Enhancing information security
Vulnerability Countermeasure Information Database JVN iPedia Registration Status [2022 3rd Quarter (Jul. - Sep.)]
Release Date:Nov 22, 2022
IT Security Center
1. 2022 3rd Quarter: Vulnerability Countermeasure Information Database JVN iPedia Registration Status
The vulnerability countermeasure information database JVN iPedia is endeavoring to become a comprehensive vulnerability database where vulnerability information is aggregated for easy access for IT users. JVN iPedia collects and/or translates the vulnerability information published by 1) domestic software developers, 2) JVN (footnote 1), a vulnerability information portal run by JPCERT/CC and IPA, and 3) NVD (footnote 2), a vulnerability database run by NIST (footnote 3). JVN iPedia has been making vulnerability information available to the public since April 25, 2007.
1-1. Vulnerabilities Registered in 2022/3Q
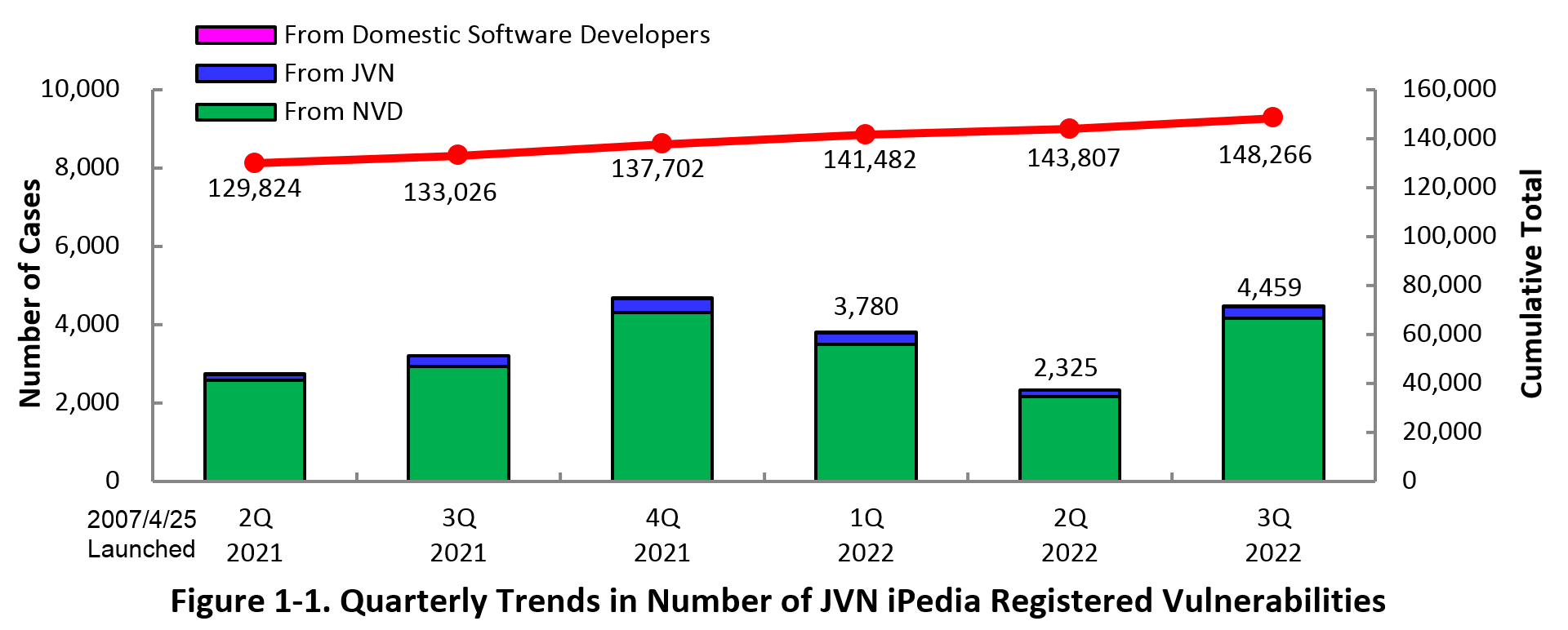
The summary of the vulnerability information registered to the Japanese version of JVN iPedia during the 3rd quarter of 2022 (July 1 to September 30, 2022) is shown in the table below. As of the end of September 2022, the total number of vulnerabilities stored in JVN iPedia is 148,266 (Table 1-1, Figure 1-1).
As for the JVN iPedia English version, the total number of vulnerabilities stored is 2,483 as shown in the lower half of the Table 1-1.
