Enhancing information security
Vulnerability Countermeasure Information Database JVN iPedia Registration Status [2019 2nd Quarter (Apr. - Jun.)]
Release Date:Aug 27, 2019
IT Security Center
1. 2019 2nd Quarter: Vulnerability Countermeasure Information Database JVN iPedia Registration Status
The vulnerability countermeasure information database JVN iPedia (https://jvndb.jvn.jp/en/) is endeavoring to become a comprehensive vulnerability database where vulnerability information is aggregated for easy access for IT users. JVN iPedia collects and/or translates the vulnerability information published by 1) domestic software developers, 2) JVN (*1), a vulnerability information portal run by JPCERT/CC and IPA, and 3) NVD (*2), a vulnerability database run by NIST (*3). JVN iPedia has been making vulnerability information available to the public since April 25, 2007.
1-1. Vulnerabilities Registered in 2019/2Q
~ JVN iPedia now stores 102,651 vulnerabilities ~
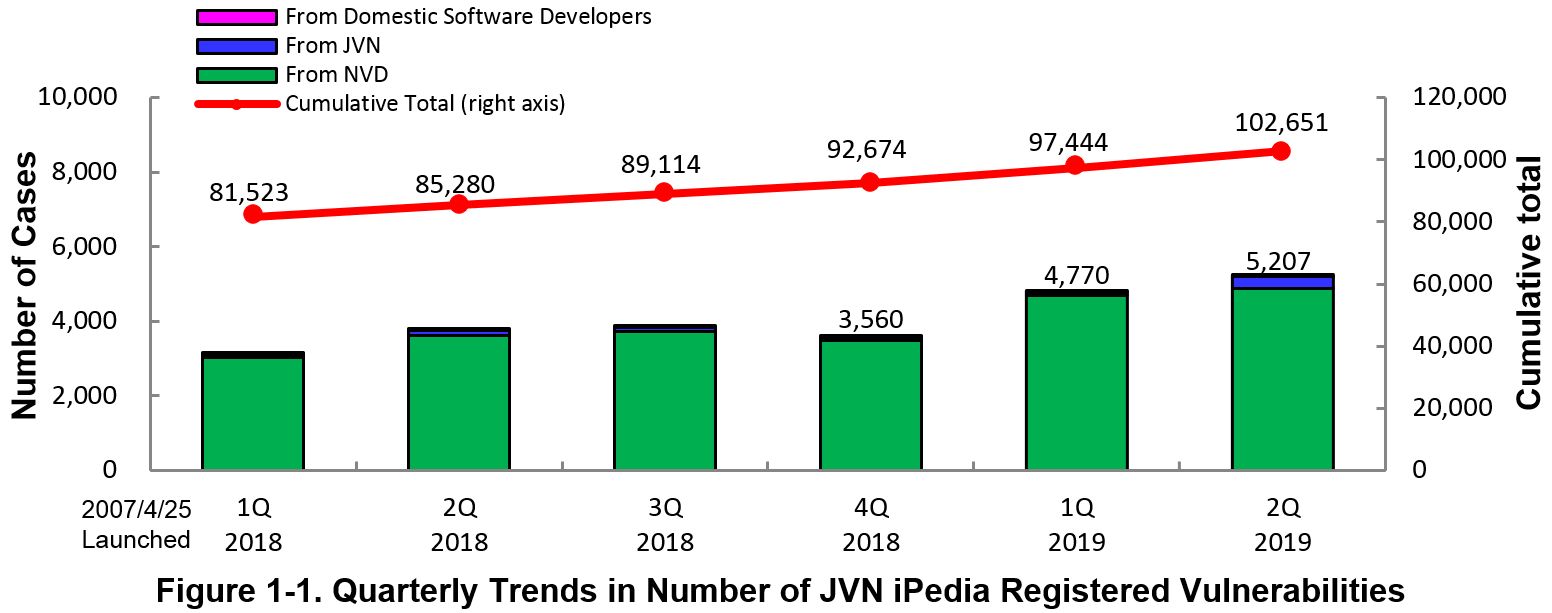
The summary of the vulnerability information registered to the Japanese version of JVN iPedia during the 2nd quarter of 2019 (April 1 to June 30, 2019) is shown in the table below. As of the end of June 2019, the total number of vulnerabilities stored in JVN iPedia is 102,651 (Table 1-1, Figure 1-1).
As for the JVN iPedia English version, the total number of vulnerabilities stored is 2,048 as shown in the lower half of the Table 1-1.
