2021/1/4
- Access Count
-
8,202
No.4 FileZen vulnerable to OS command injection JVNDB-2021-000015
- CVSSv2 Severity Rating Scale
-
Level III (High)
- CVSSv2 Base Score
-
9.0
- CVSSv3 Severity Rating Scale
-
Critical
- CVSSv3 Base Score
-
9.1
- Date Public
-
2021/2/16
- Access Count
-
7,686
No5. phpMyAdmin vulnerable to cross-site scripting JVNDB-2014-003893
- CVSSv2 Severity Rating Scale
-
Level I (Low)
- CVSSv2 Base Score
-
3.5
- CVSSv3 Base Score
-
-
- Date Public
-
2014/8/25
- Access Count
-
7,388
No.6 Multiple vulnerabilities in Aterm WF800HP, Aterm WG2600HP, and Aterm WG2600HP2 JVNDB-2021-000006
- CVSSv2 Severity Rating Scale
-
- Level II (Medium)
- CVSSv2 Base Score
-
4.3
- CVSSv3 Severity Rating Scale
-
- High
- CVSSv3 Base Score
-
7.5
- Date Public
-
2021/1/22
- Access Count
-
7,286
No.7 Multiple vulnerabilities in acmailer JVNDB-2021-000004
- CVSSv2 Severity Rating Scale
-
- Level III (High)
- CVSSv2 Base Score
-
7.5
- CVSSv3 Severity Rating Scale
-
Critical
- CVSSv3 Base Score
-
9.8
- Date Public
-
2021/1/14
- Access Count
-
7,131
No.8 Multiple vulnerabilities in SolarView Compact JVNDB-2021-000016
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
5.8
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
6.3
- Date Public
-
2021/2/19
- Access Count
-
6,133
No.9 GROWI vulnerable to cross-site scripting JVNDB-2021-000005
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
4.3
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
6.1
- Date Public
-
2021/1/19
- Access Count
-
5,874
No.10 Multiple vulnerabilities in multiple ELECOM products JVNDB-2021-000008
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
5.8
- CVSSv3 Severity Rating Scale
-
High
- CVSSv3 Base Score
-
8.8
- Date Public
-
2021/1/26
- Access Count
-
5,796
No.11 OS command injection vulnerability in multiple Infoscience Corporation log management tools JVNDB-2021-000007
- CVSSv2 Severity Rating Scale
-
- Level III (High)
- CVSSv2 Base Score
-
7.1
- CVSSv3 Severity Rating Scale
-
- High
- CVSSv3 Base Score
-
7.5
- Date Public
-
2021/1/27
- Access Count
-
5,533
No.12 Calsos CSDJ fails to restrict access permissions JVNDB-2021-000014
- CVSSv2 Severity Rating Scale
-
- Level II (Medium)
- CVSSv2 Base Score
-
4.0
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
4.3
- Date Public
-
2021/2/15
- Access Count
-
5,508
No.13 Multiple vulnerabilities in multiple LOGITEC products JVNDB-2021-000010
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
5.2
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
6.8
- Date Public
-
2021/1/26
- Access Count
-
5,443
No.14 Management software for NEC Storage disk array system vulnerable to improper server certificate verification JVNDB-2020-000087
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
4.0
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
4.8
- Date Public
-
2020/12/18
- Access Count
-
5,368
No.15 Wekan vulnerable to cross-site scripting JVNDB-2021-000013
- CVSSv2 Severity Rating Scale
-
Level I (Low)
- CVSSv2 Base Score
-
3.5
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
5.4
- Date Public
-
2021/2/10
- Access Count
-
5,341
No.16 Cross-site Scripting Vulnerability in Hitachi Command Suite JVNDB-2020-010072
- CVSSv2 Base Score
-
-
- CVSSv3 Base Score
-
-
- Date Public
-
2020/12/21
- Access Count
-
5,340
No.17 Improper access control vulnerability in JP1/IT Desktop Management 2 - Manager and JP1/NETM/Asset Information Manager JVNDB-2021-001021
- CVSSv2 Base Score
-
-
- CVSSv3 Base Score
-
-
- Date Public
-
2021/2/8
- Access Count
-
5,149
No.18 Multiple Vulnerabilities in JP1/Automatic Operation JVNDB-2021-001026
- CVSSv2 Base Score
-
-
- CVSSv3 Base Score
-
-
- Date Public
-
2021/2/16
- Access Count
-
5,056
No.19 Improper certificate validation vulnerability in Hitachi Infrastructure Analytics Advisor and Hitachi Ops Center Analyzer JVNDB-2020-009964
- CVSSv2 Base Score
-
-
- CVSSv3 Base Score
-
-
- Date Public
-
2020/12/15
- Access Count
-
4,992
No.20 Apache Struts 2 vulnerable to remote code execution (S2-061) JVNDB-2020-000084
- CVSSv2 Base Score
-
6.8
- CVSSv3 Base Score
-
8.1
- Date Public
-
2020/12/11
- Access Count
-
4,919
Table 3-2 lists the top 5 most accessed vulnerability information among those reported by domestic product developers.
Table 3-2. Top 5 Most Accessed Vulnerabilities Reported by Domestic Product Developers [Jan. - Mar. 2021]
No.1 Cross-site Scripting Vulnerability in Hitachi Command Suite JVNDB-2020-010072
- CVSSv2 Base Score
-
- -
- CVSSv3 Base Score
-
- -
- Date Public
-
2020/12/21
- Access Count
-
5,340
No.2 Improper access control vulnerability in JP1/IT Desktop Management 2 - Manager and JP1/NETM/Asset Information Manager JVNDB-2021-001021
- CVSSv2 Base Score
-
- -
- CVSSv3 Base Score
-
-
- Date Public
-
2021/2/8
- Access Count
-
5,149
No.3 Multiple Vulnerabilities in JP1/Automatic Operation JVNDB-2021-001026
- CVSSv2 Base Score
-
-
- CVSSv3 Base Score
-
-
- Date Public
-
2021/2/16
- Access Count
-
5,056
No.4 Improper certificate validation vulnerability in Hitachi Infrastructure Analytics Advisor and Hitachi Ops Center Analyzer JVNDB-2020-009964
- CVSSv2 Base Score
-
-
- CVSSv3 Base Score
-
-
- Date Public
-
2020/12/15
- Access Count
-
4,922
No.5 Cross-site Scripting Vulnerability in Hitachi Application Server Help JVNDB-2021-001022
- CVSSv2 Base Score
-
-
- CVSSv3 Base Score
-
-
- Date Public
-
2021/2/8
- Access Count
-
4,674
Footnotes
-
(*1)
-
(*2)
-
(*3)
-
(*4)
-
(*5)
-
(*6)
-
(*7)
-
(*8)
-
(*9)
Past Quarterly Reports
Contact information
IT Security Center, Information-technology Promotion Agency, Japan (ISEC/IPA)