Table 1-1. Vulnerabilities Registered to JVN iPedia during 3rd Quarter of 2022
|
|
Information Source
|
Registered Cases
|
Cumulative Cases
|
|---|---|---|---|
|
Japanese Version
|
Domestic Product Developers
|
2 cases
|
266 cases
|
|
JVN
|
305 cases
|
11,654 cases
|
|
|
NVD
|
4,152 cases
|
136,346 cases
|
|
|
Total
|
4,459 cases
|
148,266 cases
|
|
|
English Version
|
Domestic Product Developers
|
2 cases
|
261 cases
|
|
JVN
|
34 cases
|
2,222 cases
|
|
|
Total
|
36 cases
|
2,483 cases
|
2. Details on JVN iPedia Registered Data
2-1. Types of Vulnerabilities Reported
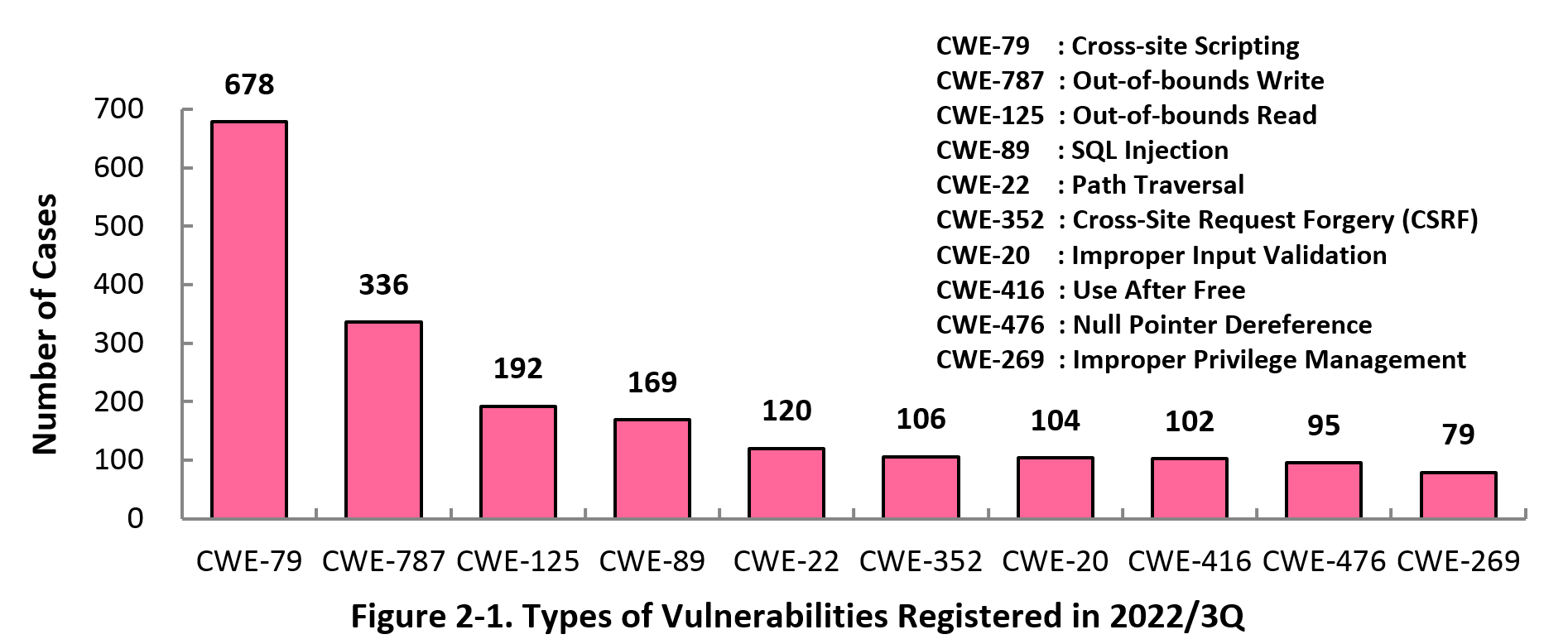
Figure 2-1 shows the number of vulnerabilities newly added to JVN iPedia during the 3rd quarter of 2022, sorted by the CWE vulnerability types.
The type of the vulnerabilities reported most in the 1st quarter is CWE-79 (Cross-Site Scripting) with 678 cases, followed by CWE-787 (Out-of-bounds Write) with 336, CWE-125 (Out-of-bounds Read) with 192, CWE-89 (SQL Injection) with 169, CWE-22 (Path Traversal) with 120. CWE-79 (Cross-site Scripting), the most reported vulnerability type in this quarter, could allow attackers to display false webpages and/or steal information.