Table 1-1. Vulnerabilities Registered to JVN iPedia during 2nd Quarter of 2019
|
|
Information Source
|
Registered Cases
|
Cumulative Cases
|
|---|---|---|---|
|
Japanese Version
|
Domestic Product Developers
|
5 cases
|
218 cases
|
|
JVN
|
325 cases
|
8,672 cases
|
|
|
NVD
|
4,877 cases
|
93,761 cases
|
|
|
Total
|
5,207 cases
|
102,651 cases
|
|
|
English Version
|
Domestic Product Developers
|
4 cases
|
217 cases
|
|
JVN
|
25 cases
|
1,831 cases
|
|
|
Total
|
29 cases
|
2,048 cases
|
2. Details on JVN iPedia Registered Data
2-1. Types of Vulnerabilities Reported
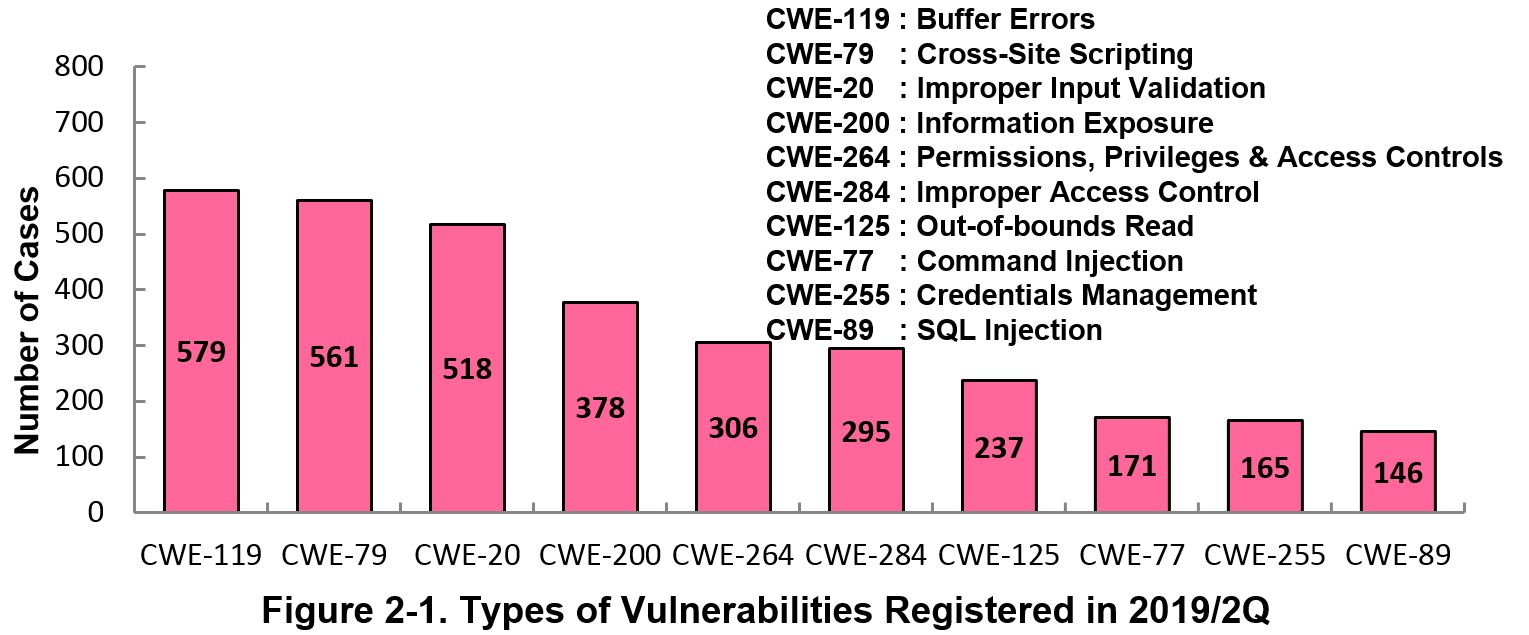
Figure 2-1 shows the number of vulnerabilities newly added to JVN iPedia during the 2nd quarter of 2019, sorted by the CWE vulnerability types.
The type of the vulnerabilities reported most in the 2nd quarter is CWE-119 (Improper Restriction of Operations within the Bounds of a Memory Buffer (Buffer Errors)) with 579 cases, followed by CWE-79 (Cross-Site Scripting) with 561, CWE-20 (Improper Input Validation) with 518, CWE-200 (Information Exposure) with 378, CWE-264 (Permissions, Privileges, and Access Controls) with 306.
