アーカイブ

IPA/ISEC:Vulnerabilities:OVAL (Open Vulnerability and Assessment Language) Overview
The standard for determining vulnerability and configuration issues on computer systems.
November 30, 2009
IT Security Center
Information-technology Promotion Agency, Japan
>> JAPANESE
OVAL (Open Vulnerability and Assessment Language)(*1) is a security assessment language for checking security configuration of computers.
OVAL is one of the elements that constitute SCAP (Security Content Automation Protocol)(*2), which allows the automation and standardization of technical approaches in the field of information security promoted by the U.S. government.
MITRE(*3), a non-profit organization supported by the U.S. government, led the effort in developing the specifications and introduced OVAL at SANS Network Security 2002 in October the same year as a language to enable automatic assessment of vulnerability and security of computers.
Since 2007, the enhancements have been made through its use in FDCC (Federal Desktop Core Configuration)(*4), a U.S. federal government mandate standard for desktop configuration.
When a software vulnerability is reported, its users need to assess whether said vulnerability exists in one’s own computers based on the vulnerability countermeasure information released by software providers or security vendors and it’s still manually done in many cases.
OVAL enables to provide the vulnerability countermeasure information in an XML-based, machine-readable format written in the OVAL language. The vulnerability information written in the OVAL language, called the OVAL Definition, can be processed automatically by an interpreter program called the OVAL Interpreter, enabling automated assessment of vulnerability.
Moreover, the OVAL Definitions are provided as a database called the OVAL Repository to encourage their better. By automating the vulnerability assessment, OVAL saves administrative time and cost to manage vulnerability.
It also helps prevent human error of missing vulnerability due to paper-based, manual checking of vulnerability, and is useful for management of information assets and systems.
This document is produced based on the OVAL Version 5.6 released by MITRE on November 11, 2009, and the OVAL Repository. For more details, please refer to the official documents and the OVAL Repository.
1. OVAL Language
To use OVAL, the OVAL Definition which describes the assessment procedures in the OVAL language, and the OVAL Interpreter that interprets and executes the procedures listed in the OVAL Definition.
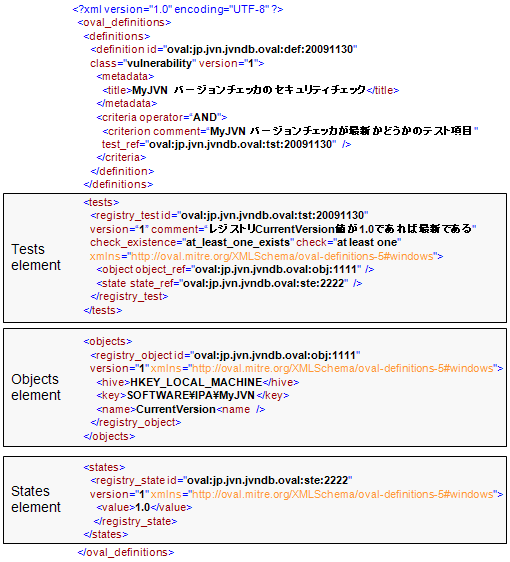
The OVAL Language is an XML specification to describe the assessment procedures of security problems in computer programs and configurations. A OVAL Definition consists of three elements: tests, objects and states (Figure 1).
The Objects is an element to specify check items such as a file and registry. The States is an element that suggests a value supposed to be held by the check items set in the Objects element. The Tests is an element to specify the Objects fields and States fields to be used in the checking.
The OVAL Interpreter looks up the value of a check item pointed in the Objects element and compares it to the value set by the corresponding States element, assessing whether a computer has security problems with its programs or configurations.
Since the assessment procedures differ depending on OS and application, the OVAL Language allows adding of system-dependent characteristics to specify the appropriate procedures for the OS or application to be tested.
For OS, the OVAL Version 5.6 defines system characteristics of Apple Macintosh, Cisco CatOS, Cisco IOS, Cisco PixOS, FreeBSD, HP-UX, IBM AIX, Linux, Microsoft Windows, Sun Solaris and UNIX.
As for applications, Apache and SharePoint are defined and VMwareESX is also supported as a virtual machine environment.
Figure 1. Example of OVAL Definition written in OVAL Language
2. OVAL Repository
OVAL Repository hosted by MITRE is a database of OVAL Definitions supported by the OVAL Community, which consists of those involved in OVAL. As of the end of November 2009, approximately 3,000 OVAL Definitions for vulnerability assessment are stored in the Repository.