Software developers need to make sure to mitigate vulnerability from the planning and design phase of software development. IPA provides tools and guidelines, such as "Vulnerability Countermeasure Guide for Software Developers"" (footnote 4), "How to Secure Your Website" (footnote 5), "Secure Programming Guide" (footnote 6) and "AppGoat" (footnote 7), a hands-on venerability learning tool, for website developers and operators to build secure websites.
2-2. Severity of Vulnerabilities Reported
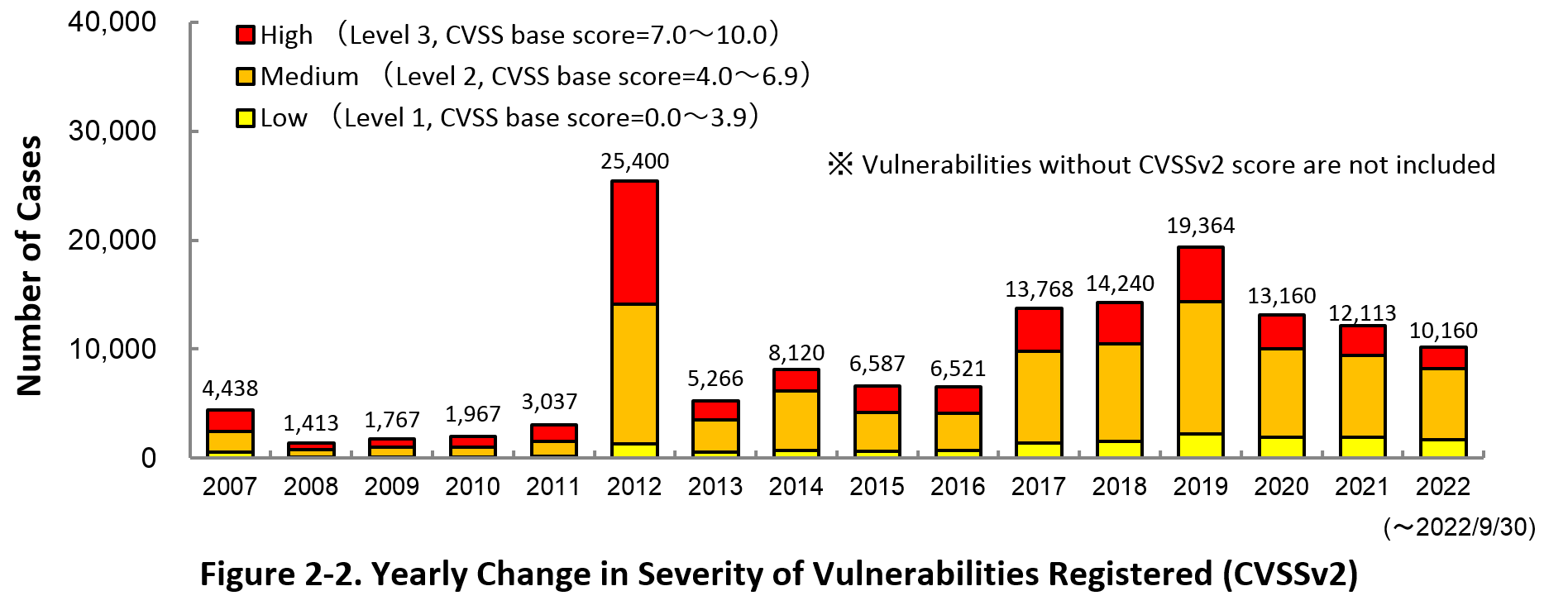
Figure 2-2 shows the yearly change in the CVSSv2 rating scale based severity of vulnerabilities registered to JVN iPedia.
As for the vulnerabilities added to JVN iPedia in 2022, 19.1 percent are “Level 3” (7.0 - 10.0), 64.7 percent are “Level 2” (4.0 – 6.9) and 16.2 percent are “Level 1” (0.0 – 3.9). This means 83.8 percent of all vulnerabilities registered are Level 2 or higher, which are potentially critical enough to cause damage like information exposure or data falsification.