CWE-119 (buffer error), the most reported vulnerability type in this quarter, could allow attackers to execute malicious code on the target server or PC, resulting in damage such as data interception or falsification.
Software developers need to make sure to mitigate vulnerability from the planning and design phase of software development. IPA provides tools and guidelines, such as "How to Secure Your Website" (*4), "Secure Programing Guide" (*5) and "AppGoat" (*6), a hands-on venerability learning tool, for website developers and operators to build secure websites.
2-2. Severity of Vulnerabilities Reported
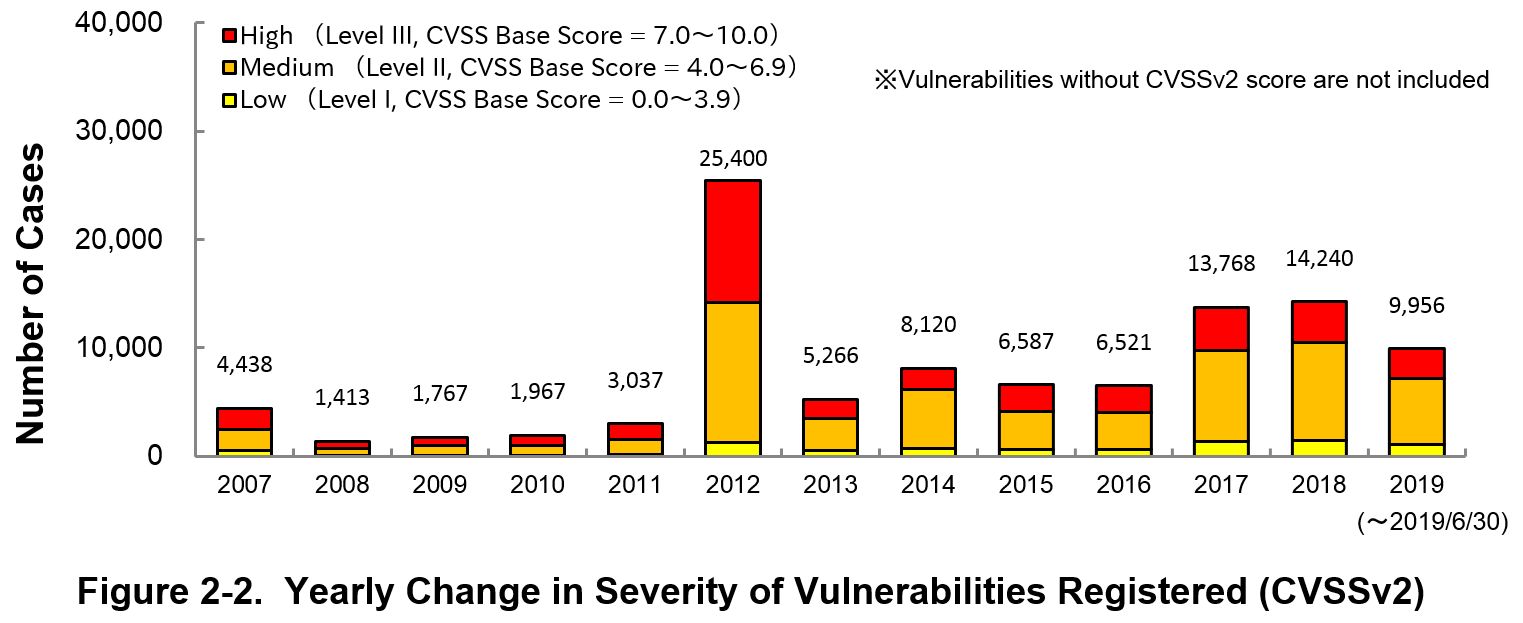
Figure 2-2 shows the yearly change in the CVSSv2 rating scale based severity of vulnerabilities registered to JVN iPedia.
As for the vulnerabilities added to JVN iPedia in 2019, 27.4 percent are “Level III” (7.0 - 10.0), 61.9 percent are “Level ll” (4.0 – 6.9) and 10.7 percent are “Level I” (0.0 – 3.9). This means 89.3 percent of all vulnerabilities registered are Level II or higher, which are potentially critical enough to cause damage like information exposure or data falsification.