MITRE adopts CVE(*5), a unique vulnerability identifier, and CPE(*6), a unique system platform identifier, in writing OVAL definitions and provide them at the Repository website ( http://oval.mitre.org/repository/ )(Figure 2).
Since 2006, Red Hat has been providing the OVAL Definition data that allow its users to assess whether they need to apply security patch released by Red Hat in response to the security problems made public in its security advisories.
In 2007, NIST(*7) started to offer the OVAL Definition data to assess software security configuration and vulnerability in part promoting SCAP ( http://nvd.nist.gov/scap/scap.cfm ).
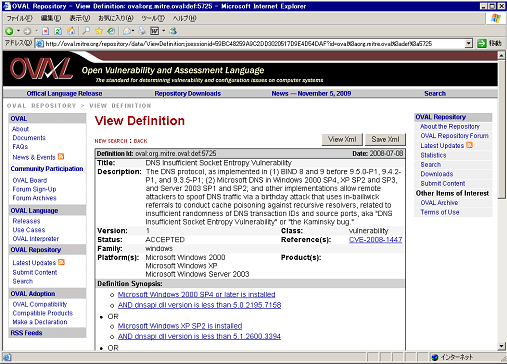
Figure 2. OVAL Definition data offered on OVAL Repository
3. IPA Support of OVAL
In these days, way of virus and bot infection is getting more and more sophisticated and it is critical to keep OS, applications, plug-in tools like ActiveX, virus definition file latest.
As FDCC published by NIST for reference, IPA developed a software version check tool MyJVN Version Checker(*8). It checks whether software installed on the users’ computers is up-to-date.
The software MyJVN Version Checker will assess is those which are registered in the vulnerability countermeasure database JVN iPedia ( http://jvndb.jvn.jp/en/ )(*9) and those which seem to be a good target of virus/bot attack.
MyJVN Version Checker works as an OVAL Interpreter. By assessing what kind of software is installed on the computer and their version with the OVAL Definition data written in the OVAL Language, MyJVN Version Checker enables vendor-independent software version assessment.
Also, MyJVN Version Checker uses CPE as a platform identifier, and allows the users to cross-reference vulnerability countermeasure information published on JVN iPedia.
IPA will collaborate with OVAL Repository and relevant organizations, such as NIST, and MITRE. By providing more OVL Definitions written in OVAL Language, IPA will keep working on how to provide vulnerabilities and infrastructure that helps users take objective and efficient countermeasures against security vulnerabilities.
Footnote
(*1)OVAL: Open Vulnerability and Assessment Language. Language specification to assess security configurations.
http://oval.mitre.org/
(*2)SCAP: Security Content Automation Protocol. A set of technical specifications supported by the U.S. government to promote standardization and automation of information security implementation.
http://nvd.nist.gov/scap.cfm
(*3)MITRE Corporation: A not-for-profit organization that provides information technology support and research and development to the U.S. government.
http://www.mitre.org/
(*4)FDCC: Federal Desktop Core Configuration. A mandated security standard that requires all federal agencies standardize the minimum configuration of PC settings.
http://nvd.nist.gov/fdcc/index.cfm
(*5)CVE: Common Vulnerabilities and Exposures. A unique, common identifier used to distinguish vulnerabilities.
http://cve.mitre.org
(*6)CPE: Common Platform Enumeration. a list of standard IT platform names designated to identify each IT platform.
http://cpe.mitre.org/
(*7)NIST: National Institute of Standards and Technology. A U.S federal agency that develops and promotes measurement, standards and technology.
http://www.nist.gov/
(*8)Release of Version Check Tool "MyJVN Version Checker"
http://www.ipa.go.jp/security/english/vuln/200911_myjvn_vc_en.html
(*9)JVN iPedia: Vulnerability countermeasure information database mainly for those concerning products popularly used in Japan. Collect, Store and release information.
http://jvndb.jvn.jp/en/
Reference
- CVE (Common Vulnerabilities and Exposures) Overview
http://www.ipa.go.jp/security/english/vuln/CVE_en.html - CPE (Common Platform Enumeration) Overview
http://www.ipa.go.jp/security/english/vuln/CPE_en.html - CWE (Common Weakness Enumeration) Overview
http://www.ipa.go.jp/security/english/vuln/CWE_en.html
Contact
IT Security Center,
Information-technology Promotion Agency, Japan (ISEC/IPA)
E-mail: ![]()