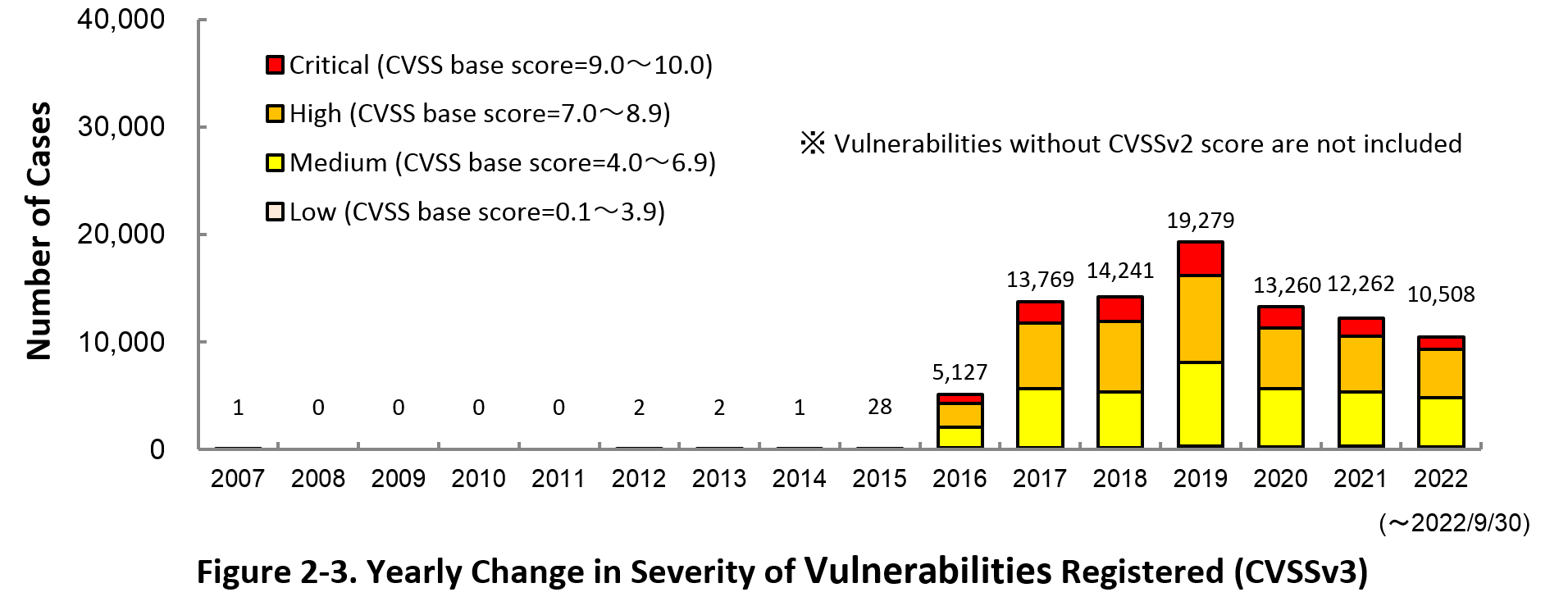
Figure 2-3 shows the yearly change in the CVSSv3 rating scale based severity of vulnerabilities registered to JVN iPedia.
As for the vulnerabilities added to JVN iPedia in 2022, 11.5 percent are “Critical” (9.0 – 10.0), 42.4 percent are “High” (7.0 – 8.9), 43.6 percent are “Medium” (4.0 – 6.9) and 2.4 percent are “Low” (0.1 – 3.9).
To avoid threats posed by the known vulnerabilities, both product developers and IT users should pay close attention to vulnerability disclosure and update software they use to a fixed version or apply a security patch as soon as possible when they become available. IT users can check vulnerabilities newly published on JVN iPedia in RSS and XML format (footnote 8) as well.