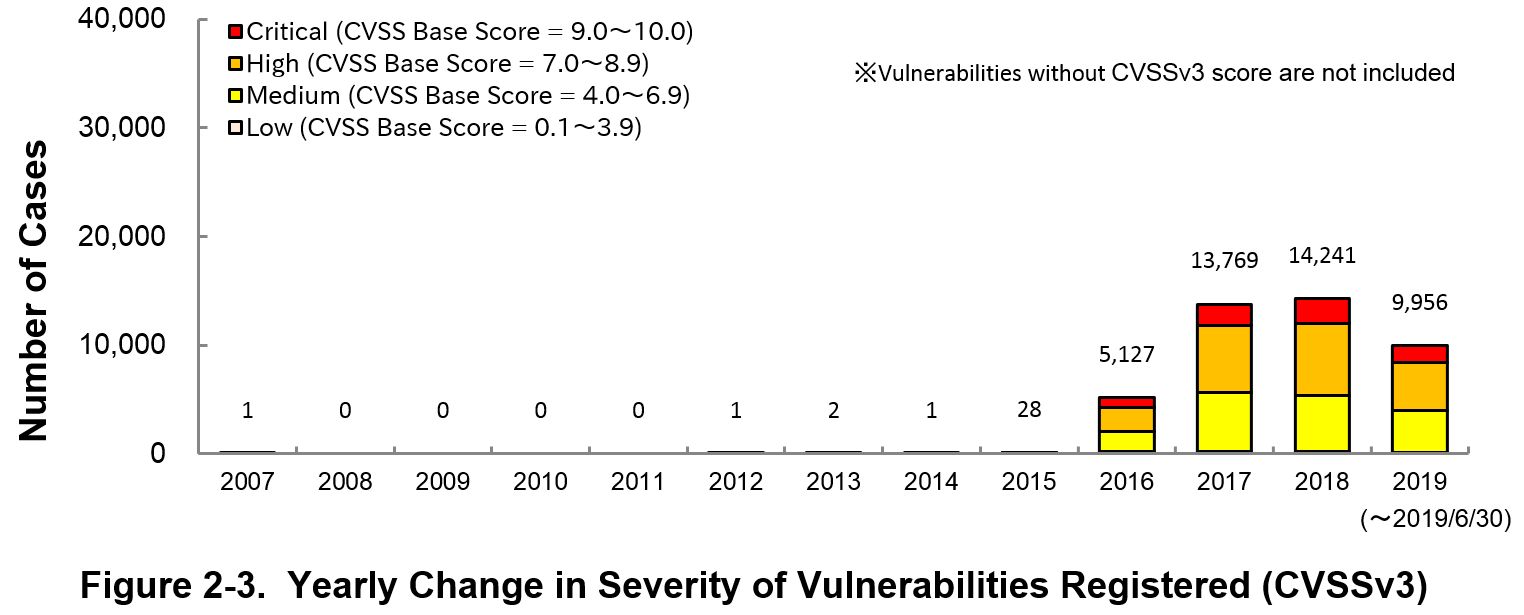
Figure 2-3 shows the yearly change in the CVSSv3 rating scale based severity of vulnerabilities registered to JVN iPedia.
As for the vulnerabilities added to JVN iPedia in 2019, 16.0 percent are “Critical” (9.0 – 10.0), 44.0 percent are “High” (7.0 – 8.9), 39.1 percent are “Medium” (4.0 – 6.9) and 0.9 percent are “Low” (0.1 – 3.9).
To avoid threats posed by the known vulnerabilities, both product developers and IT users should pay close attention to vulnerability disclosure and update software they use to a fixed version or apply a security patch as soon as possible when they become available. IT users can check vulnerabilities newly published on JVN iPedia in RSS and XML format (*7) as well.