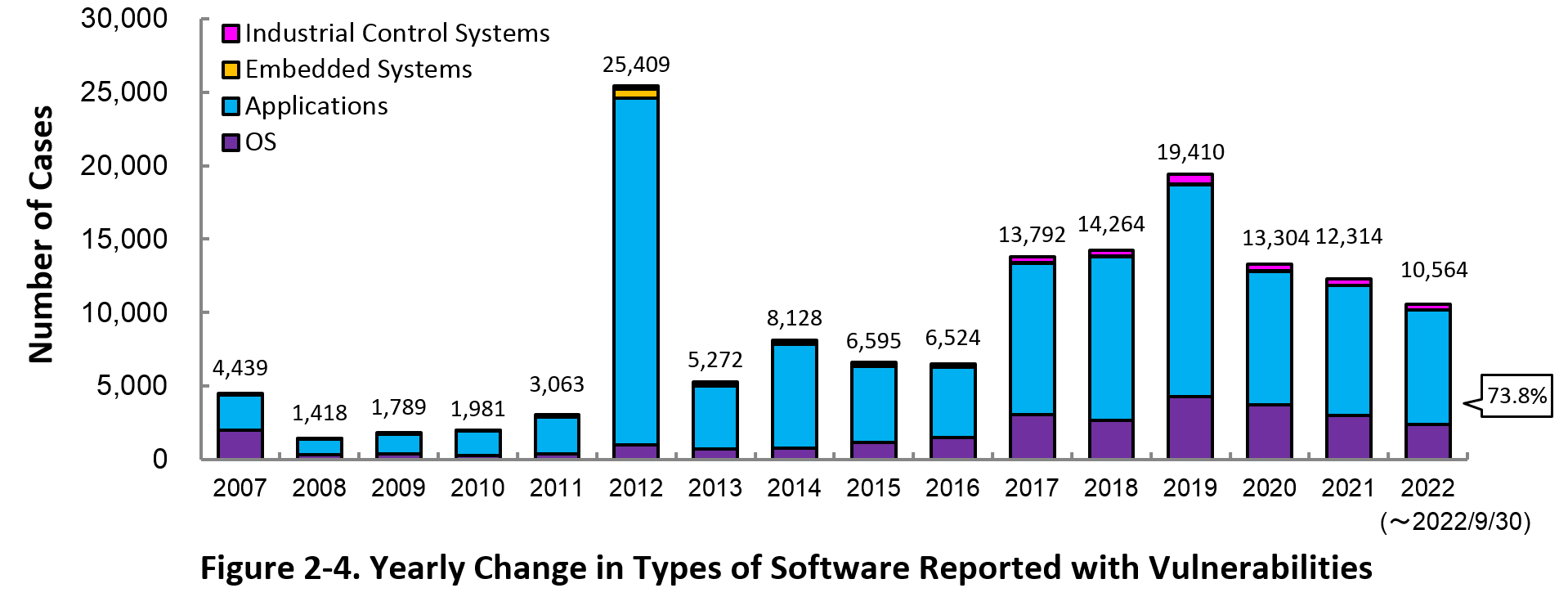
2-3. Types of Software Reported with Vulnerability
Figure 2-4 shows the yearly change in the type of software reported with vulnerability. Application vulnerabilities have been published most, accounting for 73.8 percent (7,793 out of 10,564) of the 2022 total.
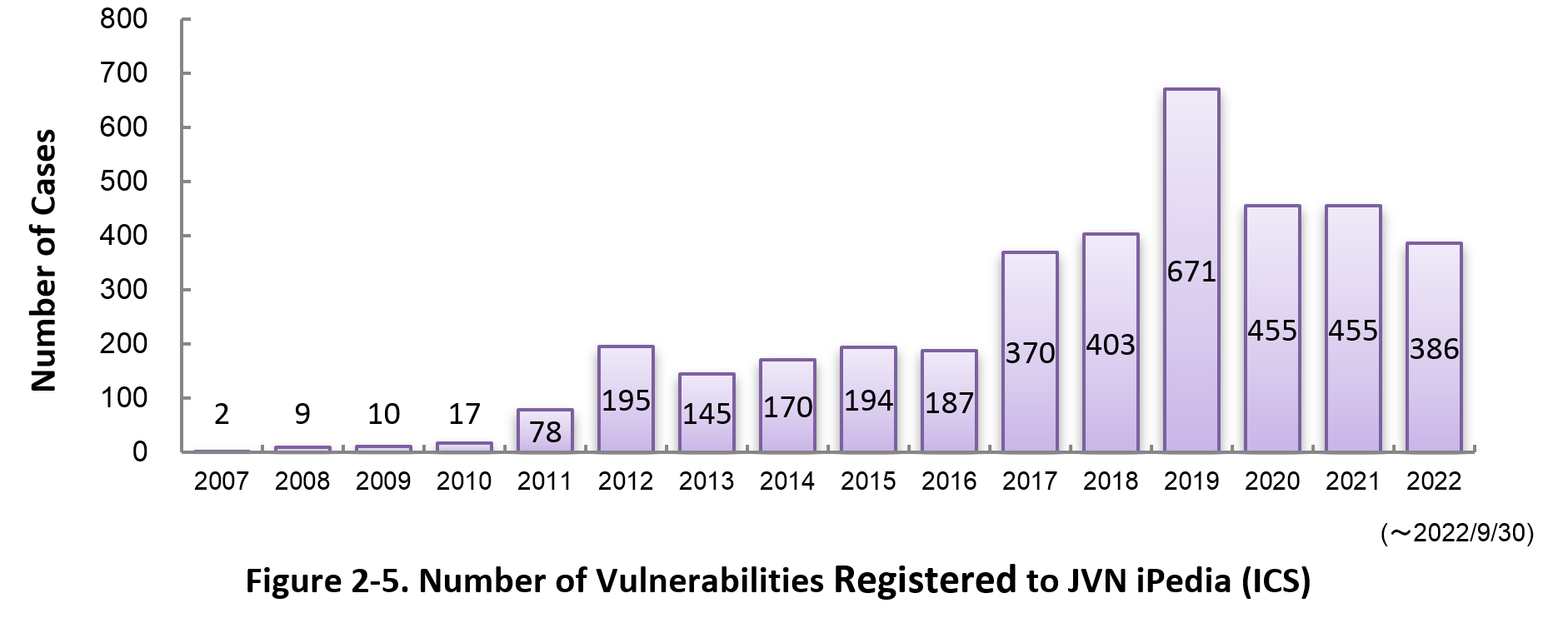
Figure 2-5 shows the yearly change in the number of JVN iPedia-stored vulnerabilities in industrial control systems (ICS) used in critical infrastructure sectors. As of September 2022, the total of 3,747 ICS vulnerabilities have been registered.