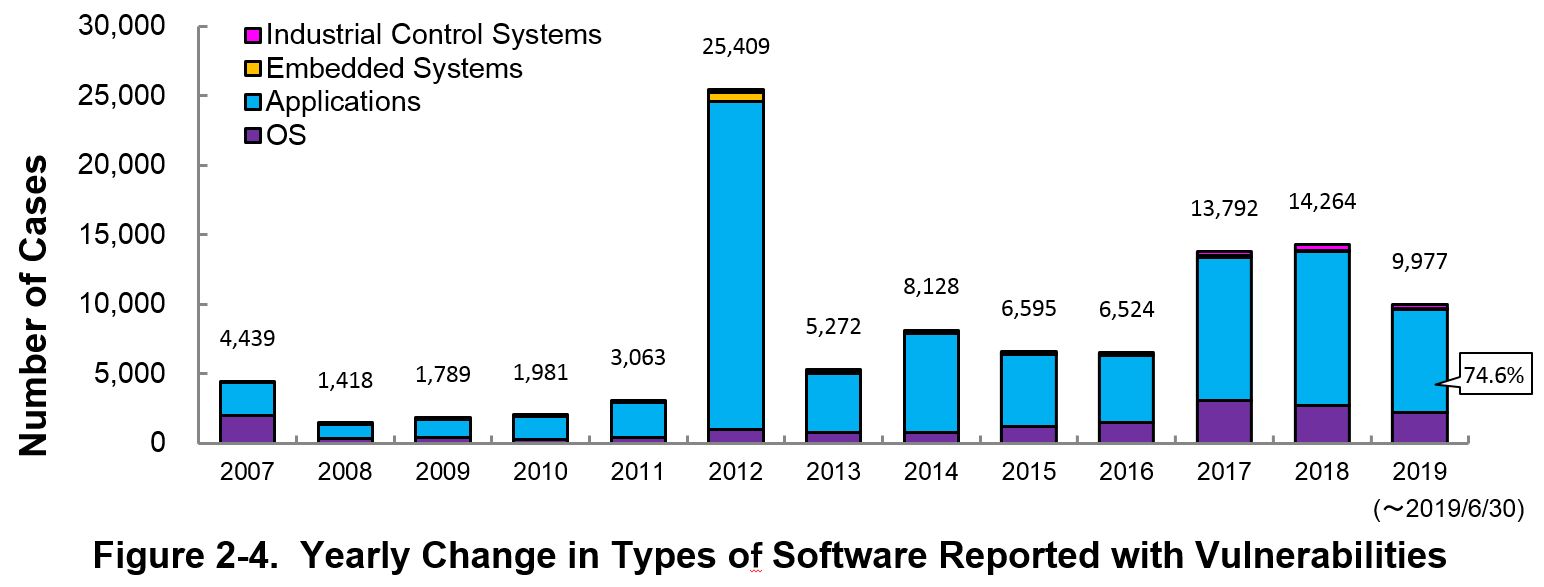
2-3. Types of Software Reported with Vulnerability
Figure 2-4 shows the yearly change in the type of software reported with vulnerability. Application vulnerabilities have been published most, accounting for 74.6 percent (7,445 out of 9,977) of the 2019 total.
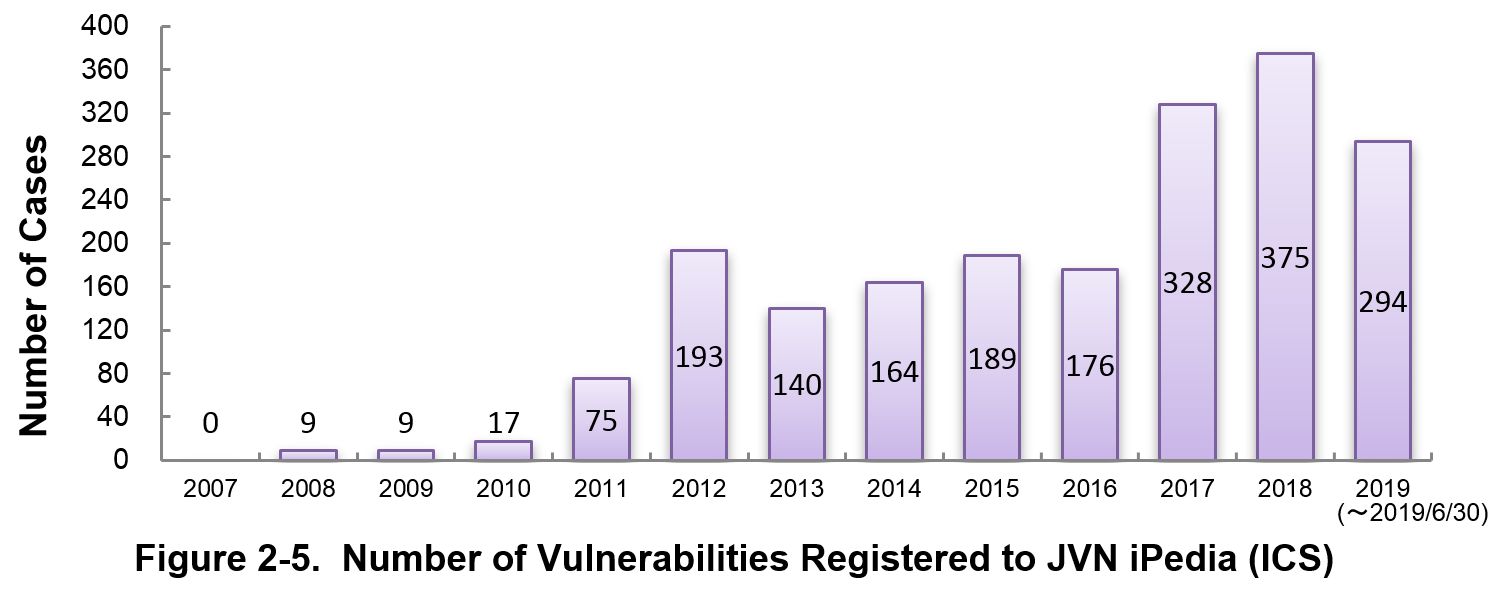
Figure 2-5 shows the yearly change in the number of JVN iPedia-stored vulnerabilities in industrial control systems (ICS) used in critical infrastructure sectors. As of June 2019, the total of 1,969 ICS vulnerabilities have been registered.
2-4. Products Reported with Vulnerability
Table 2-1 lists the top 20 software whose vulnerabilities were most registered to JVN iPedia during the 2nd quarter (April to June) of 2019.
In this quarter, large number of vulnerability countermeasure information related to OS products have been registered and which accounts for over 70% of the total. Of the top 20 cases, 9 are Microsoft OS, 4 are Apple OS, and 2 are Linux-based OS.
Besides those in the top 20 list, JVN iPedia stores and offers vulnerability information about a variety of software. IPA hopes software developers and users will make good use of JVN iPedia to efficiently check vulnerability information and take necessary action in a timely manner (*8).
Table 2-1. Top 20 Software Products Vulnerabilities Were Most Registered [Apr. – Jun. 2019]