2-4. Products Reported with Vulnerability
Table 2-1 lists the top 20 software whose vulnerabilities were most registered to JVN iPedia during the 3rd quarter (July to September) of 2022.
In this quarter, the most registered products were Qualcomm products which continued from previous quarter, with 680 cases. This is due to the registration of vulnerability information for multiple Qualcomm products which was published in 2021. In addition, OS products of Apple, Microsoft, etc. ranked from 2nd to 20th.
Besides those in the top 20 list, JVN iPedia stores and offers vulnerability information about a variety of software. IPA hopes software developers and users will make good use of JVN iPedia to efficiently check vulnerability information and take necessary action in a timely manner (footnote 9).
Table 2-1. Top 20 most registered software products vulnerability countermeasure information in JVN iPedia [Jul. – Sep. 2022]
|
Rank
|
Category
|
Product Name (Vendor)
|
Number of
Vulnerabilities Registered |
|---|---|---|---|
|
1
|
Firmware
|
Qualcomm component (Qualcomm)
|
680
|
|
2
|
OS
|
macOS (Apple)
|
276
|
|
3
|
OS
|
iOS (Apple)
|
248
|
|
4
|
OS
|
Apple Mac OS X (Apple)
|
228
|
|
5
|
OS
|
iPadOS (Apple)
|
224
|
|
6
|
OS
|
Fedora (Fedora Project)
|
200
|
|
7
|
OS
|
Debian GNU/Linux (Debian)
|
188
|
|
8
|
OS
|
watchOS (Apple)
|
170
|
|
9
|
OS
|
tvOS (Apple)
|
166
|
|
10
|
OS
|
Microsoft Windows Server 2022 (Microsoft)
|
128
|
|
11
|
OS
|
Microsoft Windows Server 2019 (Microsoft)
|
125
|
|
12
|
OS
|
Android (Google)
|
121
|
|
13
|
OS
|
Microsoft Windows 10 (Microsoft)
|
120
|
|
14
|
OS
|
Microsoft Windows Server 2016 (Microsoft)
|
118
|
|
15
|
OS
|
Microsoft Windows 11 (Microsoft)
|
116
|
|
16
|
OS
|
Microsoft Windows Server 2012 (Microsoft)
|
95
|
|
17
|
OS
|
Microsoft Windows Server 2008 (Microsoft)
|
89
|
|
18
|
OS
|
Microsoft Windows 8.1 (Microsoft)
|
88
|
|
19
|
OS
|
Microsoft Windows RT 8.1 (Microsoft)
|
85
|
|
20
|
OS
|
Microsoft Windows Server (Microsoft)
|
84
|
3. Most Accessed Vulnerability Countermeasure Information
Table 3-1 lists the top 20 most accessed vulnerability countermeasure information in JVN iPedia during the 3rd quarter of 2022 (July to September).
In this quarter, all the ranked vulnerability countermeasure information in top 20 was published in 2022. In addition, 13 of the top 20 were vulnerabilities related to Microsoft products.