|
Rank
|
Category
|
Product Name (Vendor)
|
Number of
Vulnerabilities Registered |
|---|---|---|---|
|
1
|
OS
|
Microsoft Windows 10 (Microsoft)
|
178
|
|
2
|
OS
|
Microsoft Windows Server (Microsoft)
|
176
|
|
3
|
PDF Viewer
|
Adobe Acrobat Reader DC (Adobe Systems)
|
175
|
|
3
|
PDF Viewer/Editor
|
Adobe Acrobat DC (Adobe Systems)
|
175
|
|
3
|
PDF Viewer/Editor
|
Adobe Acrobat (Adobe Systems)
|
175
|
|
6
|
OS
|
Microsoft Windows Server 2019 (Microsoft)
|
167
|
|
7
|
OS
|
iOS (Apple)
|
157
|
|
8
|
OS
|
Microsoft Windows Server 2016 (Microsoft)
|
152
|
|
9
|
OS
|
Microsoft Windows Server 2008 (Microsoft)
|
141
|
|
10
|
OS
|
Microsoft Windows 7 (Microsoft)
|
140
|
|
11
|
OS
|
Microsoft Windows Server 2012 (Microsoft)
|
136
|
|
12
|
OS
|
Microsoft Windows 8.1 (Microsoft)
|
133
|
|
13
|
OS
|
Microsoft Windows RT 8.1 (Microsoft)
|
130
|
|
14
|
OS
|
tvOS (Apple)
|
110
|
|
15
|
OS
|
Apple Mac OS X (Apple)
|
108
|
|
16
|
Network Management Software
|
HPE Intelligent Management Center (Hewlett Packard Enterprise)
|
104
|
|
17
|
OS
|
Debian GNU/Linux (Debian)
|
100
|
|
18
|
OS
|
watchOS (Apple)
|
95
|
|
19
|
Firmware
|
Qualcomm component (Qualcomm)(*9)
|
91
|
|
20
|
OS
|
Ubuntu (Canonical)
|
86
|
3. Most Accessed Vulnerability Countermeasure Information
Table 3-1 lists the top 20 most accessed vulnerability information in JVN iPedia during the 2nd quarter of 2019 (April to June).