Rating Scale
Note 1) CVSSv2 Severity Rating Scale
- Level I (Low)
- CVSS Base Score = 0.0~3.9
- Level II (Medium)
- CVSS Base Score = 4.0~6.9
- Level III (High)
- CVSS Base Score = 7.0~10.0
Note 2) CVSSv3 Severity Rating Scale
- Low
- CVSS Base Score =0.1~3.9
- Medium
- CVSS Base Score =4.0~6.9
- High
- CVSS Base Score =7.0~8.9
- Critical
- CVSS Base Score =9.0~10.0
Table 3-1. Top 20 Most Accessed Vulnerability Countermeasure Information in JVN iPedia [Jul. – Sep. 2022]
No.1 LiteCart vulnerable to cross-site scripting JVNDB-2022-000050
- CVSSv2 Severity Rating Scale
-
- Level I (Low)
- CVSSv2 Base Score
-
2.6
- CVSSv3 Severity Rating Scale
-
- Medium
- CVSSv3 Base Score
-
6.1
- Date Public
-
2022/7/4
- Access Count
-
6,617
No.2 Multiple vulnerabilities in Cybozu Garoon JVNDB-2022-000051
- CVSSv2 Severity Rating Scale
-
- Level II (Medium)
- CVSSv2 Base Score
-
5.5
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
5.4
- Date Public
-
2022/7/4
- Access Count
-
5,932
No.3 Passage Drive vulnerable to insufficient data verification JVNDB-2022-000052
- CVSSv2 Severity Rating Scale
-
Level III (High)
- CVSSv2 Base Score
-
9.3
- CVSSv3 Severity Rating Scale
-
High
- CVSSv3 Base Score
-
8.6
- Date Public
-
2022/7/8
- Access Count
-
5,620
No.4 Django Extract and Trunc functions vulnerable to SQL injection JVNDB-2022-000053
- CVSSv2 Severity Rating Scale
-
Level III (High)
- CVSSv2 Base Score
-
7.5
- CVSSv3 Severity Rating Scale
-
High
- CVSSv3 Base Score
-
7.3
- Date Public
-
2022/7/12
- Access Count
-
5,615
No.5 Microsoft Windows Server vulnerable to remote code execution JVNDB-2022-001978
- CVSSv2 Severity Rating Scale
-
Level III (High)
- CVSSv2 Base Score
-
10.0
- CVSSv3 Severity Rating Scale
-
Critical
- CVSSv3 Base Score
-
9.8
- Date Public
-
2022/6/30
- Access Count
-
5,589
No.6 Multiple Microsoft Windows products vulnerable to remote code execution JVNDB-2022-002004
- CVSSv2 Severity Rating Scale
-
- Level II (Medium)
- CVSSv2 Base Score
-
6.8
- CVSSv3 Severity Rating Scale
-
- High
- CVSSv3 Base Score
-
8.8
- Date Public
-
2022/6/30
- Access Count
-
5,282
No.7 U-Boot squashfs filesystem implementation vulnerable to heap-based buffer overflow JVNDB-2022-002017
- CVSSv2 Base Score
-
-
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
6.6
- Date Public
-
2022/7/14
- Access Count
-
5,256
No.8 Multiple Microsoft Windows products vulnerable to denial-of-service (DoS) JVNDB-2022-002003
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
5.0
- CVSSv3 Severity Rating Scale
-
High
- CVSSv3 Base Score
-
7.5
- Date Public
-
2022/6/30
- Access Count
-
5,251
No.9 Multiple Microsoft Windows products vulnerable to denial-of-service (DoS) JVNDB-2022-002006
- CVSSv2 Severity Rating Scale
-
Level III (High)
- CVSSv2 Base Score
-
7.1
- CVSSv3 Severity Rating Scale
-
Medium
- CVSSv3 Base Score
-
5.5
- Date Public
-
2022/6/30
- Access Count
-
5,249
No.10 HOME SPOT CUBE2 vulnerable to OS command injection JVNDB-2022-000049
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
5.8
- CVSSv3 Severity Rating Scale
-
High
- CVSSv3 Base Score
-
8.8
- Date Public
-
2022/6/29
- Access Count
-
5,202
No.11 Privilege escalation vulnerability in Microsoft Windows Server JVNDB-2022-002007
- CVSSv2 Severity Rating Scale
-
- Level I (Low)
- CVSSv2 Base Score
-
2.1
- CVSSv3 Severity Rating Scale
-
- Medium
- CVSSv3 Base Score
-
5.3
- Date Public
-
2022/6/30
- Access Count
-
5,198
No.12 Multiple Microsoft Windows products vulnerable to remote code execution JVNDB-2022-001999
- CVSSv2 Severity Rating Scale
-
- Level II (Medium)
- CVSSv2 Base Score
-
5.1
- CVSSv3 Severity Rating Scale
-
High
- CVSSv3 Base Score
-
7.5
- Date Public
-
2022/6/30
- Access Count
-
5,157
No.12 Privilege escalation vulnerability in multiple Microsoft Windows products JVNDB-2022-002000
- CVSSv2 Severity Rating Scale
-
Level III (High)
- CVSSv2 Base Score
-
7.2
- CVSSv3 Severity Rating Scale
-
High
- CVSSv3 Base Score
-
7.8
- Date Public
-
2022/6/30
- Access Count
-
5,157
No.14 Multiple Microsoft Windows products vulnerable to remote code execution JVNDB-2022-001997
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
5.1
- CVSSv3 Severity Rating Scale
-
High
- CVSSv3 Base Score
-
7.5
- Date Public
-
2022/6/30
- Access Count
-
5,150
No.15 Microsoft SQL Server vulnerable to remote code execution JVNDB-2022-001974
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
6.0
- CVSSv3 Severity Rating Scale
-
High
- CVSSv3 Base Score
-
7.5
- Date Public
-
2022/6/30
- Access Count
-
5,140
No.16 Privilege escalation vulnerability in multiple Microsoft Windows products JVNDB-2022-002002
- CVSSv2 Severity Rating Scale
-
- Level II (Medium)
- CVSSv2 Base Score
-
4.4
- CVSSv3 Severity Rating Scale
-
- High
- CVSSv3 Base Score
-
7.0
- Date Public
-
2022/6/30
- Access Count
-
5,132
No.17 Privilege escalation vulnerability in multiple Microsoft Windows products JVNDB-2022-002001
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
6.8
- CVSSv3 Severity Rating Scale
-
High
- CVSSv3 Base Score
-
8.1
- Date Public
-
2022/6/30
- Access Count
-
5,125
No.18 Multiple Microsoft Windows products vulnerable to remote code execution JVNDB-2022-001998
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
6.0
- CVSSv3 Severity Rating Scale
-
High
- CVSSv3 Base Score
-
8.1
- Date Public
-
2022/6/30
- Access Count
-
5,122
No.19 Microsoft SharePoint Server vulnerable to remote code execution JVNDB-2022-002005
- CVSSv2 Severity Rating Scale
-
Level II (Medium)
- CVSSv2 Base Score
-
6.5
- CVSSv3 Severity Rating Scale
-
High
- CVSSv3 Base Score
-
8.8
- Date Public
-
2022/6/30
- Access Count
-
5,082
No.20 Improper input validation in FreeRDP JVNDB-2021-010460
- CVSSv2 Severity Rating Scale
-
Level III (High)
- CVSSv2 Base Score
-
7.5
- CVSSv3 Severity Rating Scale
-
Critical
- CVSSv3 Base Score
-
9.8
- Date Public
-
2022/7/1
- Access Count
-
5,065
Table 3-2 lists the top 5 most accessed vulnerability information among those reported by domestic product developers.
Table 3-2. Top 5 Most Accessed Vulnerabilities Reported by Domestic Product Developers [Jul. - Sep. 2022]
Table 3-2. Top 5 Most Accessed Vulnerabilities Reported by Domestic Product Developers [Jul. - Sep. 2022]
No.1 Information Disclosure Vulnerability in Hitachi Automation Director and Hitachi Ops Center Automator JVNDB-2022-002143
- Information Disclosure Vulnerability in Hitachi Automation Director and Hitachi Ops Center Automator
- CVSSv2 Base Score
-
- -
- CVSSv3 Base Score
-
- -
- Date Public
-
2022/8/1
- Access Count
-
3,657
No.2 Cross-site Scripting Vulnerability in JP1/IT Desktop Management 2 JVNDB-2022-001299
- CVSSv2 Base Score
-
- -
- CVSSv3 Base Score
-
-
- Date Public
-
2022/2/8
- Access Count
-
3,516
No.3 File Permission Vulnerability in Hitachi Command Suite JVNDB-2022-001382
- CVSSv2 Base Score
-
-
- CVSSv3 Base Score
-
-
- Date Public
-
2022/3/7
- Access Count
-
3,430
No.4 Directory Permission Vulnerability in Hitachi Ops Center Viewpoint JVNDB-2022-001383
- CVSSv2 Base Score
-
-
- CVSSv3 Base Score
-
-
- Date Public
-
2022/3/7
- Access Count
-
3,402
No.5 Multiple Vulnerabilities in JP1/Automatic Operation JVNDB-2021-004432
- CVSSv2 Base Score
-
-
- CVSSv3 Base Score
-
-
- Date Public
-
2021/11/22
- Access Count
-
3,366
Footnotes
(1) Japan Vulnerability Notes: A portal for vulnerability countermeasure information including information on vendor response to the reported vulnerabilities and security support. Operated in the collaboration of IPA and JPCERT/CC.
(2) National Vulnerability Database: A vulnerability database operated by NIST.
(3) National Institute of Standards and Technology: A U.S federal agency that develops and promotes measurement, standards and technology.
(4) Vulnerability Countermeasure Guide for Software Developers (in Japanese only )
(5) How to Secure Your Websites (latest version in Japanese only )
(6) Secure Programming Guide (in Japanese only)
(7) AppGoat (in Japanese only)
(8) IPA Data Feeds (in Japanese only)
(9) IPA Technical Watch - Daily Practice Guide (in Japanese only): Tips on Vulnerability Management
The guide gives tips on how to efficiently and efficiently collect and leverage vulnerability information.
Past Quarterly Reports
Contact information
IT Security Center,
Information-technology Promotion Agency, Japan (ISEC/IPA)