Of the vulnerability countermeasure information ranked high in this quarter, the 3rd and 19th rank were collected from domestic product developers. Except for the above two and the 4th rank, 17 are vulnerability countermeasure information released on the Vulnerability Countermeasure Information Portal Site JVN. Those products registered in the vulnerability countermeasure information have many domestic users and receive a lot of attention so that the number of access the relevant web site tend to increase.
Rating Scale
Note 1) CVSSv2 Severity Rating Scale
- Level I (Low)
- CVSS Base Score = 0.0~3.9
- Level II (Medium)
- CVSS Base Score = 4.0~6.9
- Level III (High)
- CVSS Base Score = 7.0~10.0
Note 2) CVSSv3 Severity Rating Scale
- Low
- CVSS Base Score =0.1~3.9
- Medium
- CVSS Base Score =4.0~6.9
- High
- CVSS Base Score =7.0~8.9
- Critical
- CVSS Base Score =9.0~10.0
Table 3-1. Top 20 Most Accessed Vulnerability Countermeasure Information in JVN iPedia [Apr. – Jun. 2019]
No.1 GNU Wget vulnerable to buffer overflow JVNDB-2019-000022
- CVSSv2 Severity Rating Scale
-
- Level II (Medium)
- CVSSv2 Base Score
-
6.8
- CVSSv3 Severity Rating Scale
-
- High
- CVSSv3 Base Score
-
8.8
- Date Public
-
2019/4/3
- Access Count
-
10,020
No.2 API server used by JR East Japan train operation information push notification App for Android fails to restrict access permissions JVNDB-2019-000021
- CVSSv2 Severity Rating Scale
-
- Level II (Medium)
- CVSSv2 Base Score
-
6.4
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
6.5
- Date Public
-
2019/4/1
- Access Count
-
8,754
No.3 Multiple Vulnerabilities in Cosminexus JVNDB-2019-002892
- CVSSv2 Base Score
-
-
- CVSSv3 Base Score
-
-
- Date Public
-
2019/4/25
- Access Count
-
8,750
No.4 Cross-site Scripting Vulnerability in OpenKM JVNDB-2014-007972
- CVSSv2 Severity Rating Scale
-
Level I (Low)
- CVSSv2 Base Score
-
3.5
- CVSSv3 Base Score
-
-
- Date Public
-
2015/3/13
- Access Count
-
7,915
No.5 The installer of Microsoft Teams may insecurely load Dynamic Link Libraries JVNDB-2019-000014
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
6.8
- CVSSv3 Severity Rating Scale
-
High
- CVSSv3 Base Score
-
7.8
- Date Public
-
2019/2/28
- Access Count
-
7,419
No.6 PowerAct Pro Master Agent for Windows fails to restrict access permissions JVNDB-2019-000020
- CVSSv2 Severity Rating Scale
-
- Level I (Low)
- CVSSv2 Base Score
-
1.7
- CVSSv3 Severity Rating Scale
-
- Low
- CVSSv3 Base Score
-
3.3
- Date Public
-
2019/3/27
- Access Count
-
7,320
No.7 Multiple vulnerabilities in Cybozu Garoon JVNDB-2019-000023
- CVSSv2 Severity Rating Scale
-
- Level II (Medium)
- CVSSv2 Base Score
-
6.5
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
6.0
- Date Public
-
2019/4/25
- Access Count
-
7,292
No.8 "an" App for iOS vulnerable to directory traversal JVNDB-2019-000018
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
4.3
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
4.7
- Date Public
-
2019/3/19
- Access Count
-
7,157
No.9 KinagaCMS vulnerable to cross-site scripting JVNDB-2019-000019
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
4.3
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
6.1
- Date Public
-
2019/3/15
- Access Count
-
6,774
No.10 iChain Insurance Wallet App for iOS vulnerable to directory traversal JVNDB-2019-000015
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
4.3
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
4.7
- Date Public
-
2019/3/12
- Access Count
-
6,622
No.11 Cybozu Garoon vulnerable to directory traversal JVNDB-2018-000099
- CVSSv2 Severity Rating Scale
-
- Level II (Medium)
- CVSSv2 Base Score
-
5.5
- CVSSv3 Severity Rating Scale
-
- Medium
- CVSSv3 Base Score
-
6.4
- Date Public
-
2018/9/10
- Access Count
-
6,238
No.12 Cybozu Garoon access restriction bypass vulnerability JVNDB-2018-000130
- CVSSv2 Severity Rating Scale
-
- evel II (Medium)
- CVSSv2 Base Score
-
5.0
- CVSSv3 Severity Rating Scale
-
High
- CVSSv3 Base Score
-
7.5
- Date Public
-
2018/12/10
- Access Count
-
6,081
No.13 Dradis Community Edition and Dradis Professional Edition vulnerable to cross-site scripting JVNDB-2019-000017
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
4.0
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
5.4
- Date Public
-
2019/3/5
- Access Count
-
6,072
No.14 Multiple vulnerabilities in NablarchJVNDB-2019-000012
- CVSSv2 Severity Rating Scale
-
Level III (High)
- CVSSv2 Base Score
-
8.5
- CVSSv3 Severity Rating Scale
-
High
- CVSSv3 Base Score
-
8.2
- Date Public
-
2019/2/27
- Access Count
-
6,067
No.15 Windows 7 may insecurely load Dynamic Link Libraries JVNDB-2019-000013
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
6.8
- CVSSv3 Severity Rating Scale
-
High
- CVSSv3 Base Score
-
7.8
- Date Public
-
2019/2/28
- Access Count
-
6,024
No.16 WordPress plugin "Smart Forms" vulnerable to cross-site request forgery JVNDB-2019-000016
- CVSSv2 Severity Rating Scale
-
- Level I (Low)
- CVSSv2 Base Score
-
2.6
- CVSSv3 Severity Rating Scale
-
- Medium
- CVSSv3 Base Score
-
4.3
- Date Public
-
2019/2/28
- Access Count
-
5,933
No.17 WordPress plugin "FormCraft" vulnerable to cross-site request forgery JVNDB-2019-000011
- CVSSv2 Severity Rating Scale
-
- Level I (Low)
- CVSSv2 Base Score
-
2.6
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
4.3
- Date Public
-
2019/2/26
- Access Count
-
5,840
No.18 azure-umqtt-c vulnerable to denial-of-service (DoS) JVNDB-2019-000010
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
5.0
- CVSSv3 Severity Rating Scale
-
High
- CVSSv3 Base Score
-
7.5
- Date Public
-
2019/2/20
- Access Count
-
5,724
No.19 DoS Vulnerability in JP1/Base JVNDB-2019-001285
- CVSSv2 Base Score
-
-
- CVSSv3 Base Score
-
-
- Date Public
-
2019/2/25
- Access Count
-
5,709
No.20 Installer of Adobe Creative Cloud Desktop Application may insecurely load Dynamic Link Libraries JVNDB-2019-000009
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
6.8
- CVSSv3 Severity Rating Scale
-
High
- CVSSv3 Base Score
-
7.8
- Date Public
-
2019/2/18
- Access Count
-
5,665
Table 3-2 lists the top 5 most accessed vulnerability information among those reported by domestic product developers.
Table 3-2. Top 5 Most Accessed Vulnerabilities Reported by Domestic Product Developers [Apr. - Jun. 2019]
No.1 Multiple Vulnerabilities in Cosminexus JVNDB-2019-002892
- CVSSv2 Base Score
-
- -
- CVSSv3 Base Score
-
- -
- Date Public
-
2019/4/25
- Access Count
-
8,750
No.2 DoS Vulnerability in JP1/Base JVNDB-2019-001285
- CVSSv2 Base Score
-
- -
- CVSSv3 Base Score
-
-
- Date Public
-
2019/2/25
- Access Count
-
5,709
No.3 Information Disclosure Vulnerability in Hitachi Command Suite and Hitachi Infrastructure Analytics Advisor JVNDB-2019-001094
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
5.0
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
5.3
- Date Public
-
2019/1/22
- Access Count
-
5,376
No.4 Problem with directory permissions in JP1/Operations Analytics JVNDB-2018-010027
- CVSSv2 Severity Rating Scale
-
Medium
- CVSSv2 Base Score
-
3.5
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
4.9
- Date Public
-
2018/12/4
- Access Count
-
5,255
No.5 Clickjacking Vulnerability in Hitachi Automation Director JVNDB-2018-010851
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
4.3
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
4.3
- Date Public
-
2018/12/26
- Access Count
-
5,101
Footnotes
-
(*1)
-
(*2)
-
(*3)
-
(*4)
-
(*5)
-
(*6)
-
(*7)
-
(*8)
-
(*9)'Qualcomm Firmware' contains various firmware of Qualcomm processors such as SD and MSM series.
Past Quarterly Reports
Contact information
IT Security Center, Information-technology Promotion Agency, Japan (ISEC/IPA)